Beruflich Dokumente
Kultur Dokumente
Railway Reservation System2
Hochgeladen von
Rahul PaulOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Railway Reservation System2
Hochgeladen von
Rahul PaulCopyright:
Verfügbare Formate
1
ONLINE RAILWAY RESERVATION SYSTEM
MEGHNAD SAHA INSTITUTE OF TECHNOLOGY DEPARTMENT OF COMPUTER SCIENCE ENGINERRING THE PROJECT IS CARRIED OUT BY ----APU DEY ARITRA BANERJEE JIT SAHA RAHUL PAUL SUMAN DAS SUBHA SEN _______________ _______________ _______________ _______________ _______________ _______________
CERTIFICATE OF ORIGINALITY
To Whom It May Concern
This is to certify that the Project report entitled ONLINE RAILWAY RESERVATION SYSTEM is submitted to IETE in partial fulfillment of the requirement for the award of the degree of, BACHELOR OF COMPUTER SCIENCE AND ENGINEERING, is an original work carried out by Apu Dey with University roll number 08142001025,Aritra Banerjee with University roll no 08142001030,Jit Saha ,with university roll no 08142001018,Rahul Paul with university roll number 08142001029,Suman Das with University roll no 08142001036 and Subho Sen with University roll no 09142001063,under the guidance of Mainak Basu Roy. The matter in this project is a genuine work done by the student and has not been submitted elsewhere of any course of study.
________________________ Mainak Basu Roy Industry Seal and Signature
___________________
Acknowledgement
Mere going through books and doing some homework is not sufficient. We wish to get a total command over a subject or topic. For this purpose project work is very important. The project web application which we are the developer- are about to propose deals with Online Railway Reservation. The project report contains an overall description of the developed software. The description contains almost all the modules that we the developers have made and also indicates their functionality and how to use them. They are basically so user-friendly that a novice can use it very easily. This project description is described with most of the basic things step by step like what configuration and which software we use to make this project, the necessity of developing the project , the technology it use and also the complete description of the modules along with the screenshots . I owe a great many thanks to many great people who helped and supported me during the project.
First, we would like to give our deepest thanks to our Lecturer or guide Mainak Basu Roy for guiding and correcting various documents of mine with attention and care. He has taken pain to go through the project and make necessary correction as and when needed. Without whose guidance and moral support developing such software would have been only a dream with no real existence. Thank you sir. We are really grateful to you. I express my thanks to the Principal of MEGHNAD SAHA INSTITUTE OF TECHNOLOGY, Kolkata for extending his support. Then we would like to thank IETE Campus for allowing us to do this project under their guidance and for providing us with such an excellent teacher. We believe that the honour of thanks should also be given to WBUT (West Bengal University of Technology) for introducing the concept of project work in our syllabus without which the idea of doing it wouldnt have come to our mind. Last but not the least we would like to thank the reader for bearing with us. We would be grateful to them if they forgive us for our mistakes and help us to rectify them by filling up the provided feedback form. Thanking you.
CONTENTS
PAGE NO:
INTRODUCTION 6 2. PROPOSED 7 3. SYSTEM DEVELOPMENT LIFE 8- 17 4. TESTING 18 WHITE BOX TESTING BLACK BOX TESTING 5. E.R. DIAGRAM 6. DATA FLOW DIAGRAM 7. SCREENSHOTS 8. ADVANTAGES OF THE SYSTEM 9. HARDWARE/SOFTWARE REQUIREMENTS 10. BIBLIOGRAPHY
1.
SYSTEM CYCLE
INTRODUCTION
This project introduces railway reservation system . It explains how reservation is being done in Indian Railways . The step by step procedure is explained . This project is developed in ASP.NET platform . Almost all the header files have been used in this project. Proper comments have been given at desired locations to make the project user friendly. Various functions and structures are used to make a complete use of this language. Thos project is well versed with the programming . Railway reservation can easily accompanied with the help of this.
PROPOSED SYSTEM
Today one cannot afford to rely on the fallible human beings of be really wants to stand against todays merciless competition where not to wise saying to err is human no longer valid, its outdated to rationalize your mistake. So, to keep pace with time, to bring about the best result without malfunctioning and greater efficiency so to replace the unending heaps of flies with a much sophisticated hard disk of the computer. One has to use the data management software. Software has been an ascent in atomization various organizations. Many software products working are now in markets, which have helped in making the organizations work easier and efficiently. Data management initially had to maintain a lot of ledgers and a lot of paper work has to be done but now software product on this organization has made their work faster and easier. Now only this software has to be loaded on the computer and work can be done. This prevents a lot of time and money. The work becomes fully automated and any information regarding the organization can be obtained by clicking the button. Moreover, now its an age of computers of and automating such an organization gives the better look.
SYSTEM DEVELOPMENT LIFE CYCLE
The systems development life cycle is a project management technique that divides complex projects into smaller, more easily managed segments or phases. Segmenting projects allows managers to verify the successful completion of project phases before allocating resources to subsequent phases. Software development projects typically include initiation, planning, design, development, testing, implementation, and maintenance phases. However, the phases may be divided differently depending on the organization involved. For example, initial project activities might be designated as request, requirements-definition, and planning phases, or initiation, concept-development, and planning phases. End users of the system under development should be involved in reviewing the output
10
of each phase to ensure the system is being built to deliver the needed functionality.
PHASES CYCLE
OF
SYSTEM
DEVELOPMENT
LIFE
Initiation Phase
The Initiation Phase begins when a business sponsor identifies a need or an opportunity. The purpose of the Initiation Phase is to:
11
Identify and validate an opportunity to improve business accomplishments of the organization or a deficiency related to a business need.
Identify significant assumptions and constraints on solutions to that need. Recommend the exploration of alternative concepts and methods to satisfy the need including questioning the need for technology, i.e., will a change in the business process offer a solution? Assure executive business and executive technical sponsorship. The Sponsor designates a Project Manager and the business need is documented in a Concept Proposal. The Concept Proposal includes information about the business process and the relationship to the Agency/Organization Infrastructure and the Strategic Plan. A successful Concept Proposal results in a Project Management Charter which outlines the authority of the project manager to begin the project. Careful oversight is required to ensure projects support strategic business objectives and resources are effectively implemented into an organization's enterprise architecture. The initiation phase begins when an opportunity to add, improve, or correct a system is identified and formally requested through the presentation of a business case. The business case should, at a minimum, describe a proposals purpose, identify expected benefits, and explain how the proposed system supports one of the organizations business strategies. The business case should also identify alternative solutions and detail as
12
many informational, requirement
functional, as
and
network possible.
System Concept Development Phase
The System Concept Development Phase begins after a business need or opportunity is validated by the Agency/Organization Program Leadership and the Agency/Organization CIO. The purpose of the System Concept Development Phase is to: Determine the feasibility and appropriateness of the alternatives. Identify system interfaces. Identify basic functional and data requirements to satisfy the business need. Establish system boundaries, identify goals, objectives, critical success factors, and performance measures. Evaluate costs and benefits of alternative approaches to satisfy the basic functional requirements Assess project risks Identify and initiate risk mitigation actions, and Develop high-level technical architecture, process models, data models, and a concept of operations. This phase explores potential technical solutions within the context of the business need. It may include
13
several trade-off decisions such as the decision to use COTS software products as opposed to developing custom software or reusing software components, or the decision to use an incremental delivery versus a complete, one-time deployment. Construction of executable prototypes is encouraged to evaluate technology to support the business process. The System Boundary Document serves as an important reference document to support the Information Technology Project Request (ITPR) process. The ITPR must be approved by the State CIO before the project can move forward.
PICTORIAL REPRESENTATION OF SDLC:-
14
Planning Phase
15
The planning phase is the most critical step in completing development, acquisition, and maintenance projects. Careful planning, particularly in the early stages of a project, is necessary to coordinate activities and manage project risks effectively. The depth and formality of project plans should be commensurate with the characteristics and risks of a given project. Project plans refine the information gathered during the initiation phase by further identifying the specific activities and resources required to complete a project. A critical part of a project managers job is to coordinate discussions between user, audit, security, design, development, and network personnel to identify and document as many functional, security, and network requirements as possible. During this phase, a plan is developed that documents the approach to be used and includes a discussion of methods, tools, tasks, resources, project schedules, and user input. Personnel assignments, costs, project schedule, and target dates are established. A Project Management Plan is created with components related to acquisition planning, configuration management planning, quality assurance planning, concept of operations, system security, verification and validation, and systems engineering management planning.
16
Requirements Analysis Phase
This phase formally defines the detailed functional user requirements using high-level requirements identified in the Initiation, System Concept, and Planning phases. It also delineates the requirements in terms of data, system performance, security, and maintainability requirements for the system. The requirements are defined in this phase to a level of detail sufficient for systems design to proceed. They need to be measurable, testable, and relate to the business need or opportunity identified in the Initiation Phase. The requirements that will be used to determine acceptance of the system are captured in the Test and Evaluation Master Plan. The purposes of this phase are to: Further define and refine the functional and data requirements and document them in the Requirements Document, Complete business process reengineering of the functions to be supported (i.e., verify what information drives the business process, what information is generated, who generates it, where does the information go, and who processes it), Develop detailed data and process models (system inputs, outputs, and the process.
17
Develop the test and evaluation requirements that will be used to determine acceptable system performance.
Design Phase
The design phase involves converting the informational, functional, and network requirements identified during the initiation and planning phases into unified design specifications that developers use to script programs during the development phase. Program designs are constructed in various ways. Using a top-down approach, designers first identify and link major program components and interfaces, then expand design layouts as they identify and link smaller subsystems and connections. Using a bottomup approach, designers first identify and link minor program components and interfaces, then expand design layouts as they identify and link larger systems and connections. Contemporary design techniques often use prototyping tools that build mock-up designs of items
18
such as application screens, database layouts, and system architectures. End users, designers, developers, database managers, and network administrators should review and refine the prototyped designs in an iterative process until they agree on an acceptable design. Audit, security, and quality assurance personnel should be involved in the review and approval process. During this phase, the system is designed to satisfy the functional requirements identified in the previous phase. Since problems in the design phase could be very expensive to solve in the later stage of the software development, a variety of elements are considered in the design to mitigate risk. These include: Identifying potential risks and defining mitigating design features. Performing a security risk assessment. Developing a conversion plan to migrate current data to the new system. Determining the operating environment. Defining major subsystems and their inputs and outputs. Allocating processes to resources. Preparing detailed logic specifications for each software module. The result is a draft System Design Document which captures the preliminary design for the system. Everything requiring user input or approval is documented and reviewed by the user. Once these documents have been approved by the Agency CIO and Business Sponsor, the final System
19
Design Document is created to serve as the Critical/Detailed Design for the system. This document receives a rigorous review by Agency technical and functional representatives to ensure that it satisfies the business requirements. Concurrent with the development of the system design, the Agency Project Manager begins development of the Implementation Plan, Operations and Maintenance Manual, and the Training Plan.
Development Phase
The development phase involves converting design specifications into executable programs. Effective development standards include requirements that programmers and other project participants discuss design specifications before programming begins. The procedures help ensure programmers clearly understand program designs and functional requirements. Programmers use various techniques to develop computer programs. The large transaction-oriented programs associated with financial institutions have traditionally been developed using procedural programming techniques. Procedural programming
20
involves the line-by-line scripting of logical instructions that are combined to form a program. Effective completion of the previous stages is a key factor in the success of the Development phase. The Development phase consists of: Translating the detailed requirements and design into system components. Testing individual elements (units) for usability. Preparing for integration and testing of the IT system.
Integration Phase
and
Test
Subsystem integration, system, security, and user acceptance testing is conducted during the integration and test phase. The user, with those responsible for quality assurance, validates that the functional requirements, as defined in the functional requirements document, are satisfied by the developed or modified system. OIT Security staff assess the system security and issue a security certification and accreditation prior to installation/implementation. Multiple levels of testing are performed, including:
21
Testing at the development facility by the contractor and possibly supported by end users Testing as a deployed system with end users working together with contract personnel Operational testing by the end user alone performing all functions. Requirements are traced throughout testing, a final Independent Verification & Validation evaluation is performed and all documentation is reviewed and accepted prior to acceptance of the system.
Implementation Phase
This phase is initiated after the system has been tested and accepted by the user. In this phase, the system is installed to support the intended business functions. System performance is compared to performance objectives established during the planning phase. Implementation includes user notification, user training, installation of hardware, installation of software onto production computers, and integration of the system into daily work processes.
22
This phase continues until the system is operating in production in accordance with the defined user requirements.
Operations and Maintenance Phase
The system operation is ongoing. The system is monitored for continued performance in accordance with user requirements and needed system modifications are incorporated. Operations continue as long as the system can be effectively adapted to respond to the organizations needs. When modifications or changes are identified, the system may reenter the planning phase. The purpose of this phase is to: Operate, maintain, and enhance the system. Certify that the system can process sensitive information. Conduct periodic assessments of the system to ensure the functional requirement continue to satisfy. Determine when the system needs to be modernized or replaced,
Testing
23
Software Testing is an empirical investigation conducted to provide stakeholders with information about the quality of the product or service under test[1] , with respect to the context in which it is intended to operate. Software Testing also provides an objective, independent view of the software to allow the business to appreciate and understand the risks at implementation of the software. Test techniques include, but are not limited to, the process of executing a program or application with the intent of finding software bugs. It can also be stated as the process of validating and verifying that a software program/application/product meets the business and technical requirements that guided its design and development, so that it works as expected and can be implemented with the same characteristics. Software Testing, depending on the testing method employed, can be implemented at any time in the development process, however the most test effort is employed after the requirements have been defined and coding process has been completed.
Testing methods
Software testing methods are traditionally divided into black box testing and white box testing. These two approaches are used to describe the point of view that a test engineer takes when designing test cases.
Black box testing
Black box testing treats the software as a "black box," without any knowledge of internal implementation.
24
Black box testing methods include: equivalence partitioning, boundary value analysis, all-pairs testing, fuzz testing, model-based testing, traceability matrix, exploratory testing and specification-based testing.
Specification-based testing
Specification-based testing aims to test the functionality of software according to the applicable requirements.[16] Thus, the tester inputs data into, and only sees the output from, the test object. This level of testing usually requires thorough test cases to be provided to the tester, who then can simply verify that for a given input, the output value (or behavior), either "is" or "is not" the same as the expected value specified in the test case. Specification-based testing is necessary, but it is insufficient to guard against certain risks
Advantages and disadvantages
The black box tester has no "bonds" with the code, and a tester's perception is very simple: a code must have bugs. Using the principle, "Ask and you shall receive," black box testers find bugs where programmers don't. But, on the other hand, black box testing has been said to be "like a walk in a dark labyrinth without a flashlight," because the tester doesn't know how the
25
software being tested was actually constructed. That's why there are situations when (1) a black box tester writes many test cases to check something that can be tested by only one test case, and/or (2) some parts of the back end are not tested at all. Therefore, black box testing has the advantage of "an unaffiliated opinion," on the one hand, and the disadvantage of "blind exploring," on the other.
White box testing
White box testing, by contrast to black box testing, is when the tester has access to the internal data structures and algorithms (and the code that implement these)
Types of white box testing :The following types of white box testing exist: api testing - Testing of the application using Public and Private APIs. code coverage - creating tests to satisfy some criteria of code coverage. For example, the test designer can create tests to cause all statements in the program to be executed at least once. fault injection methods. mutation testing methods. static testing - White box testing includes all static testing.
26
Code completeness evaluation
White box testing methods can also be used to evaluate the completeness of a test suite that was created with black box testing methods. This allows the software team to examine parts of a system that are rarely tested and ensures that the most important function points have been tested.[19] Two common forms of code coverage are: function coverage, which reports on functions executed and statement coverage, which reports on the number of lines executed to complete the test.
They both return a coverage metric, measured as a percentage
27
DATA FLOW DIAGRAM:-
LEVEL 0 DIAGRAM/CONTEXT LEVEL DIAGRAM
n o p s e R
28
LEVEL 1 DIAGRAM
train1
29
P a ym en t 0 .4 .3
Bo o
Sum 0.
R ESERVE T IC K E T
0 .4 .2
B o ok LEVEL 2 DIAGRAM tic ket
Check tra in d e ta ils
Lo g in 0 .4 .1
30
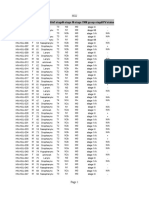
TABLE ADMINDATA----
SCREENSHOTS
31
TABLE CITIES----
32
TABLE PASS ----
33
TABLE TABLE1 ------
34
TABLE TRAIN ----
35
TABLE TRAIN1 ----
36
PROJECT SCREENSHOTS-----HOME PAGE ---
37
SEAT AVAILABILITY --- this page shows whether the seats in a class of the corresponding train is available or not.
Train enquiry --- this page shows the list of trains that ply between two stations as entered by the user.
38
LOGIN PAGE--- This page logs on the user to its account for either making a reservation or viewing booking history.
Signup page--- New users can sign in using this page.
39
FORGOT PASSWORD ---
Detail Page--- This page enables the user to select either making a reservation or viewing booking history
40
Route Page--- This page selects the source and destination station
List of trains that ply between two stations---
41
Passenger details page--- This page enables the user to input passenger details.
42
Summary Page---This page summarizes the transaction made by the user
Payment details--- Credit Card Details of the Payment as accorded by the user.
43
Booking History--- Lists the transactions made by the user and its corresponding PNR
44
PNR query page--- The user queries its booking through the PNR.
ADVANTAGES OF RAILWAY RESERVATION SYSTEM
Now one can easily plan the journey comfortably as the process is efficient and fast with being easy to access. Reservations can be made through the Indian railways site or at the ample reservation centers all over the country. Also now there are authorized agencies which provide reservation facility on behalf of India railways and without
45
waiting in long line one can easily book a ticket. The booking is done through an ETicket issue which have a PNR number of which one has to take a print and just have to show at the station. It not only provide reservation but cancellation can also be done through this system at ease and one can use a credit card to complete the process. This being a big step in terms of improvement in the railway system it is widely accepted across the country.
46
SOFTWARE
AND
HARDWARE
REQUIREMENTSSS HARDWARE REQUIREMENTS:
I. II.
OPERATING SYSTEM : Windows XP PROCESSOR: PENTIUM(ANY) ATHALON(3800+- 4200+ DUAL CORE OR AMD
III. RAM :1GB OR ABOVE IV. HDD:160+ V. CD ROM
SOFTWARE REQUIREMENTS:
I. office XP II. Microsoft Visual Studio 2008 III. SQL SERVER 2005
47
BIBLIOGRAPHY
These are the following links which assist me at each and every step in compliting this project , without them i was not be able to finish this important project:1. 2. 3. 4. 5.
www.scribd.com www.wikipedia.com www.answers.com www.askme.com www.esnips.com
Das könnte Ihnen auch gefallen
- INFOclinical HN Version2 30may2018Dokument38 SeitenINFOclinical HN Version2 30may2018Rahul PaulNoch keine Bewertungen
- WP Contentuploads201909Bonsai Basic Design 2-12-13.PDF 3Dokument49 SeitenWP Contentuploads201909Bonsai Basic Design 2-12-13.PDF 3Rahul PaulNoch keine Bewertungen
- Pixel-Based and Region-Based Image Fusion Schemes Using ICA BasesDokument12 SeitenPixel-Based and Region-Based Image Fusion Schemes Using ICA BasesRahul PaulNoch keine Bewertungen
- Image ReconstructionDokument28 SeitenImage ReconstructionRahul PaulNoch keine Bewertungen
- Object TrackingDokument23 SeitenObject TrackingRahul PaulNoch keine Bewertungen
- 333 High Frequency GRE Words With MeaningsDokument4 Seiten333 High Frequency GRE Words With Meaningsvysakhpillai100% (4)
- Seminar ReportDokument21 SeitenSeminar ReportRahul PaulNoch keine Bewertungen
- LISHELPDokument1 SeiteLISHELPRahul PaulNoch keine Bewertungen
- 2011 IEEE Symposium On Security and Privacy 2011 IEEE Symposium On Security and PrivacyDokument9 Seiten2011 IEEE Symposium On Security and Privacy 2011 IEEE Symposium On Security and PrivacyRahul PaulNoch keine Bewertungen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Sapthagiri College of Engineering: Tracing Manufacturing Processes Using Blockchain Based Token CompositionsDokument19 SeitenSapthagiri College of Engineering: Tracing Manufacturing Processes Using Blockchain Based Token CompositionsYashi FakeNoch keine Bewertungen
- Paranormal Activity 3Dokument5 SeitenParanormal Activity 3alexNoch keine Bewertungen
- Ms 95-2018 Solved AssignmentDokument15 SeitenMs 95-2018 Solved AssignmentPramod ShawNoch keine Bewertungen
- CAM Charges Working For The Month of May 2023Dokument1 SeiteCAM Charges Working For The Month of May 2023adnandani2882Noch keine Bewertungen
- External Command in 10 Steps For Revit 2015Dokument2 SeitenExternal Command in 10 Steps For Revit 2015JigneshNoch keine Bewertungen
- GANTREX® MK6 Rail PadDokument4 SeitenGANTREX® MK6 Rail PadwickremasingheNoch keine Bewertungen
- Workstation-Sub Micro Space PlanDokument21 SeitenWorkstation-Sub Micro Space Planarnella_hNoch keine Bewertungen
- Case Study #3 ThermodynamicsDokument6 SeitenCase Study #3 ThermodynamicsColeene Forteza100% (1)
- Sky Spark White PaperDokument7 SeitenSky Spark White PaperJohn KablerNoch keine Bewertungen
- HOF - To PrasannaDokument3 SeitenHOF - To PrasannahishamndtNoch keine Bewertungen
- Global Cardiac Catheters - 2012-2018Dokument4 SeitenGlobal Cardiac Catheters - 2012-2018Axis Research MindNoch keine Bewertungen
- Nvidia CompanyDokument4 SeitenNvidia CompanyaaaNoch keine Bewertungen
- Superb 2 Aditional HeaterDokument2 SeitenSuperb 2 Aditional Heaterpalle larsenNoch keine Bewertungen
- SystemVerilog DPI With SystemCDokument17 SeitenSystemVerilog DPI With SystemCSWAPNIL DWIVEDINoch keine Bewertungen
- sITE aVAIL 29-07-2021Dokument58 SeitensITE aVAIL 29-07-2021ogbodoemaNoch keine Bewertungen
- Dodge Journey 2017 - Owner's ManualDokument510 SeitenDodge Journey 2017 - Owner's Manualandres camachin100% (1)
- Project Report JamiaDokument76 SeitenProject Report JamiaShoaibNoch keine Bewertungen
- Palfinger PK 15500 Load ChartDokument2 SeitenPalfinger PK 15500 Load ChartD Chandra Sekhar100% (2)
- Trial and Error: Failure and Innovation in Criminal Justice ReformDokument5 SeitenTrial and Error: Failure and Innovation in Criminal Justice ReformAzim MohammedNoch keine Bewertungen
- Drive List BoxDokument3 SeitenDrive List BoxLuis Carlos VillegasNoch keine Bewertungen
- Sikafloor Morritex Self-Levelling Broadcast SystemDokument4 SeitenSikafloor Morritex Self-Levelling Broadcast SystemTPNoch keine Bewertungen
- Online Bank SynopsisDokument7 SeitenOnline Bank SynopsisPrashant VermaNoch keine Bewertungen
- Global Edge Interview ExperienceDokument2 SeitenGlobal Edge Interview Experienceshafi hasmaniNoch keine Bewertungen
- Adopter CategoriesDokument6 SeitenAdopter CategoriesCaroline Mputhia100% (1)
- 3BSE035980-600 A en System 800xa Control 6.0 AC 800M Configuration PDFDokument580 Seiten3BSE035980-600 A en System 800xa Control 6.0 AC 800M Configuration PDFWaqas AnjumNoch keine Bewertungen
- Original Instructions Alkuperäiset Ohjeet Αρχικýj Οδηγßεj: Rev. 4 5/31/11 BrwDokument32 SeitenOriginal Instructions Alkuperäiset Ohjeet Αρχικýj Οδηγßεj: Rev. 4 5/31/11 BrwnikosvitalNoch keine Bewertungen
- What Are The Good Research QuestionDokument26 SeitenWhat Are The Good Research Questionkavindukarunarathna100% (2)
- Water Tank Seat Slab DesignDokument2 SeitenWater Tank Seat Slab DesignMesfin Derbew100% (2)
- Omd Graviner Mk6 ManualDokument90 SeitenOmd Graviner Mk6 ManualChristis SavvaNoch keine Bewertungen