Beruflich Dokumente
Kultur Dokumente
Syllabus of Cloud Computing and Plan
Hochgeladen von
onesnoneOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Syllabus of Cloud Computing and Plan
Hochgeladen von
onesnoneCopyright:
Verfügbare Formate
CODE: OEC-CS-702(II)
SUBJECT NAME: CLOUD COMPUTING
NO OF CREDITS: 3
B.TECH 7th SEMESTER SESSIONAL: 25
L TP THEORY EXAM: 75
3 0 0 TOTAL : 100
Course objectives: The student will learn how to apply
1. Trust-based security model to real-world security problems.
2. An overview of the concepts, processes, and best practices needed to successfully secure
information within Cloud infrastructures.
3. Students will learn the basic Cloud types and delivery models and develop an
understanding of the risk and compliance responsibilities and Challenges for each
Cloud type and service delivery model.
MODULE-1: INTRODUCTION TO CLOUD COMPUTING
Online Social Networks and Applications, Cloud introduction and overview, Different clouds,
Risks, Novel applications of cloud computing .
MODULE-2: CLOUD COMPUTING ARCHITECTURE
Requirements, Introduction Cloud computing architecture, On Demand Computing
Virtualization at the infrastructure level, Security in Cloud computing environments, CPU
Virtualization, A discussion on Hypervisors Storage Virtualization Cloud Computing Defined,
The SPI Framework for Cloud Computing, The Traditional Software Model, The Cloud Services
Delivery Model Cloud Deployment Models Key Drivers to Adopting the Cloud, The Impact of
Cloud Computing on Users, Governance in the Cloud, Barriers to Cloud Computing Adoption in
the Enterprise .
MODULE-3: SECURITY ISSUES IN CLOUD COMPUTING
Infrastructure Security, Infrastructure Security: The Network Level, The Host Level, The
Application Level, Data Security and Storage, Aspects of Data Security, Data Security
Mitigation Provider Data and Its Security Identity and Access Management Trust Boundaries
and IAM, IAM Challenges, Relevant IAM Standards and Protocols for Cloud Services, IAM
Practices in the Cloud, Cloud Authorization Management
MODULE-4: SECURITY MANAGEMENT IN THE CLOUD
Security Management Standards, Security Management in the Cloud, Availability Management:
SaaS, PaaS, IaaS Privacy Issues Privacy Issues, Data Life Cycle, Key Privacy Concerns in the
Cloud, Protecting Privacy, Changes to Privacy Risk Management and Compliance in Relation to
Cloud Computing, Legal and Regulatory Implications, U.S. Laws and Regulations, International
Laws and Regulations
MODULE-5: AUDIT AND COMPLIANCE
Internal Policy Compliance, Governance, Risk, and Compliance (GRC), Regulatory/External
Compliance, Cloud Security Alliance, Auditing the Cloud for Compliance, Security-as-a-Cloud.
MODULE-6: DATA INTENSIVE COMPUTING
Map-Reduce Programming Characterizing Data-Intensive Computations, Technologies for Data-
Intensive Computing, Storage Systems, Programming Platforms, MapReduce Programming,
MapReduce Programming Model, Example Application
Course Outcomes:
After completion of course, students would be able to:
1. Identify security aspects of each cloud model
2. Develop a risk-management strategy for moving to the Cloud
3. Implement a public cloud instance using a public cloud service provider
REFERENCES:
1. Gautam Shroff, “Enterprise Cloud Computing Technology Architecture Applications”,
Cambridge University Press; 1 edition, [ISBN: 978-0521137355], 2010.
2. Kai Hwang, Geoffrey C. Fox, Jack J. Dongarra, “Distributed and Cloud Computing:
From parallel processing to IOT” Morgan Kaufmann Publishers; 1 edition [ISBN: 978-0-
12-385880], 2012.
Das könnte Ihnen auch gefallen
- GTU Cloud Computing CourseDokument3 SeitenGTU Cloud Computing CourseEr Umesh ThoriyaNoch keine Bewertungen
- Sample Format: Academic Year 2018-19 - Semester B.EDokument3 SeitenSample Format: Academic Year 2018-19 - Semester B.EShobha KumarNoch keine Bewertungen
- Cloud Computing and Data Science SyllabusDokument3 SeitenCloud Computing and Data Science SyllabusNikhil TengliNoch keine Bewertungen
- CCSK Course Outlines PDFDokument5 SeitenCCSK Course Outlines PDFPooja SachdevaNoch keine Bewertungen
- Course Plan of 6th SemesterDokument9 SeitenCourse Plan of 6th SemesterAkash RavichandranNoch keine Bewertungen
- Cloud ComputingDokument1 SeiteCloud Computingperi cshodNoch keine Bewertungen
- Collaboration-Based Cloud Computing Security Management FrameworkDokument8 SeitenCollaboration-Based Cloud Computing Security Management FrameworkSaheli GuptaNoch keine Bewertungen
- Preparing To Take The Certificate of Cloud Security Knowledge (CCSK) A Cloud Security Alliance GuideDokument5 SeitenPreparing To Take The Certificate of Cloud Security Knowledge (CCSK) A Cloud Security Alliance Guidedeals4kbNoch keine Bewertungen
- Cyber Security and ApplicationsDokument4 SeitenCyber Security and Applicationssj2100333Noch keine Bewertungen
- Cloud EngineerDokument20 SeitenCloud Engineeramit.andre8144Noch keine Bewertungen
- A Two Level-Security Model For Cloud Computing Based On The Biometric Features and Multi-Level EncryptionDokument13 SeitenA Two Level-Security Model For Cloud Computing Based On The Biometric Features and Multi-Level EncryptionTeddy IswahyudiNoch keine Bewertungen
- Enterprise Cloud Computing Lecture PlanDokument7 SeitenEnterprise Cloud Computing Lecture Planmithun d'souzaNoch keine Bewertungen
- CCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamVon EverandCCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamNoch keine Bewertungen
- Cybersecurity AU SyllabusDokument2 SeitenCybersecurity AU SyllabusAjay MukundNoch keine Bewertungen
- Fy Mtech Sem2 Ay2014 15Dokument31 SeitenFy Mtech Sem2 Ay2014 15swapnil0% (1)
- CCSK PrepDokument3 SeitenCCSK PrepAmr SaidNoch keine Bewertungen
- Cloud ComputingDokument4 SeitenCloud Computingaryan kothambiaNoch keine Bewertungen
- FoundationsDokument1 SeiteFoundationsritika malikNoch keine Bewertungen
- Artic ICST12 Ccfinalv 22Dokument8 SeitenArtic ICST12 Ccfinalv 22desx redjNoch keine Bewertungen
- Cloud Computing Course OutlineDokument3 SeitenCloud Computing Course Outlinetahreem nazimNoch keine Bewertungen
- Cloud Computing Course Plan 491CS G262Dokument6 SeitenCloud Computing Course Plan 491CS G262DrMohamed MustaqNoch keine Bewertungen
- An Analysis of The Cloud Computing Security ProblemDokument6 SeitenAn Analysis of The Cloud Computing Security Problemrmsaqib1Noch keine Bewertungen
- CCSK Prep Guide V3Dokument4 SeitenCCSK Prep Guide V3satish_networkerNoch keine Bewertungen
- Cs6703 Grid and Cloud Computing - SyllabusDokument3 SeitenCs6703 Grid and Cloud Computing - SyllabusjayanthikrishnanNoch keine Bewertungen
- Security Issues in Cloud Computing: Kalyani D. Kadam Sonia K. Gajre R. L. PaikraoDokument5 SeitenSecurity Issues in Cloud Computing: Kalyani D. Kadam Sonia K. Gajre R. L. Paikraoetylr mailNoch keine Bewertungen
- Dual Access Control for Cloud Data StorageDokument4 SeitenDual Access Control for Cloud Data StorageSowmya MNoch keine Bewertungen
- Commerce and Related Security Issues and Challenge SemesterDokument4 SeitenCommerce and Related Security Issues and Challenge Semesteradil pansotaNoch keine Bewertungen
- Auditing Cloud Computing: A Security and Privacy GuideVon EverandAuditing Cloud Computing: A Security and Privacy GuideBewertung: 3 von 5 Sternen3/5 (2)
- CLD SecDokument12 SeitenCLD SecAman KumarNoch keine Bewertungen
- Cloud Security Using Blowfish and Key Management Encryption AlgorithmDokument4 SeitenCloud Security Using Blowfish and Key Management Encryption AlgorithmerpublicationNoch keine Bewertungen
- Hy-SAIL Hyper-Scalability Availability and Integrity Layer For Cloud Storage SystemsDokument12 SeitenHy-SAIL Hyper-Scalability Availability and Integrity Layer For Cloud Storage SystemsgsandiwNoch keine Bewertungen
- Cloud Computing Risk Assessment: A Systematic Literature ReviewDokument12 SeitenCloud Computing Risk Assessment: A Systematic Literature ReviewAbdallah QusefNoch keine Bewertungen
- Data Security and Privacy Protection Issues in Cloud ComputingDokument5 SeitenData Security and Privacy Protection Issues in Cloud Computingoptimistic07Noch keine Bewertungen
- Security Analysis of CloudDokument5 SeitenSecurity Analysis of CloudAaron MangalNoch keine Bewertungen
- Cloud Computing Course File for III B.Tech II SemesterDokument8 SeitenCloud Computing Course File for III B.Tech II SemesterMukundha ChNoch keine Bewertungen
- Software Project Management: SyllabusDokument6 SeitenSoftware Project Management: SyllabusAnonymous rFt9CaE1Noch keine Bewertungen
- A Project ReportDokument21 SeitenA Project Report10-Aniket MatodkarNoch keine Bewertungen
- Framework For Secure Cloud ComputingDokument15 SeitenFramework For Secure Cloud ComputingAnonymous roqsSNZNoch keine Bewertungen
- Cloud Computing Course CurriculumDokument1 SeiteCloud Computing Course Curriculummax singhNoch keine Bewertungen
- Data Security and Privacy Using Data Partition Centric Key Management in CloudDokument60 SeitenData Security and Privacy Using Data Partition Centric Key Management in CloudPidikiti Surendra BabuNoch keine Bewertungen
- CSE-4081: Cloud Computing: Course Context and OverviewDokument2 SeitenCSE-4081: Cloud Computing: Course Context and Overviewraghav dhamaniNoch keine Bewertungen
- Accountable Privacy-Preserving Mechanism For Cloud Computing Based On Identity-Based EncryptionDokument14 SeitenAccountable Privacy-Preserving Mechanism For Cloud Computing Based On Identity-Based EncryptionPrathyushaNoch keine Bewertungen
- 2929-Article Text-2710-1-10-20230304Dokument5 Seiten2929-Article Text-2710-1-10-20230304makuadzdhvfragravsNoch keine Bewertungen
- Cloud Computing Theory Syllabus-23Dokument3 SeitenCloud Computing Theory Syllabus-23nociwo4894Noch keine Bewertungen
- 7th Sem SyllDokument13 Seiten7th Sem Syll19001011008 ANIKET BHATIANoch keine Bewertungen
- Cloud Computing - Introduction, Application, SecurityDokument5 SeitenCloud Computing - Introduction, Application, Securityno07Noch keine Bewertungen
- CS-520 Cloud ComputingDokument2 SeitenCS-520 Cloud Computingshekhar785424Noch keine Bewertungen
- R18 B.Tech - CSE Syllabus IV Year - Removed - Removed - RemovedDokument8 SeitenR18 B.Tech - CSE Syllabus IV Year - Removed - Removed - Removedshamshuddin MdNoch keine Bewertungen
- 4-1 SyllabusDokument6 Seiten4-1 Syllabusvenulucky951Noch keine Bewertungen
- Cloud Computing - Unit IVDokument18 SeitenCloud Computing - Unit IVSWATHINoch keine Bewertungen
- Vii Sem - Cc-SyllabusDokument2 SeitenVii Sem - Cc-SyllabusShaik azeezullahNoch keine Bewertungen
- Matter 01Dokument59 SeitenMatter 01Ranjana DalwaniNoch keine Bewertungen
- CC SyllabusDokument6 SeitenCC SyllabusSafish MaryNoch keine Bewertungen
- Cloud Computing: Security Issues and SolutionsDokument4 SeitenCloud Computing: Security Issues and SolutionsInternational Journal of Application or Innovation in Engineering & ManagementNoch keine Bewertungen
- Cloud ComputingDokument4 SeitenCloud ComputingSrijita MukherjeeNoch keine Bewertungen
- Cloud Security - A Primer by Yogesh Gupta, CISSP® CCSK CCSP - The Cloud, Services, Standards - PeerlystDokument8 SeitenCloud Security - A Primer by Yogesh Gupta, CISSP® CCSK CCSP - The Cloud, Services, Standards - PeerlystrossloveladyNoch keine Bewertungen
- CloudcomputingDokument18 SeitenCloudcomputingKaran KatariaNoch keine Bewertungen
- Unit 2 - Political Orientation of CTDokument7 SeitenUnit 2 - Political Orientation of CTonesnoneNoch keine Bewertungen
- Sad Unit 4 - Real Time SystemsDokument10 SeitenSad Unit 4 - Real Time SystemsonesnoneNoch keine Bewertungen
- Cyber Security Global Information InfrastructureDokument7 SeitenCyber Security Global Information InfrastructureonesnoneNoch keine Bewertungen
- Cyber ForensicsDokument6 SeitenCyber ForensicsonesnoneNoch keine Bewertungen
- SAD Unit 4 Distributed Database DesignDokument30 SeitenSAD Unit 4 Distributed Database DesignonesnoneNoch keine Bewertungen
- Chapter 1 - Information Society, Knowledge Society and Didgital EconomyDokument35 SeitenChapter 1 - Information Society, Knowledge Society and Didgital EconomyonesnoneNoch keine Bewertungen
- Book Chapter - Cyber Terrorsim Part1Dokument4 SeitenBook Chapter - Cyber Terrorsim Part1onesnoneNoch keine Bewertungen
- Unit 4 CSDokument19 SeitenUnit 4 CSonesnoneNoch keine Bewertungen
- Book Chapter - Cyber Terrorsim Part2Dokument13 SeitenBook Chapter - Cyber Terrorsim Part2onesnoneNoch keine Bewertungen
- Cyber Security Global Information InfrastructureDokument7 SeitenCyber Security Global Information InfrastructureonesnoneNoch keine Bewertungen
- Book Chapter 3 - Critical Infra and Critical Info InfraDokument22 SeitenBook Chapter 3 - Critical Infra and Critical Info InfraonesnoneNoch keine Bewertungen
- SAD Unit 4 Distributed Database Components, TypesDokument8 SeitenSAD Unit 4 Distributed Database Components, TypesonesnoneNoch keine Bewertungen
- Book Chapter 4 - Global InfrastructureDokument10 SeitenBook Chapter 4 - Global InfrastructureonesnoneNoch keine Bewertungen
- Book Chapter 2-Cyber Space, Cyber SecurityDokument30 SeitenBook Chapter 2-Cyber Space, Cyber SecurityonesnoneNoch keine Bewertungen
- Python Programming Lecture ModulesDokument17 SeitenPython Programming Lecture ModulesonesnoneNoch keine Bewertungen
- SAD - Rate MonotonicDokument1 SeiteSAD - Rate MonotoniconesnoneNoch keine Bewertungen
- Btech Syllabus Cse 2018-19Dokument168 SeitenBtech Syllabus Cse 2018-19Arpita BaliNoch keine Bewertungen
- Decision Table & Decision TreeDokument3 SeitenDecision Table & Decision TreeonesnoneNoch keine Bewertungen
- BBA Scheme and SyllabusDokument51 SeitenBBA Scheme and SyllabusonesnoneNoch keine Bewertungen
- BBA Scheme and SyllabusDokument51 SeitenBBA Scheme and SyllabusonesnoneNoch keine Bewertungen
- Sad uNIT 4-Distibuted Database Systems Features, Adv and DisadvantagesDokument10 SeitenSad uNIT 4-Distibuted Database Systems Features, Adv and DisadvantagesonesnoneNoch keine Bewertungen
- Syllabus of Cloud Computing and PlanDokument2 SeitenSyllabus of Cloud Computing and PlanonesnoneNoch keine Bewertungen
- BBA Scheme and SyllabusDokument51 SeitenBBA Scheme and SyllabusonesnoneNoch keine Bewertungen
- Logical to Physical Design ImplementationDokument15 SeitenLogical to Physical Design ImplementationonesnoneNoch keine Bewertungen
- Machine LearningDokument4 SeitenMachine LearningonesnoneNoch keine Bewertungen
- Satyug Darshan Institute of Engg. & TechnologyDokument5 SeitenSatyug Darshan Institute of Engg. & TechnologyonesnoneNoch keine Bewertungen
- Neelam SainiDokument3 SeitenNeelam SainionesnoneNoch keine Bewertungen
- Satyug Darshan Institute of EnggDokument5 SeitenSatyug Darshan Institute of EnggonesnoneNoch keine Bewertungen
- SaurabhDokument1 SeiteSaurabhonesnoneNoch keine Bewertungen
- VR Simulation of Real & Imaginary Worlds for Specific PurposesDokument2 SeitenVR Simulation of Real & Imaginary Worlds for Specific Purposesdino_020% (1)
- MPPT Solar Charge Controller: Tracer A SeriesDokument4 SeitenMPPT Solar Charge Controller: Tracer A Seriesfingkan fitriyantiNoch keine Bewertungen
- p328.07x - Vogue Wireless Charging Speaker 2Dokument28 Seitenp328.07x - Vogue Wireless Charging Speaker 2Georgie SNoch keine Bewertungen
- Dolby Pulse BrochureDokument2 SeitenDolby Pulse BrochureHà Huy HoàngNoch keine Bewertungen
- A1. J1939 Fmis and DescriptionsDokument3 SeitenA1. J1939 Fmis and Descriptionsabdelhadi houssinNoch keine Bewertungen
- Syngistix 2.2 For ICP MS Software GuideDokument411 SeitenSyngistix 2.2 For ICP MS Software GuideSaswataNoch keine Bewertungen
- The Machine As Seen at The End of The Mechanical Age 1968Dokument222 SeitenThe Machine As Seen at The End of The Mechanical Age 1968Manuel Bogalheiro100% (2)
- Uci 401 AssignmentDokument15 SeitenUci 401 Assignmentevans kiplimoNoch keine Bewertungen
- Blockchain Regulatory ReportDokument264 SeitenBlockchain Regulatory Reportsmanley5Noch keine Bewertungen
- SEM Workshop Presentation 3Dokument28 SeitenSEM Workshop Presentation 3felixkern1991Noch keine Bewertungen
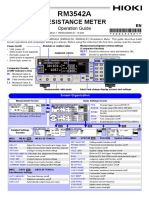
- Resistance Meter: Operation GuideDokument2 SeitenResistance Meter: Operation GuideEko SutjiptoNoch keine Bewertungen
- Actia Manual ENDokument4 SeitenActia Manual ENmonsieurminou72Noch keine Bewertungen
- JS - Solar Energy - 1Dokument15 SeitenJS - Solar Energy - 1Venkat GamingNoch keine Bewertungen
- Oasis Mon Taj Tutorial NewDokument325 SeitenOasis Mon Taj Tutorial NewM Hasan BasriNoch keine Bewertungen
- Autosar TR SwcmodelingguideDokument57 SeitenAutosar TR SwcmodelingguideRadu ButnaruNoch keine Bewertungen
- 1.4 NN MP Neuron ModelDokument20 Seiten1.4 NN MP Neuron ModelSatyam RanaNoch keine Bewertungen
- 2015 AREMA MRE Chapter 33 Power SupplyDokument194 Seiten2015 AREMA MRE Chapter 33 Power SupplyIulianNoch keine Bewertungen
- John Deere 7720 Parts CatalogDokument20 SeitenJohn Deere 7720 Parts Catalogalejandro100% (38)
- Job Details - Join Indian NavyDokument6 SeitenJob Details - Join Indian NavySaurabh KatkarNoch keine Bewertungen
- PostgreSQL: Historia, requisitos de instalación y componentes claveDokument7 SeitenPostgreSQL: Historia, requisitos de instalación y componentes claveJosue AlmanzaNoch keine Bewertungen
- Kirloskar Technologies P. LTD.: Appraisal FormDokument4 SeitenKirloskar Technologies P. LTD.: Appraisal Formdihudi.prasantaNoch keine Bewertungen
- A7800 PDFDokument9 SeitenA7800 PDFkarkonNoch keine Bewertungen
- Scope of e - Retailing in India 4.5Dokument29 SeitenScope of e - Retailing in India 4.5Ankit SinghNoch keine Bewertungen
- Awp Serv Embedded 7-0-50 RLDokument12 SeitenAwp Serv Embedded 7-0-50 RLOscar Alberto ZambranoNoch keine Bewertungen
- Tim Sweeney - Google SearchDokument1 SeiteTim Sweeney - Google SearchPatton DerionNoch keine Bewertungen
- DAQO CatalogueDokument24 SeitenDAQO CatalogueZigor Larrabe UribeNoch keine Bewertungen
- Telefone IP 8002 - 80012Dokument3 SeitenTelefone IP 8002 - 80012Ronaldo JoseNoch keine Bewertungen
- Selling and Buying A Product - Useful PhrasesDokument1 SeiteSelling and Buying A Product - Useful PhrasesBusy BrainsNoch keine Bewertungen
- MDS Report for PTFE TubeDokument3 SeitenMDS Report for PTFE TubeyatheendravarmaNoch keine Bewertungen
- Chziri zvf330 Ac Drive User Manual E375Dokument59 SeitenChziri zvf330 Ac Drive User Manual E375Diego Armando Carrera palmaNoch keine Bewertungen