Beruflich Dokumente
Kultur Dokumente
Cyber Security Short Question
Hochgeladen von
Dharmanshu Mer0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
86 Ansichten4 SeitenCyber security is the protection of internet-connected systems, including hardware, software and data, from cyber attacks. It involves protecting networks, computers, programs and data from unauthorized access, destruction or manipulation. Some key aspects of cyber security covered are network security vs cyber security, vulnerabilities, ports, tools like Nmap, openVAS, metasploit, firewalls, intrusion detection and prevention systems, cyber crimes, hacking, malware, encryption, ethical hacking and recent trends. Cyber security also encompasses recovery from cyber incidents like restoring systems and data that have been compromised or damaged.
Originalbeschreibung:
CYBER SECURITY IMP
Copyright
© © All Rights Reserved
Verfügbare Formate
PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCyber security is the protection of internet-connected systems, including hardware, software and data, from cyber attacks. It involves protecting networks, computers, programs and data from unauthorized access, destruction or manipulation. Some key aspects of cyber security covered are network security vs cyber security, vulnerabilities, ports, tools like Nmap, openVAS, metasploit, firewalls, intrusion detection and prevention systems, cyber crimes, hacking, malware, encryption, ethical hacking and recent trends. Cyber security also encompasses recovery from cyber incidents like restoring systems and data that have been compromised or damaged.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
86 Ansichten4 SeitenCyber Security Short Question
Hochgeladen von
Dharmanshu MerCyber security is the protection of internet-connected systems, including hardware, software and data, from cyber attacks. It involves protecting networks, computers, programs and data from unauthorized access, destruction or manipulation. Some key aspects of cyber security covered are network security vs cyber security, vulnerabilities, ports, tools like Nmap, openVAS, metasploit, firewalls, intrusion detection and prevention systems, cyber crimes, hacking, malware, encryption, ethical hacking and recent trends. Cyber security also encompasses recovery from cyber incidents like restoring systems and data that have been compromised or damaged.
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 4
CYBER SECURITY SHORT QUESTION
1) What is Cyber Security?
2) What do you mean by cyber?
3) What is security?
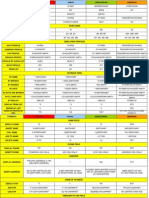
4) Difference between network security and Cyber security.
5) What is vulnerability?
6) What do you mean by port?
7) Full form of openVAS and use of openVAS tool.
8) Use of metasploit.
9) Full form of NMAP and Working of NMAP
10) Use of wireshark.
11) What do you mean by network?
12) What is sniffer?
13) What is network sniffer?
14) What is firewall? Use of firewall?
15) Types of firewalls
16) Full form of VPN and use of VPN
17) Full form of Netcat and use of it.
18) What is network injection?
19) Difference between packet filter vs firewall.
20) What do you mean by traffic probe?
21) What is banner grabbing?
22) Difference between stateless and statefull
23) Full form NAT and its use.
24) What is snort?
25) Difference between linux firewall and windows firewall
26) What do you mean intrusion?
27) What is intrusion detection system?
28) What is intrusion prevention system?
29) Types of intrusion detection system
30) Full form of DVWA and its use.
31) What is brute force attack? How it performs.
32) Platform for DVWA tool.
33) What is cyber crime?
34) Types of cyber crime
35) Types of hacking.
36) What is hacker?
37) Types of Hackers
38) What is Attack?
39) Types of attack.
40) Which os is mostly used in hacking and why?
41) What is cyber space?
42) What is incident response?
43) What is digital forensics?
44) What is computer forensics?
45) Difference between digital forensics and computer forensics
46) Difference between computer language and network language
47) What is internet?
48) What is intranet?
49) What is extranet?
50) Difference between internet, intranet and extranet
51) What is destruction of data?
52) What is password cracking?
53) Techniques of password cracking?
54) What is keylogger?
55) Work of keylogger
56) Types of keylogger?
57) What is spyware?
58) What is virus?
59) Which is self replicated virus or warm?
60) What is warms?
61) Difference between viruses and warms.
62) What is malware?
63) Types of malware.
64) What is Adware?
65) What is crimeware?
66) What is anti-virus? How it works?
67) What is Trojans?
68) What is backdoors?
69) What do you mean by steganography?
70) Full form of DOS and DDOS attack
71) Difference between DOS and DDOS attack
72) What is SQL injection?
73) What is buffer overflow?
74) Attack on wireless network
75) How firewalls protect a network?
76) Indian IT act 2000.
77) Commands explanation of manual and basic commands.
78) Real time examples of crimes.
79) Name of Top Indian hacker.
80) What are the principles of security?
81) Full form of TCP, UDP and HTTP, WWW.
82) What is ethical hacking?
83) how can you Recognize and Define Computer Crime
84) Tcpdump and Windump, Wireshark, Ettercap, Hping Kismet use for ?
85) Explain risk, vulnerability and threat.
86) What is encryption and what is the difference between Asymmetric and
Symmetric encryption and which one is better?
87) What is a firewall and how do you keep yourself updated with the
information security news.
88) What is an IPS and how does it differs from IDS?
89) What is vulnerability scanning, Traffic Probe, Vulnerability Probe,
OpenVAS, Metasploit.
90) Explain Networks Vulnerability Scanning tools.
91) Purpose and use of Netcat, Socat and Nmap.
92) What are the Port and Services tools.
93) Datapipe, Fpipe, WinRelay tools used for ?
94) what is steganography?
95) Define Cryptojacking and Ransomware.
96) What is momo watsapp challenge?
97) Password cracking tools(Any 10)
98) How many passwords can a computer guess per second?
99) Recent trends in cyber security
Das könnte Ihnen auch gefallen
- Cyber Security - Network Intrusion Case StudyDokument9 SeitenCyber Security - Network Intrusion Case Studysaby aroraNoch keine Bewertungen
- Cyber Securiy PPT Unit 1Dokument93 SeitenCyber Securiy PPT Unit 1chandana kiranNoch keine Bewertungen
- Cyber Threats and SecurityDokument17 SeitenCyber Threats and Securityno OneNoch keine Bewertungen
- 2nd Year Cyber Security NotesDokument3 Seiten2nd Year Cyber Security NotespriyankaNoch keine Bewertungen
- Cyber threat intelligence A Complete Guide - 2019 EditionVon EverandCyber threat intelligence A Complete Guide - 2019 EditionNoch keine Bewertungen
- Seminar On Ip SpoofingDokument27 SeitenSeminar On Ip SpoofingVenkatesh RajaNoch keine Bewertungen
- Datapro Computers: Seminar On Ethical HackingDokument26 SeitenDatapro Computers: Seminar On Ethical Hackingmuna cliffNoch keine Bewertungen
- Cyber Security All QuestionsDokument22 SeitenCyber Security All Questionsom chavanNoch keine Bewertungen
- Cyber Threat Hunting A Complete Guide - 2019 EditionVon EverandCyber Threat Hunting A Complete Guide - 2019 EditionNoch keine Bewertungen
- Cyber SecurityDokument48 SeitenCyber SecuritySuraj DasNoch keine Bewertungen
- Cyber-Attacks and Cybersecurity The Pressing Need For The LatterDokument4 SeitenCyber-Attacks and Cybersecurity The Pressing Need For The LatterInternational Journal of Innovative Science and Research TechnologyNoch keine Bewertungen
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookVon EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNoch keine Bewertungen
- Web Application Security Standard PDFDokument5 SeitenWeb Application Security Standard PDFyshprasdNoch keine Bewertungen
- CEH v5 Module 01 Introduction To Ethical HackingDokument43 SeitenCEH v5 Module 01 Introduction To Ethical HackingNghia Tran VanNoch keine Bewertungen
- Cyber Security in AfricaDokument5 SeitenCyber Security in AfricaBlack Hat HackerNoch keine Bewertungen
- Introduction To Ethical Hacking - Foot Printing and Reconnaissance - Scanning Networks - Enumeration - System Hacking - Malware Threats - SniffingDokument40 SeitenIntroduction To Ethical Hacking - Foot Printing and Reconnaissance - Scanning Networks - Enumeration - System Hacking - Malware Threats - Sniffingjaya prasanna100% (1)
- Cyber Security: Mrs. V. NikithaDokument78 SeitenCyber Security: Mrs. V. Nikithanikitha veeramallaNoch keine Bewertungen
- Cyber Safety PP Presentation For Class 11Dokument16 SeitenCyber Safety PP Presentation For Class 11WAZ CHANNEL100% (1)
- Cyber Security-MinDokument73 SeitenCyber Security-MinRajendra Kumar VermaNoch keine Bewertungen
- CYBERSECURITYDokument22 SeitenCYBERSECURITYmichellebulgar0Noch keine Bewertungen
- Unit-3 Lesson 4 Cyber SecurityDokument15 SeitenUnit-3 Lesson 4 Cyber Securitysreeharirpillai0805Noch keine Bewertungen
- UNIT - V: Cybercrimes and Cyber SecurityDokument11 SeitenUNIT - V: Cybercrimes and Cyber SecurityjaiNoch keine Bewertungen
- SOC Interview QuestionsDokument5 SeitenSOC Interview Questionsphishing ltaNoch keine Bewertungen
- Kyrion Ethical Hacking Workshop Handouts PDFDokument43 SeitenKyrion Ethical Hacking Workshop Handouts PDFKaran MehtaNoch keine Bewertungen
- Active and Passive AttackDokument21 SeitenActive and Passive Attackmangesh chaurasiaNoch keine Bewertungen
- The Cybercrimes Act, 2015 (Tanzania)Dokument54 SeitenThe Cybercrimes Act, 2015 (Tanzania)Evarist Chahali100% (2)
- (Class Note) Module 1 - Introduction To CybersecurityDokument79 Seiten(Class Note) Module 1 - Introduction To CybersecurityYao Xia LiNoch keine Bewertungen
- Chapter 4Dokument30 SeitenChapter 4Fazal KarimNoch keine Bewertungen
- SQL SynopsisDokument8 SeitenSQL SynopsisAnthati KumarNoch keine Bewertungen
- Network AttackDokument84 SeitenNetwork Attackaarthi devNoch keine Bewertungen
- Chapter 1: Introduction 1.1.2 Internet of Things (Iot) : Basic ConceptDokument29 SeitenChapter 1: Introduction 1.1.2 Internet of Things (Iot) : Basic ConceptJpsworldNoch keine Bewertungen
- Cyber Security UNIT-3Dokument58 SeitenCyber Security UNIT-3Dhananjay SinghNoch keine Bewertungen
- Cyber Kill ChainDokument4 SeitenCyber Kill ChainAbhi NairNoch keine Bewertungen
- Information Security PracticalDokument21 SeitenInformation Security PracticalDeepak Kumar Rajak67% (6)
- A Project Report On: Website Penetration Testing: Electronics and Communication EngineeringDokument22 SeitenA Project Report On: Website Penetration Testing: Electronics and Communication EngineeringSreehari YermalNoch keine Bewertungen
- Information Technology: Submitted To Devendra KohliDokument15 SeitenInformation Technology: Submitted To Devendra KohliAbhirup UbaleNoch keine Bewertungen
- Principles of Information SecurityDokument23 SeitenPrinciples of Information SecurityVinu VithuNoch keine Bewertungen
- A Presentation On Ethical HackingDokument30 SeitenA Presentation On Ethical Hackingʚĩɞ IkRàm AkCha ʚĩɞ100% (1)
- Mobile Application Security Penetration Testing BaDokument13 SeitenMobile Application Security Penetration Testing BaVenkatNoch keine Bewertungen
- Lab Report OF: by Anish Ghimire (7142)Dokument29 SeitenLab Report OF: by Anish Ghimire (7142)Nischal BhattaNoch keine Bewertungen
- Chapter 3 Encryption Principles and AlgorithmsDokument25 SeitenChapter 3 Encryption Principles and AlgorithmsHiziki TareNoch keine Bewertungen
- Unit 3 CYBER SECURITY (AUC-002)Dokument15 SeitenUnit 3 CYBER SECURITY (AUC-002)PrachiNoch keine Bewertungen
- Sample Exam QuestionsDokument6 SeitenSample Exam QuestionsAnonymous njwTvCNoch keine Bewertungen
- Network SecurityDokument17 SeitenNetwork SecurityJp CasabonNoch keine Bewertungen
- Chapter 8 - Cyber SecurityDokument23 SeitenChapter 8 - Cyber SecurityAnurag Parate100% (2)
- CEH Sample Questions - Vamsi Krishna PDFDokument7 SeitenCEH Sample Questions - Vamsi Krishna PDFvamsi krishnaNoch keine Bewertungen
- Denial of ServiceDokument18 SeitenDenial of ServiceAbhishek PandyaNoch keine Bewertungen
- Exploit Attack: Shaunak Joshi (Roll No:43162)Dokument7 SeitenExploit Attack: Shaunak Joshi (Roll No:43162)Shaunak JoshiNoch keine Bewertungen
- Chapter 1 - Cyber SecurityDokument20 SeitenChapter 1 - Cyber SecurityAnurag Parate100% (1)
- Ip Spoofing ABSTRACTDokument1 SeiteIp Spoofing ABSTRACTSreeprada Veerubhotla100% (1)
- Cybersecurity WebinarDokument27 SeitenCybersecurity Webinarcarl collinsNoch keine Bewertungen
- Cyber - Security Unit - 1Dokument61 SeitenCyber - Security Unit - 1regina100% (2)
- Cyber Security - I.ravi KumarDokument38 SeitenCyber Security - I.ravi KumarMr. RAVI KUMAR INoch keine Bewertungen
- Artificial Intelligence in Cyber SecuritDokument5 SeitenArtificial Intelligence in Cyber SecuritPiyush KunwarNoch keine Bewertungen
- Anti Phishing AttacksDokument58 SeitenAnti Phishing AttacksSneha Gupta0% (1)
- Ip Spoofing Seminar ReportDokument38 SeitenIp Spoofing Seminar ReportVishnu RaviNoch keine Bewertungen
- Comprehensive Review On CNN-based Malware Detection With Hybrid Optimization AlgorithmDokument13 SeitenComprehensive Review On CNN-based Malware Detection With Hybrid Optimization Algorithmارشی کماریNoch keine Bewertungen
- Analyzing and Implementing of Network Penetration TestingDokument48 SeitenAnalyzing and Implementing of Network Penetration TestingEngr. Md Yusuf MiahNoch keine Bewertungen
- Presentation Legal IssuesDokument9 SeitenPresentation Legal IssuesxcygonNoch keine Bewertungen
- Cyber Security: Mrs. V. NikithaDokument78 SeitenCyber Security: Mrs. V. Nikithanikitha veeramallaNoch keine Bewertungen
- PEAC Data Privacy Notice For The 2019 Philippine Education ConferenceDokument2 SeitenPEAC Data Privacy Notice For The 2019 Philippine Education ConferenceResel O. GalloNoch keine Bewertungen
- Cyber Security Training ContentDokument4 SeitenCyber Security Training ContentPrashant ZambreNoch keine Bewertungen
- Ibaba East - DecDokument30 SeitenIbaba East - DecAngelika CalingasanNoch keine Bewertungen
- IAPP Privacy Certification Glossary v2.0.0.2Dokument99 SeitenIAPP Privacy Certification Glossary v2.0.0.2Jerry Serapion100% (1)
- Acfe Malaysia Application FormDokument2 SeitenAcfe Malaysia Application FormUmmu AhmadNoch keine Bewertungen
- PDF Ebook Filsafat Fahrudin Faiz PDF Ruangbacaan DLDokument38 SeitenPDF Ebook Filsafat Fahrudin Faiz PDF Ruangbacaan DLToto TotelesNoch keine Bewertungen
- VisitorRegistrationForm - 23 Mac 2022Dokument1 SeiteVisitorRegistrationForm - 23 Mac 2022FaXmEeNoch keine Bewertungen
- Unit-5 (Cyber Security)Dokument4 SeitenUnit-5 (Cyber Security)tinime3820Noch keine Bewertungen
- PDF Actividad 4 Taller Generalidades Del Sistema TributarioDokument10 SeitenPDF Actividad 4 Taller Generalidades Del Sistema Tributarioliliana sernaNoch keine Bewertungen
- GDS All in One Conversion SheetDokument10 SeitenGDS All in One Conversion SheetAnca Dragan90% (10)
- 20akun Free FireDokument6 Seiten20akun Free Firewahyu mr. baooNoch keine Bewertungen
- Kritesh Dulawat - Undergraduate Architecture Portfolio 2015-20Dokument23 SeitenKritesh Dulawat - Undergraduate Architecture Portfolio 2015-20Athif JohnyNoch keine Bewertungen
- Shared TextDokument32 SeitenShared TextAna FunkyNoch keine Bewertungen
- Reflection Paper in Living in The It EraDokument1 SeiteReflection Paper in Living in The It Eraadrian nakilaNoch keine Bewertungen
- Types of CybercrimesDokument28 SeitenTypes of Cybercrimesmarry joy AlobaNoch keine Bewertungen
- Importance of CybersecurityDokument8 SeitenImportance of CybersecurityAnonymous CwJeBCAXpNoch keine Bewertungen
- Joomla VulnsDokument35 SeitenJoomla VulnsMksdm KlkliiNoch keine Bewertungen
- CONSENT PRIVACY NOTICE Form NNDokument2 SeitenCONSENT PRIVACY NOTICE Form NNAprilyn Galvizo MorandanteNoch keine Bewertungen
- Syllabus Information & Cyber Security WorkshopDokument1 SeiteSyllabus Information & Cyber Security Workshopjody dyandraNoch keine Bewertungen
- Personal Information Protection Law (PIPL)Dokument2 SeitenPersonal Information Protection Law (PIPL)Kedar BhasmeNoch keine Bewertungen
- Technical Seminar: On Cyber SecurityDokument18 SeitenTechnical Seminar: On Cyber Securityyasaswi sonyNoch keine Bewertungen
- Tawara Yacht BrokersDokument8 SeitenTawara Yacht BrokersDian Puspita SariNoch keine Bewertungen
- Nikhil Aryal: Roshan Sapkota Aarya Dahal Kushal PoudelDokument12 SeitenNikhil Aryal: Roshan Sapkota Aarya Dahal Kushal PoudelKushal PoudelNoch keine Bewertungen
- Shop The 2CELLOS Official StoreDokument10 SeitenShop The 2CELLOS Official StoreLomon SamNoch keine Bewertungen
- NAG-IBA I.decDokument26 SeitenNAG-IBA I.decAngelika CalingasanNoch keine Bewertungen
- Grade 11 Lesson 3Dokument24 SeitenGrade 11 Lesson 3Riel FernandezNoch keine Bewertungen
- Voucher 12.05.21 PangkasDokument2 SeitenVoucher 12.05.21 PangkasAris SetiawanNoch keine Bewertungen
- Computer Crime Final Assessment Test AnswersDokument4 SeitenComputer Crime Final Assessment Test AnswersOmar HaibaNoch keine Bewertungen