Beruflich Dokumente
Kultur Dokumente
Cybersecurity-Incident-Response Joa Eng 0720
Hochgeladen von
Luis SosaOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Cybersecurity-Incident-Response Joa Eng 0720
Hochgeladen von
Luis SosaCopyright:
Verfügbare Formate
FEATURE
Cybersecurity Incident Response
Tabletop Exercises Using the Lego Serious Play Method
It is foolish to wait until an enterprise is in the midst to prevent failures and overcome challenges has
of a data breach to test its cybersecurity incident been recognized. Cybersecurity professionals need
response plan (CSIRP). How likely is it that the to acknowledge these shortcomings and explore
enterprise will know that a cyberattack is underway new mechanisms to manage them. The LSP
and be able to react appropriately? Are the method has proved to be one mechanism that
enterprise’s current policies and procedures enriches and improves cybersecurity incident
sufficient to effectively detect, respond to and response TTEs and reduces the risk of failure.
mitigate sophisticated cybersecurity incidents?
The Value of Tabletop Exercises
The use of tabletop exercises (TTEs) can help
answer these and other questions. TTEs are A TTE presents a realistic cybersecurity incident
designed to prepare for real cybersecurity incidents. scenario to which an enterprise must respond.
By conducting TTEs, an incident response team Participants in the exercise describe how they
increases its confidence in the validity of the would react during the incident, what tools they
enterprise’s CSIRP and the team’s ability to would use and what procedures they would follow.
execute it.1 At the end of the exercise, the enterprise can
determine where its incident response plans and
The Lego Serious Play (LSP) method can support, policies are working well, where there is room for
improve and strengthen the design, execution and improvement, and how it can refine its CSIRP
outcomes of the TTEs an enterprise uses to assess
the capabilities, effectiveness and maturity of its
CSIRP. TTEs help determine whether the current
CSIRP is able to detect, respond to and mitigate
incidents in a timely and successful manner. They
can also ascertain whether the right people are in
place, whether they are aware of and committed to
their duties during a real cybersecurity incident, and
whether they can execute the procedures correctly.
Although TTEs are based on recommended
methodologies, such as the US National Institute of
Standards and Technology (NIST) Special
Publication (SP) 800-84,2 the need to improve TTEs
Fabian Garzón, CISM, CRISC, GCIH
Has two decades of experience in the IT and information security consultancy services working in various roles including product
management, IT security operations engineer, cybersecurity incident management, Payment Card Industry Data Security Standard
(PCI DSS) implementation, cyberrisk management and, now, chief technology officer at Hackergame, Colombia. He can be reached
at fabian@hackergame.com or www.linkedin.com/in/r-fabian-gg/.
Gustavo Garzón, CISM, CRISC, PMP
Has more than 15 years of experience in technology and digital security areas as a consultant and team leader implementing
information technology projects in Latin America and now is the founder and chief executive officer at Hackergame. He was a
member of the development team for A Practical Guide to the Payment Card Industry Data Security Standard (PCI DSS). He can be
reached at gustavo@hackergame.com or www.linkedin.com/in/gustavogarzonr.
ISACA JOURNAL VOL 4 49
“
• Improve coordination between internal and
INCREASINGLY, CLIENTS, INSURERS, external teams, enterprises and entities.
AUDITORS AND REGULATORS REQUIRE • Increase awareness and understanding of
EVIDENCE OF PREPAREDNESS, AND THE hazards and the potential impact of hazards.
”
RESULTS OF A TTE CAN SATISFY THESE • Assess the capabilities of existing resources and
identify needed resources.
REQUIREMENTS.
moving forward. Increasingly, clients, insurers,
Methodology for Planning and
auditors and regulators require evidence of Performing Tabletop Exercises
preparedness, and the results of a TTE can satisfy TTEs must follow some widely accepted
these requirements. methodology or guide. NIST SP 800-84, for
example, focuses on TTEs and functional
A variety of standards, regulations and guides exercises.10 It can help enterprises design, develop,
related to cybersecurity incident response conduct and evaluate testing, training and exercise
recommends the testing of CSIRPs. Figure 1 events in an effort to assist personnel in preparing
provides a sampling of standards from NIST,3, 4 the for adverse situations involving IT.
Payment Card Industry Security Standards Council
(PCI SSC),5 the SANS Institute,6 the International TTEs are discussion-based exercises. Personnel
Organization for Standardization (ISO)/International meet in a classroom setting or in breakout groups to
Electrotechnical Commission (IEC)7 and ISACA®.8 discuss their roles during an emergency and their
responses to a particular crisis situation. A facilitator
The US Department of Homeland Security’s Ready presents a scenario and asks the participants
Campaign,9 designed to educate and empower questions related to the scenario, which initiates a
US citizens to prepare for, respond to and mitigate discussion of roles, responsibilities, coordination and
emergencies, summarizes the benefits and decision making. Figure 2 outlines the NIST SP 800-
outcomes of exercises to test response plans. They 84 methodology for conducting a TTE.
include the following:
• Identify planning and procedural deficiencies. Failures and Challenges of Tabletop
• Clarify roles and responsibilities.
Exercises
TTEs are not exempt from weaknesses and
• Obtain participant feedback and
discouraging results.11 Disengaged staff, low
recommendations for program improvement.
attendance, inattention during the exercise and
• Measure improvement compared to other failures have been identified. They include
performance objectives. the following:
Figure 1—Cybersecurity Incident Response Guidelines
Standard Requirement/Recommendation
NIST SP 800-53 Requires US federal agencies to conduct exercises or tests for their incident
response capabilities at least annually
NIST SP 800-61 Requires that the incident response policy, plan and procedures be tested to
validate their accuracy and usefulness
PCI Data Security Standard (DSS) 3.2 Requires the implementation of an incident response plan, including a review
and test of the plan at least annually
SANS Institute Recommends drills at regular intervals to ensure that all individuals on the
incident response team can perform their duties during an incident
ISO/IEC 27035 Recommends periodic tests of the information security incident management
scheme
ISACA® Recommends comprehensive exercises that involve all key factors:
communications, coordination, resource availability and response
50 ISACA JOURNAL VOL 4
Figure 2—NIST SP 800-84 TTE Methodology • Distractions—If TTE participants divide their
attention between their electronic devices and
Design—Phase 1 the exercise—multitasking—neither activity gets
Establish teams and the benefit of the brain’s full resources, and
scope the TTE event.
participants are likely to miss important details
of the cybersecurity scenario.12
Evaluation—Phase 4 Development—Phase 2 This list of failures and challenges is not all-
Document lessons Develop all documentation inclusive, but these shortcomings have been
learned from the necessary for the conduct
event. of the TTE event. highlighted because LSP addresses them directly.
Game-Based Learning and Gamification
Conduct—Phase 3
Conduct the
Because many of the failures of TTEs are related to
TTE event. interest, interaction, engagement and participation,
creative solutions are needed, and this is where
game-based learning and gamification can help.
• Lack of clear and achievable objectives—Do not An example of game-based learning applied to
overcomplicate the objectives of the TTE, and TTEs is Backdoors & Breaches, an incident
make sure they are achievable. response card game that is simple in concept,
easy to play and fun.13
• Irrelevance—The value of a TTE is the
opportunity to discuss individual interests Gamification is the craft of deriving fun and engaging
(related to areas or roles) and to explore new and elements found typically in games and thoughtfully
unforeseen issues. applying them to real-world or productive activities.
• Tedium—TTEs are a means to expand the scope Game mechanics such as points, challenges,
of an enterprise’s human, process and leaderboards, rules and incentives make game-play
technology assets. For some individuals, the enjoyable. Gamification applies these mechanics to
prospect of a TTE meeting may not be exciting, motivate the audience to achieve higher and more
so it is important to make the exercises meaningful levels of engagement.14
interesting.
Many enterprises have experimented with
• Boring scenarios—The TTE scenario should gamification to improve end-user awareness. The
ensure that all the participants are engaged. results have been remarkable.15 Games have the
Maintaining their interest in the conversation ability to disarm people, negating their natural
throughout the session can be difficult, but it can aversion to meetings because games make them fun,
be accomplished by including issues that are and most games are associated with the chance to
specific to the participants’ areas of responsibility. win. Although using games to increase people’s
• Lack of visual appeal—Pictures, short videos, engagement with work may seem counterintuitive,
manipulated images, simulated news and social game playing appears to be paying off in the areas of
media messages can create realism and keep cybersecurity awareness, incident response exercises
participants engaged. Failure to present a and cybersecurity skills development.
visually stimulating experience will result in less
interaction and more disengagement. Lego Serious Play Method
• Exercises that are too challenging or not In the search for innovative and proven methods of
challenging enough—Achieving the right balance game-based learning that can be used without any
can be difficult. If scenarios go too far, restrictions in the development and execution of TTEs
participants may be overwhelmed by the various and can mitigate the failures described previously,
problems presented to them. This can lead to a LSP is an obvious choice. In simple terms, LSP is a
reduction in active participation during the TTE. systematic method that enables people to use Lego
The same is true for a scenario that is too easy bricks to solve problems, explore ideas and achieve
to handle and does not test the team. objectives.16 Lego bricks are combined with animals,
ISACA JOURNAL VOL 4 51
“
traditional failures of TTEs were reduced. The
LSP...IS A CREATIVE APPROACH TO following are some of the positive outcomes:
ENHANCING INNOVATION AND IMPROVING • Everyone involved in the TTE has an interest or
”
BUSINESS PERFORMANCE, WITH THE FOCUS stake in the agenda.
ON UNLEASHING PLAY. • Everyone commits to and honors decisions
reached after the TTE.
miniature figures and an extensive selection of special
• Team understanding is increased, and team
frustration is decreased.
elements such as wheels, tires, windows, trees, sticks,
globes, spiral tubes, ladders and fences. Figure 3 • Participants do not consider the exercises a
shows models built with Lego pieces during an waste of time.
LSP exercise.
• All participants share a common understanding
and frame of reference (CSIRP in place).
If participants’ hands are occupied with Lego pieces,
one failure of TTEs—distraction—is already • Conversations flow without the fear of treading
diminished. But LSP is much more than building on personal feelings.
models. It is a creative approach to enhancing
innovation and improving business performance, with
• Cybersecurity incident response can be complex
and multifaceted. TTEs using LSP help participants
the focus on unleashing play. Based on the merging
grasp the bigger picture, find connections, and
of play with organizational development, systems
explore options and potential solutions.
thinking and strategy development, LSP can lead to
improved meetings, faster innovation processes, • Participants acquire the skills to communicate
team growth and better communication.17 more effectively when a cybersecurity incident
happens and approach their work with increased
The purpose of LSP is to change “lean backward confidence and commitment.
meetings” to “lean forward meetings,”18 where the
result is more participation, more insights, more
• There is a level playing field for discussion.
engagement, and, ultimately, more commitment • Excuses and lack of initiative are less common
and faster implementation. In several TTEs after the TTE.
executed with LSP in Latin America in 2019, the
Figure 3—Lego Models
52 ISACA JOURNAL VOL 4
What are the practical applications of the LSP cross-functional relationships within the enterprise
method? Many case studies have been (e.g., legal, IT, human resources, public relations) and
documented.19 Effective team building; shared decreases the resistance to performing cross-
vision, values and behaviors; and the development functional TTEs. Modifying Lego models is analogous
of workshops are some of the practical examples. to manipulating elements in a system, network or
Depending on the challenge (the incident scenario process in a simulated incident scenario. The
in the TTE), the LSP method has seven application participants explore “what if” questions (injecting new
techniques (figure 4), all of which are built on four elements into cybersecurity scenarios) and how
core phases (figure 5).20 these elements can impact the results of their
response. By observing connections among Lego
Figure 4—Applications Techniques of LSP model systems and by playing “what if,” participants
Applications Techniques are able to identify the underlying truths that will
guide them through real cybersecurity incidents in
Building individual models
the future.
Building shared models
Creating a landscape Conclusion
Making connections
A number of efforts can advance an enterprise’s
Building a system CSIRP, including the development of TTEs that are
Playing emergence and decisions fun, engaging and interactive. Lego Serious Play can
Extracting simple guiding principles be an important tool in a cybersecurity incident
response TTE.
Figure 5—Basic Phases of LSP
When planning a TTE, remember that people tend to
Basic Phases be more engaged when the subject matter is
1. Facilitator poses the questions pertinent, fun, appealing and challenging. It is
2. Individuals build a model important to test the CSIRP and the incident response
team as often as possible with different scenarios,
3. Individuals share their stories
different exercises and different mechanisms.
4. Questions and reflections
Enterprises are strongly encouraged to adapt LSP is not just for incident response TTEs. Once
scenarios to use in their own incident response cybersecurity professionals understand and have
exercises. For TTEs executed with LSP, sample practiced and tested the LSP method, they can use
scenarios can be found in the Center for Internet it for other types of workshops, including security
Security (CIS) guide21 or appendix A of NIST SP 800- awareness, skill building, team building,
61.22 If an enterprise wants to simulate incidents cybersecurity program goal setting, cybersecurity
using cloud-based services, Amazon Web Services behavior modification and cultural activities within
(AWS) provides sample scenarios.23 the community, enterprise, workplace and home.
During TTEs applying the LSP method in Colombia’s Endnotes
financial enterprises, it was observed that 1 Markey, S.; “Testing Your Computer Security
participants with shared Lego models demonstrated Incident Response Plan,” ISACA® Journal, vol. 2,
a team understanding of a cyberattack, its impact and 2012, www.isaca.org/Journal/archives
the step-by-step incident response.24, 25 They had a 2 National Institute of Standards and Technology
shared vision of the response strategy and how to (NIST), “Guide to Test, Training, and Exercise
mitigate the simulated cybersecurity incident. Programs for IT Plans and Capabilities,”
Participants can make physical connections between Special Publication (SP) 800-84, USA, 2006,
various Lego models to demonstrate how they are https://csrc.nist.gov/publications/detail/
related; this helps them solve problems involving sp/800-84/final
ISACA JOURNAL VOL 4 53
3 National Institute of Standards and Technology, 14 Chou, Y.; Actionable Gamification—Beyond
“Security and Privacy Controls for Federal Points, Badges, and Leaderboard, Octalysis
Enjoying
Information Systems and Organizations,” Media, USA, 2017
this article? SP 800-53, rev. 4, USA, 2013, https://nvd. 15 Bedell, C.; “Play On: How Gamification Can
nist.gov/800-53 Improve Employee Cybersecurity Compliance,”
• Learn more 4 National Institute of Standards and Technology, Infosecurity Professional Magazine,
about, discuss “Computer Security Incident Handling Guide,” July/August 2019
and collaborate SP 800-61, rev. 2, USA, 2012, 16 Blair, S.; M. Rillo; “Serious Work: How to
on information https://nvlpubs.nist.gov/nistpubs/Special Facilitate Meetings and Workshops Using the
and cybersecurity Publications/NIST.SP.800-61r2.pdf Lego Serious Play Method,” 2016,
in ISACA’s Online 5 Payment Card Industry Security Standards https://b-ok.cc/book/3403461/887f78
Forums. Council (PCI SSC), Payment Card Industry Data 17 Kristiansen, P.; R. Rasmussen; Building a Better
https://engage. Security Standard (PCI DSS) 3.2.1, 2018, Business Using the Lego® Serious Play® Method,
isaca.org/online www.pcisecuritystandards.org/document_library Wiley, USA, 2014
forums 6 SANS Institute, “Incident Handler’s Handbook,” 18 Association of Master Trainers, “The Lego®
2012, www.sans.org/reading-room/whitepapers/ Serious Play® Method,” Serious Play, 2019,
incident/paper/33901 seriousplay.training/lego-serious-play/
7 International Organization for Standardization 19 Op cit Blair, Rillo
(ISO)/International Electrotechnical 20 Rillo, M.; “History: Copyright of Lego Serious
Commission (IEC), ISO/IEC 27035-2:2016, Play Methodology Process Elements,” Serious
“Security Techniques—Information Security Play Pro, 3 August 2018, seriousplaypro.com/
Incident Management—Part 2,” Switzerland, 2018/08/03/copyright-of-application-techniques-
2016, https://www.iso.org/standard/62071.html and-4-core-steps-of-the-lego-serious-play-process
8 ISACA®, Responding to Targeted Cyberattacks, 21 Center for Internet Security (CIS), “Six Tabletop
USA, 2013 Exercises Prepare Cybersecurity Team,” 2018,
9 US Department of Homeland Security, Ready www.cisecurity.org/white-papers/six-tabletop-
Campaign, 21 January 2016, www.ready.gov/ exercises-prepare-cybersecurity-team/
business/testing/exercises 22 Op cit NIST, 2012
10 Op cit NIST, 2006 23 Amazon Web Services (AWS), “AWS Security
11 Murray, M.; R. Lelewski; “Common Tabletop Incident Response Guide,” 2019,
Exercise Failures,” 31st Annual FIRST https://d1.awsstatic.com/whitepapers/
Conference, 2019, www.first.org/conference/ aws_security_incident_response.pdf
2019/program#pTop-Common-Tabletop- 24 HackerGame, “Taller de ciberseguridad con
Exercise-Failures Lego® Serious Play®—Cómo afrontar una Crisis
12 Etailinsights, “Why Multitasking Doesn’t Digital en tu empresa,” YouTube, 15 August
Actually Increase Productivity,” 2014, 2019, www.youtube.com/watch?v=ikQR0lLU9YY
www.etailinsights.com/blog/multitasking- 25 HackerGame, “Taller de ciberseguridad con
productivity Lego® Serious Play®—Cómo hacer que tus
13 Porup, J. M.; “Backdoors and Breaches: inversiones sean seguras,” YouTube, 15 August
Incident Response Card Game Makes 2019, www.youtube.com/watch?v=zHsRln_kH6k
Tabletop Exercises Fun,” CSO Online, 2020,
www.csoonline.com/article/3509467/
backdoors-and-breaches-incident-response-
card-game-makes-tabletop-exercises-fun.html
54 ISACA JOURNAL VOL 4
Das könnte Ihnen auch gefallen
- Lab 8Dokument3 SeitenLab 8U MinhNoch keine Bewertungen
- CISSP 8 Domains PDFDokument508 SeitenCISSP 8 Domains PDFEduardo Honorato100% (2)
- CISSP Note Finale 1Dokument93 SeitenCISSP Note Finale 1psenthil1100% (3)
- Hikvision DDNS Management System20130216Dokument8 SeitenHikvision DDNS Management System20130216Ankush TandonNoch keine Bewertungen
- Cism Exam Preparation: Domain 4Dokument52 SeitenCism Exam Preparation: Domain 4Alifia FithritamaNoch keine Bewertungen
- Business Continuity Plan Checklist PDFDokument2 SeitenBusiness Continuity Plan Checklist PDFkapil ajmaniNoch keine Bewertungen
- 29 Highly Influential CISOs JKHHFN PDFDokument45 Seiten29 Highly Influential CISOs JKHHFN PDFLuis Sosa100% (1)
- ThinkMo CCIE EI Lab v1.0 Module2 Section 1 Part2 Version 4.1 PDFDokument29 SeitenThinkMo CCIE EI Lab v1.0 Module2 Section 1 Part2 Version 4.1 PDFlawnz gardenzNoch keine Bewertungen
- PasswordsDokument5 SeitenPasswords739589asdalkom.liveNoch keine Bewertungen
- Financial Sector Cyber Exercise TemplateDokument22 SeitenFinancial Sector Cyber Exercise TemplateDavid DavidNoch keine Bewertungen
- ICAA5056ADokument8 SeitenICAA5056AyonasNoch keine Bewertungen
- Running Head: Discussion Questions 1Dokument6 SeitenRunning Head: Discussion Questions 1Mahantesh SpNoch keine Bewertungen
- BSBOPS504Dokument20 SeitenBSBOPS504Swastika ThapaNoch keine Bewertungen
- Top10 ConsiderationsForIncidentResponseDokument11 SeitenTop10 ConsiderationsForIncidentResponseClaudio Jose CastilloNoch keine Bewertungen
- ISC2 2 Incident Response, Business Continuity and Disaster Recovery ConceptsDokument13 SeitenISC2 2 Incident Response, Business Continuity and Disaster Recovery ConceptsAj Johnson100% (1)
- Cyber Security Lesson 4Dokument22 SeitenCyber Security Lesson 4Ushna AbrarNoch keine Bewertungen
- CybersecurityinLegislatures FINALDokument36 SeitenCybersecurityinLegislatures FINALSegun AdesinaNoch keine Bewertungen
- Resilience Task Force: Augmenting Crisis Response and Recovery CapabilitiesDokument7 SeitenResilience Task Force: Augmenting Crisis Response and Recovery Capabilitiesamaan khanNoch keine Bewertungen
- Formative Assess-1Dokument15 SeitenFormative Assess-1manpreet kaurNoch keine Bewertungen
- Lessons Learned From Implementing Best Practices in Risk Based Process SafetyDokument12 SeitenLessons Learned From Implementing Best Practices in Risk Based Process SafetyChimaovu EhoroNoch keine Bewertungen
- Arab Academy For Science, Technology and Maritime TransportDokument18 SeitenArab Academy For Science, Technology and Maritime TransportAmr FawzyNoch keine Bewertungen
- A Framework For Incident ResponseDokument65 SeitenA Framework For Incident ResponseVicente OrtizNoch keine Bewertungen
- Reviewer DawDokument13 SeitenReviewer DawMark GNoch keine Bewertungen
- Iso27001 Isaca Planning-For-And PDFDokument8 SeitenIso27001 Isaca Planning-For-And PDFKhusal PhogatNoch keine Bewertungen
- SANS Back To The Future What Will Endpoint IR Really Look LikeDokument12 SeitenSANS Back To The Future What Will Endpoint IR Really Look LikeSakuragiNoch keine Bewertungen
- Entrenamiento 8DDokument23 SeitenEntrenamiento 8DRene DurandNoch keine Bewertungen
- BCM Toolkit Guide Impact Analysis and ResourcesDokument23 SeitenBCM Toolkit Guide Impact Analysis and ResourcesDidane13Noch keine Bewertungen
- Stages of Incident Management: and How To Improve ThemDokument15 SeitenStages of Incident Management: and How To Improve ThemGuillaume M.Noch keine Bewertungen
- DLP Module 2 (Security Principles & Practices Solution)Dokument53 SeitenDLP Module 2 (Security Principles & Practices Solution)barfitakillaNoch keine Bewertungen
- Five Best Practices For Communicating Security Awareness Training ImpactDokument11 SeitenFive Best Practices For Communicating Security Awareness Training ImpactManixhome MmNoch keine Bewertungen
- Lab4-Le Quang Vu-SE160967-IA1702Dokument8 SeitenLab4-Le Quang Vu-SE160967-IA1702Le Quang Vu (K16HCM)Noch keine Bewertungen
- Coordinating Security Response and Crisis Management PlanningDokument5 SeitenCoordinating Security Response and Crisis Management PlanningadinaNoch keine Bewertungen
- Materi 2-Webinar 5 PAKKEM-Ibu ElviraDokument18 SeitenMateri 2-Webinar 5 PAKKEM-Ibu ElviraUlil Amrie ZaNoch keine Bewertungen
- Business Continuity and Disaster Recovery - EDUCAUSEDokument18 SeitenBusiness Continuity and Disaster Recovery - EDUCAUSENicholasFCheongNoch keine Bewertungen
- Securing Enterprises: Against Cyber DisastersDokument10 SeitenSecuring Enterprises: Against Cyber DisastersYansyah WijayaNoch keine Bewertungen
- All Csuite Cyber Cheat SheetDokument16 SeitenAll Csuite Cyber Cheat Sheetits hero timeNoch keine Bewertungen
- Incident Manager Capability MetricsDokument229 SeitenIncident Manager Capability MetricsrbrianrNoch keine Bewertungen
- ch-5 QADokument10 Seitench-5 QAbazezew belewNoch keine Bewertungen
- Kolej Vokasional Taiping: Batu 4, 34 600 KAMUNTING, Perak Darul RidzuanDokument20 SeitenKolej Vokasional Taiping: Batu 4, 34 600 KAMUNTING, Perak Darul RidzuanNadhirah JohaNoch keine Bewertungen
- CISM - 15e - Domain 4Dokument100 SeitenCISM - 15e - Domain 4neeldxtNoch keine Bewertungen
- 01 Laboratory Exercise 1Dokument3 Seiten01 Laboratory Exercise 1Jane Rose Clemeña GumbanNoch keine Bewertungen
- 1) Overview of The Cybersecurity FrameworkDokument4 Seiten1) Overview of The Cybersecurity FrameworkArunim AichNoch keine Bewertungen
- ICTCYS612 Student Assessment Tasks and Project Portfolio V2.0Dokument36 SeitenICTCYS612 Student Assessment Tasks and Project Portfolio V2.0akashpandet60% (1)
- Risk Based Process SafetyDokument5 SeitenRisk Based Process Safetymohamed_sahnoun_enisNoch keine Bewertungen
- Cyber Security Incident Response PlanDokument4 SeitenCyber Security Incident Response PlanxyzeeNoch keine Bewertungen
- Human Performance For Nuclear Leaders Training StandardDokument13 SeitenHuman Performance For Nuclear Leaders Training StandardEm GerNoch keine Bewertungen
- AUDITDokument7 SeitenAUDITErnest Kamrad BndNoch keine Bewertungen
- Nist CSFDokument7 SeitenNist CSFAmarendar ReddyNoch keine Bewertungen
- Section Ii.9 Identifying Training Needs and Planning TrainingDokument9 SeitenSection Ii.9 Identifying Training Needs and Planning TrainingRICH FXNoch keine Bewertungen
- Buisness Continuity and Disaster RecoveryDokument130 SeitenBuisness Continuity and Disaster RecoveryApoorv RajNoch keine Bewertungen
- Term Paper - Risk Management in IT ProjectsDokument26 SeitenTerm Paper - Risk Management in IT Projectsankur_saini_17100% (2)
- Seven Steps To Creating An Effective Computer Security Incident Response TeamDokument8 SeitenSeven Steps To Creating An Effective Computer Security Incident Response TeamMarcosArauco100% (1)
- Ls3 - Policies, Procedures, and Awareness: CIS240 - Lab ExperimentDokument6 SeitenLs3 - Policies, Procedures, and Awareness: CIS240 - Lab ExperimentleovaldanNoch keine Bewertungen
- Proceeding 2Dokument102 SeitenProceeding 2userscribd2011Noch keine Bewertungen
- Incident ManagementDokument18 SeitenIncident ManagementBalan Wv100% (1)
- Solution Manual For Systems Analysis and Design 7th Edition Alan DennisDokument37 SeitenSolution Manual For Systems Analysis and Design 7th Edition Alan Dennisquartinewapiti4nbf100% (16)
- Business Continuity Management FrameworkDokument11 SeitenBusiness Continuity Management FrameworkHema MaliniNoch keine Bewertungen
- ISC Process Safety Competency Guidance: Edition 2, 2018Dokument28 SeitenISC Process Safety Competency Guidance: Edition 2, 2018kokykarkarNoch keine Bewertungen
- White Paper - Defending InfrastructureDokument20 SeitenWhite Paper - Defending InfrastructureDan McClintockNoch keine Bewertungen
- IR Reference GuideDokument43 SeitenIR Reference Guidepnorberto100% (1)
- Question Text: 1. Commitment and Support From Top ManagementDokument5 SeitenQuestion Text: 1. Commitment and Support From Top ManagementOhms BrangueloNoch keine Bewertungen
- When Things Go Wrong - Nonconformities and IncidentsDokument4 SeitenWhen Things Go Wrong - Nonconformities and Incidentshridya dasNoch keine Bewertungen
- Performance Testing: An ISTQB Certified Tester Foundation Level Specialist Certification ReviewVon EverandPerformance Testing: An ISTQB Certified Tester Foundation Level Specialist Certification ReviewNoch keine Bewertungen
- Penetration Testing: A guide for business and IT managersVon EverandPenetration Testing: A guide for business and IT managersNoch keine Bewertungen
- Cyber Breach Response That Actually Works: Organizational Approach to Managing Residual RiskVon EverandCyber Breach Response That Actually Works: Organizational Approach to Managing Residual RiskNoch keine Bewertungen
- CompTIA CASP+ Certification The Ultimate Study Guide To Master the Advanced Security Practitioner ExamVon EverandCompTIA CASP+ Certification The Ultimate Study Guide To Master the Advanced Security Practitioner ExamNoch keine Bewertungen
- 2020 NACD Cyber Handbook WEB 022020Dokument77 Seiten2020 NACD Cyber Handbook WEB 022020Luis SosaNoch keine Bewertungen
- How To Sell Cyber Security To Your BoardDokument18 SeitenHow To Sell Cyber Security To Your BoardLuis SosaNoch keine Bewertungen
- Cissp Process Guide V.21: You Can Send Me A Donation To My Account To Keep This Document Updated: Paypal - Me/FadisodahDokument51 SeitenCissp Process Guide V.21: You Can Send Me A Donation To My Account To Keep This Document Updated: Paypal - Me/FadisodahLuis SosaNoch keine Bewertungen
- Cm-Al L I Ance. Com - I NF O@cm-Al L I Ance. Com - +44 (0) 203 189 1422Dokument1 SeiteCm-Al L I Ance. Com - I NF O@cm-Al L I Ance. Com - +44 (0) 203 189 1422Luis SosaNoch keine Bewertungen
- EY Security Operations Centers Helping You Get Ahead of Cybercrime PDFDokument20 SeitenEY Security Operations Centers Helping You Get Ahead of Cybercrime PDFLuis SosaNoch keine Bewertungen
- How Does It Work?: Thank You For Buying My G2A Method !Dokument8 SeitenHow Does It Work?: Thank You For Buying My G2A Method !DavidNoch keine Bewertungen
- Wireless Communication Systems Error Correction CodesDokument32 SeitenWireless Communication Systems Error Correction Codesnabeel hasanNoch keine Bewertungen
- Power Off Reset Reason BackupDokument5 SeitenPower Off Reset Reason BackupGermano SantanaNoch keine Bewertungen
- Lastexception 63829969309Dokument3 SeitenLastexception 63829969309Chen LilyNoch keine Bewertungen
- ICT Project Process PPTDokument23 SeitenICT Project Process PPTBurning RoseNoch keine Bewertungen
- S13 Key2roam Data Roaming Implementation GuidelineDokument17 SeitenS13 Key2roam Data Roaming Implementation GuidelineAnonymous SmYjg7g100% (1)
- LogDokument76 SeitenLogLenny SegubienseNoch keine Bewertungen
- 0 - Creating A Blog-WPS OfficeDokument11 Seiten0 - Creating A Blog-WPS OfficeMiguela SantosNoch keine Bewertungen
- Technical Note FORTIMAIL Configuration For Enterprise Deployment Rev 2.1Dokument11 SeitenTechnical Note FORTIMAIL Configuration For Enterprise Deployment Rev 2.1Pyae Sone TunNoch keine Bewertungen
- 24 - Single-Area OSPFv2 ConfigurationDokument60 Seiten24 - Single-Area OSPFv2 ConfigurationJana MassadehNoch keine Bewertungen
- Ziead Emad Ali: ExperienceDokument2 SeitenZiead Emad Ali: Experiencewani ahlamNoch keine Bewertungen
- Siemens: List of Mlfbs With HSN Code For PD Pa Ae Dcs ProductsDokument145 SeitenSiemens: List of Mlfbs With HSN Code For PD Pa Ae Dcs ProductsMaheshwar - Cnervis AutomationNoch keine Bewertungen
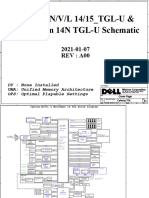
- Cyborg - TGL REVA00Dokument105 SeitenCyborg - TGL REVA00Warren DonaldsonNoch keine Bewertungen
- List of Registered Treatment, Storage and Disposal (TSD) FacilitiesDokument53 SeitenList of Registered Treatment, Storage and Disposal (TSD) FacilitiesRoland AlfaroNoch keine Bewertungen
- Hackforgov 2023: Event BrieferDokument9 SeitenHackforgov 2023: Event BrieferMichael Vincent DosadoNoch keine Bewertungen
- 336 Data Entry OperationsDokument18 Seiten336 Data Entry OperationsSuper GamingNoch keine Bewertungen
- Instructions For Online Bid Submission: Searching For Tender DocumentsDokument2 SeitenInstructions For Online Bid Submission: Searching For Tender DocumentsAmit GaragNoch keine Bewertungen
- Buku Saku SCNDokument81 SeitenBuku Saku SCNAndrie Purna FNoch keine Bewertungen
- CHAPTER 3 Lesson 2Dokument2 SeitenCHAPTER 3 Lesson 2Mariel BombitaNoch keine Bewertungen
- imageRUNNERFirmwareChart 1-7-2011Dokument3 SeitenimageRUNNERFirmwareChart 1-7-2011jesus maximilianoNoch keine Bewertungen
- CO2227U850 After Site Log 221104 1639Dokument16 SeitenCO2227U850 After Site Log 221104 1639Leonardo ezequiel Hernandez santosNoch keine Bewertungen
- Data 1Dokument8 SeitenData 1Pet PotNoch keine Bewertungen
- Free Onlyfans Hack 2021 - TN 81Dokument2 SeitenFree Onlyfans Hack 2021 - TN 81sarcastic chhokreyNoch keine Bewertungen
- Descriptive Text (To Share)Dokument6 SeitenDescriptive Text (To Share)Yusup BachtiarNoch keine Bewertungen
- Subra's PortfolioDokument3 SeitenSubra's PortfolioSubra SeNoch keine Bewertungen
- Internet of Things Approach To Cloud-Based Smart Car ParkingDokument16 SeitenInternet of Things Approach To Cloud-Based Smart Car ParkingAteek SahayNoch keine Bewertungen
- LogsDokument14 SeitenLogsMohini Umap0% (1)