Beruflich Dokumente
Kultur Dokumente
Secure FTP POC Document
Hochgeladen von
Janet Leigh StewartOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Secure FTP POC Document
Hochgeladen von
Janet Leigh StewartCopyright:
Verfügbare Formate
Wiggle Wireless
WIGGLE Wireless Secure FTP for IBM i5/OS
All of the information contained within this document has been created for the sole purpose of providing an easy reference for the setup and configuration of Secure FTP for WIGGLE Wireless. All attempts have been made to provide this information accurately and as it pertains to the IBM i5/OS Version 5.3. For up to date information and or potential changes please refer to the IBM iSeries Infocenter located at http://publib.boulder.ibm.com/infocenter/iseries/v5r3/index.jsp.
Confidential
69697753.doc2 Page 1
9/28/2011
Wiggle Wireless
Table of Contents
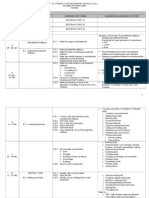
WIGGLE Wireless ..............................................................................................................1 Secure FTP for IBM i5/OS .................................................................................................1 Table of Contents.................................................................................................................2 1.1 Introduction to Secure File Transfer (SFTP)............................................................3 1.2 Planning and Prerequisites for Secure FTP on the IBM iSeries ..............................3 1.2.1 Planning Suggestions:.......................................................................... 3 1.2.2 SSL Prerequisites:................................................................................ 4 1.3 Digital Certificate Manager.....................................................................................6 1.4 Certificate Stores .....................................................................................................7 1.4.1 Local Certificate Authority (CA):........................................................... 7 1.4.2 *SYSTEM............................................................................................. 7 1.4.3 *OBJECTSIGNING............................................................................... 7 1.4.4 Other System Certificate Store.............................................................8 2.1 Transferring files using secure FTP.........................................................................9 2.1.2 Plan the configuration of the server certificate................................... 10 2.1.3 Create the *SYSTEM Certificate Store ............................................. 10 2.1.5 Obtaining a server certificate from a well-known CA - VeriSign........17 2.1.5.1 Create a system certificate request................................17 2.1.6 Import the VeriSign certificate into the Certificate store..................... 27 2.1.7 Configure the FTP client to trust the Certificate Authority.................. 42 2.1.8 Configure the FTP server to listen for secure connections................ 47 2.1.9 Test the configuration.......................................................................... 48 3.1 Renewing the Server Certificate.............................................................................50 Additional material........................................................................................................61 Certificate store structure and locations........................................................ 61 Cleaning up DCM.......................................................................................... 62 Migrating to New Hardware........................................................................... 62 Local CA Certificate Parameters................................................................... 64 Server Certificate Parameters....................................................................... 65 Public Certificates versus Private Certificates.............................................. 66 Troubleshooting ............................................................................................................68 Troubleshooting ADMIN Server Problems.................................................... 68 Troubleshooting - Problem Determination for FTP....................................... 69 FTP Problem Analysis................................................................................... 69 Documentation and Links.............................................................................. 71
Confidential
69697753.doc2 Page 2
9/28/2011
Wiggle Wireless
1.1 Introduction to Secure File Transfer (SFTP)
The FTP server con be configured to provide enhanced security while sending and receiving files over an un-trusted network. FTP server can use Secure Sockets Layer (SSL) to secure passwords and other sensitive data during an information exchange. The FTP server supports either SSL or TLS protected sessions, including client authentication and automatic sign-on. Most SSL-enabled applications connect a client to separate TCP ports, one port for "unprotected" sessions and the other for secure sessions. However, secure FTP is a bit more flexible. A client can connect to a non-encrypted TCP port (usually TCP port 21) and then negotiate authentication and encryption options. A client can also choose a secure FTP port (usually TCP port 990), where connections are assumed to be SSL. The iSeries FTP server provides for both of these options. To ensure that your FTP sessions are encrypted, limit your client connections to port 990 through the use of a firewall or native iSeries TCP/IP filtering. Before you can configure the FTP server to use SSL, you must have installed the prerequisite programs and set up digital certificates on your iSeries.
1.2 Planning and Prerequisites for Secure FTP on the IBM iSeries
When planning to enable SSL on an iSeries server, consider the following: Planning suggestions
SSL prerequisites
1.2.1 Planning Suggestions:
Password Management Implement a password policy o Create one password to be used for all Certificate Stores Warning: You must be sure that you can remember the password that you set, or that you write it down and store it in a secure place. Create and secure an Import Folder in the IFS for Certificates on each System. Make this consistent across systems. Decide on a distinct name to be used for Certificate label. Note: Certificate (key) labels in a certificate store must be unique. Therefore, you should plan ahead regarding the use of the certificate being created here and where that certificate will be stored. For example, if the default label is used and then you try to add this certificate to a different certificate store that already has a certificate with the default
Confidential
69697753.doc2 Page 3
9/28/2011
Wiggle Wireless
label, you will not be able to add this certificate to that store because the labels are not unique (a duplicate key label error will occur). There is no function in DCM to change a certificate label. If you have a duplicate key problem, the only choice is to create a new certificate with a different label. Decide on a distinct Common Name to be used on each Certificate. Enter a name to describe the certificate application. This is a required field when creating the certificate or the certificate request. How you choose a name for the certificate varies depending on the environment in which the application communicates data. For example, if you are creating a certificate for a server application that communicates data over the Internet, you should use the fully qualified domain name for the server. This ensures that browser software can validate the certificate correctly. When the certificate's common name does not match the URL domain name, the browser can validate the certificate. However, the browser cannot verify the server's identity. Consequently, the browser may warn the user of this discrepancy and prompt the user to decide whether to trust the certificate.
Ensure that you have a well planned disaster recovery plan including frequent and well maintained backups of data. In the case of digital certificates, it is important to backup the IFS directory /QIBM/UserData/ICSS and all subdirectories as well as the certificates received from your certificate provider (like VeriSign). Maintain a table of certificate installation and expiration dates and make it easily accessible to those who will maintain certificates. Although Digital Certificate Manager (DCM) has a facility to view certificate expiry information, there is currently no easy method to centrally maintain certificate information other than a user maintained database.
1.2.2 SSL Prerequisites:
User profile Must have *ALLOBJ and *SECADM for Administration purposes IBM Digital Certificate Manager (DCM), option 34 of OS/400 (5722-SS1) TCP/IP Connectivity Utilities for iSeries (5722-TC1) IBM HTTP Server for iSeries (5722-DG1) If you are trying to use the HTTP server to use the DCM, ensure that you have the correct option of the IBM Developer Kit for Java (5722JV1) installed. Otherwise, the HTTP admin server will not start. The IBM Cryptographic Access Provider product, 5722-AC3 (128-bit). The bit size for this product indicates the maximum size of the secret material within the symmetric keys that can be used in cryptographic operations. The size allowed for a symmetric key is controlled by the export and import laws of each country. A higher bit size results in a more secure connection. You may also want to install cryptographic hardware to use with SSL to speed up the SSL handshake processing. See the Cryptographic hardware information for available options. If you want to install the 4758 IBM Cryptographic Coprocessor or the 4764 IBM Cryptographic Coprocessor, you must also install Option 35, the Cryptographic Service Provider.
Confidential
69697753.doc2 Page 4
9/28/2011
Wiggle Wireless
If you want to use SSL with iSeries Access for Windows components, you must also install the iSeries Client Encryption product, 5722-CE3 (128-bit). iSeries Access for Windows requires this product in order to establish the secure connection. Note: You do not need to install a Client Encryption Product to use the PC5250 emulator that is shipped with the Personal Communications product. Personal Communications has its own builtin encryption code.
Confidential
69697753.doc2 Page 5
9/28/2011
Wiggle Wireless
1.3 Digital Certificate Manager
IBM Digital Certificate Manager (DCM) is the iSeries server solution for managing digital certificates. Digital Certificate Manager (DCM) provides a browser-based user interface that you can use to manage digital certificates for your applications and users. The user interface is divided into two main frames: a navigation frame and a task frame You use the navigation frame to select the tasks to manage certificates or the applications that use them. While some individual tasks appear directly in the main navigation frame, most tasks in the navigation frame are organized into categories. For example, Manage Certificates is a task category that contains a variety of individual guided tasks, such as View certificate, Renew certificate, Import certificate, and so forth. If an item in the navigation frame is a category that contains more than one task, an arrow appears to the left of it. The arrow indicates that when you select the category link, an expanded list of tasks displays so that you may choose which task to perform. With the exception of the Fast Path category, each task in the navigation frame is a guided task that takes you through a series of steps to complete the task quickly and easily. The Fast Path category provides a cluster of certificate and application management functions which allows experienced DCM users to quickly access a variety of related tasks from a central set of pages. Which tasks are available in the navigation frame vary based on the certificate store in which you are working. Also, the category and number of tasks that you see in the navigation frame vary depending on the authorizations that your i5/OS user profile has. All tasks for operating a CA, managing the certificates that applications use, and other system level tasks are available only to security officers or administrators. The security officer or administrator must have *SECADM and *ALLOBJ special authorities to view and use these tasks. Users without these special authorities have access to user certificate functions only.
Before you can use any of its functions, you need to start Digital Certificate Manager (DCM). Complete these tasks to ensure that you can start DCM successfully:
1. Sign on with a profile that has *SECADM and *ALLOBJ. 2. Install 5722 SS1 Option 34. This is Digital Certificate Manager (DCM).
3. Install 5722 DG1. This is the IBM HTTP Server for iSeries. 4. Install 5722 AC3. This is the cryptography product that DCM uses to generate a publicprivate key pair for certificates, to encrypt exported certificate files, and decrypt imported certificate files. 5. On the command line, type STRTCPSVR *HTTP HTTPSVR(*ADMIN). 6. Verify HTTPSVR started, type WRKSBSJOB QHTTPSVR.
Confidential
69697753.doc2 Page 6
9/28/2011
Wiggle Wireless
1.4 Certificate Stores
A certificate store is a special key database file that Digital Certificate Manager (DCM) uses to store digital certificates. The certificate store also contains the certificate's private key unless you choose to use an IBM Cryptographic Coprocessor to store the key instead. DCM allows you to create and manage several types of certificate stores. DCM controls access to certificate stores through passwords in conjunction with access control of the integrated file system directory and the files that constitute the certificate store. Certificate stores are classified based on the types of certificates that they contain. The management tasks that you can perform for each certificate store vary based on the type of certificate that the certificate store contains. DCM provides the following predefined certificate stores that you can create and manage:
1.4.1 Local Certificate Authority (CA):
DCM uses this certificate store to store the Local CA certificate and its private key if you create a Local CA. You can use the certificate in this certificate store to sign certificates that you use the Local CA to issue. When the Local CA issues a certificate, DCM puts a copy of the CA certificate (without the private key) in the appropriate certificate store (for example, *SYSTEM) for authentication purposes. Applications use CA certificates to verify the origination of certificates that they must validate as part of the SSL negotiation to grant authorization to resources.
1.4.2 *SYSTEM
DCM provides this certificate store for managing server or client certificates that applications use to participate in Secure Sockets Layer (SSL) communications sessions. IBM applications (and many other software developers' applications) are written to use certificates in the *SYSTEM certificate store only. When you use DCM to create a Local CA, DCM creates this certificate store as part of the process. When you choose to obtain certificates from a public CA, such as VeriSign, for your server or client applications to use, you must create this certificate store.
1.4.3 *OBJECTSIGNING
DCM provides this certificate store for managing certificates that you use to digitally sign objects. Also, the tasks in this certificate store allow you to create digital signatures on objects, as well as view and verify signatures on objects. When you use DCM to create a Local CA, DCM creates this certificate store as part of the process. When you choose to obtain certificates from a public CA, such as VeriSign, for signing objects, you must create this certificate store.
Confidential
69697753.doc2 Page 7
9/28/2011
Wiggle Wireless
1.4.4 Other System Certificate Store
This certificate store provides an alternate storage location for server or client certificates that you use for SSL sessions. Other System Certificate Stores are user-defined secondary certificate stores for SSL certificates. The Other System Certificate Store option allows you to manage certificates for applications that you or others write that use the SSL_Init API to programmatically access and use a certificate to establish an SSL session. This API allows an application to use the default certificate for a certificate store rather than a certificate that you specifically identify. Most commonly, you use this certificate store when migrating certificates from a prior release of DCM, or to create a special subset of certificates for SSL use. Note: If you have an IBM Cryptographic Coprocessor installed on your server, you can choose other private key storage options for your certificates (with the exception of object signing certificates). You can elect to store the private key on the coprocessor itself or use the coprocessor to encrypt the private key and store it in a special key file instead of in a certificate store. DCM controls access to certificate stores through passwords. DCM also maintains access control of the integrated file system directory and the files that constitute the certificate stores. The Local Certificate Authority (CA), *SYSTEM, *OBJECTSIGNING, and *SIGNATUREVERIFICATION certificate stores must be located in the specific paths within the integrated file system, Other System Certificate stores can be located anywhere in the integrated file system.
Confidential
69697753.doc2 Page 8
9/28/2011
Wiggle Wireless
2.1 Transferring files using secure FTP
We will walk through the steps to configure the FTP server on the iSeries to support secure connections from clients using TLS/SSL (Transport Layer Security/Secure Sockets Layer), and how to configure the iSeries FTP client to securely connect to an FTP server. In order to use SSL secured FTP sessions, the FTP server needs to have a certificate associated with it. Also, the FTP clients need to trust the Certificate Authority (CA) that issued the FTP servers certificate. WIGGLE has opted to use a Public (well-known) Certificate Authority to issue the servers certificate.
How-to
To configure the iSeries servers to connect using the secured FTP, perform the following steps:
1. Plan the configuration of the server certificate on each system. 2. Create the *SYSTEM certificate store and certificate signing request. 3. Import the certificate into the *SYSTEM certificate store.
4. Configure the server to listen for secure connections.
5. Configure the FTP client to trust the Certificate Authority.
6. Test the configuration.
Confidential
69697753.doc2 Page 9
9/28/2011
Wiggle Wireless
2.1.2 Plan the configuration of the server certificate
The FTP server needs an server certificate in order to create secure connections with the FTP clients. The specifications of the server certificate are included in Table 2-2 and are ordered from www.VeriSign.com.
Configuration Parameter Value Key size Certificate Label Certificate Store Password Password Confirmation Common Name Organization unit Organization name Locality State Country
1024 CW iSeries Cert XXXXXXXXXX XXXXXXXXXX CFGTCP option 12 will be used as the fully qualified host name (common name) WIGGLE Georgia US
Table 2-1 FTP Server certificate configuration parameters
2.1.3 Create the *SYSTEM Certificate Store
The *SYSTEM Certificate Store is used to store the server certificate that will be used by the FTP server. To create the *SYSTEM Certificate Store, perform the following steps, using the values in Table 2-1: 1. Verify that the Administration server is started on the iSeries.
On the iSeries run the command: WRKACTJOB SBS(QHTTPSVR) or type WRKSBSJOB QHTTPSVR. You should see several jobs name ADMIN running in this subsystem. If you do, go to Step 2.
If you dont see ADMIN jobs running issue the following command: STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN). Verify that the jobs start. If this is the first time the ADMIN server has been started it may take several minutes before you are able to access it. Proceed to the next step once you verify that all of the ADMIN jobs (there should be 3) have started and are in SIGW status. You should see several jobs name ADMIN running in this subsystem. If you do not, see Troubleshooting Admin Server Problems in the Additional Material Section.
Confidential
69697753.doc2 Page 10
9/28/2011
Wiggle Wireless
2. Access the iSeries Task page by opening the location http://Your_System_Name:2001 (you would supply your iSeries host name followed by :2001), using your browser. Enter User Name and Password.
3. The iSeries Tasks page is displayed as in Figure 2-2. Click on Digital Certificate
Manager.
Figure 2-2 iSeries Task page
Confidential
69697753.doc2 Page 11
9/28/2011
Wiggle Wireless
4. The Digital Certificate Manager Screen should look as shown in Figure 2-3. The left frame of Digital Certificate Manager (DCM) is the task navigation frame. You can use this frame to select a wide variety of tasks for managing certificates and the applications that use them. Which tasks are available depends on which certificate store (if any) you work with and your user profile special authorities. Most tasks are available only if you have *ALLOBJ and *SECADM special authorities. If you do not see all of the options in the selection pane on the left, you are probably signed on with a profile without proper Authority.
Figure 2-3 Digital Certificate Manager page
Confidential
69697753.doc2 Page 12
9/28/2011
Wiggle Wireless
5. Once in the DCM environment (Figure 2-3) Select Create New Certificate Store from the navigation (left) panel.
Since there is currently no *SYSTEM store on this iSeries the default value will be *SYSTEM (Figure 2-4) in the Create New Certificate Store window. Click Continue.
Figure 2-4 Select the type of certificate store to create
Confidential
69697753.doc2 Page 13
9/28/2011
Wiggle Wireless
6. In the Create a Certificate in New Certificate Store window, shown in Figure 2-5, choose
not to create a certificate.
Select No - Do not create a certificate in the certificate store. Click Continue.
Figure 2-5 Do not create a certificate in the new store
Confidential
69697753.doc2 Page 14
9/28/2011
Wiggle Wireless
7. The next window (Figure 2-6) allows you to create a password for the new certificate
store. You are asked to enter the password twice to verify. Remember the password, you will need it later.
Key in store password and confirm password. Click Continue.
Figure 2-6 Choose a password for the *SYSTEM store
Confidential
69697753.doc2 Page 15
9/28/2011
Wiggle Wireless
8. The next window (Figure 2-7) confirms that the new certificate store has been created.
Figure 2-7 Message indicating that the certificate store was created The *SYSTEM certificate store has been created. The Certificate Authority import process can now take place.
Confidential
69697753.doc2 Page 16
9/28/2011
Wiggle Wireless
2.1.5 Obtaining a server certificate from a well-known CA VeriSign
This section shows how to request and receive a server certificate from a well-known CA. WIGGLE has chosen to use VeriSign. When using such a certificate, you do not have to worry about distributing and maintaining a local CAs certificate. But from the security point of view you and the users have to fully trust the issuing CA. The following steps take you through the process of obtaining a server certificate from a wellknown CA.
2.1.5.1 Create a system certificate request
The first task when obtaining a system certificate is to create the certificate request using DCM. 1. click Select a Certificate Store from the left panel of the DCM. 2. Select the Radio button for *SYSTEM as show in Figure 2-8. 3. Click Continue.
Figure 2-8
Select *SYSTEM Store
Confidential
69697753.doc2 Page 17
9/28/2011
Wiggle Wireless
4. Enter Store Password and Click Continue.
Figure 2-9
Store Password Page
Confidential
69697753.doc2 Page 18
9/28/2011
Wiggle Wireless
5. To create a system certificate request.
a. Click Create Certificate from the left panel of the DCM. b. Select the Radio button for Server or Client certificate. c. Click Continue.
Figure 2-10
Create Certificate page
Confidential
69697753.doc2 Page 19
9/28/2011
Wiggle Wireless
d. Select the radio button for VeriSign. e. Click on Continue.
Figure 2-11 Select a Certificate Authority
Confidential
69697753.doc2 Page 20
9/28/2011
Wiggle Wireless
f. Fill in the requested information as show below, Make the Certificate Label: CW iSeries Cert , Enter the Common name, Organization name, state, country. g. Click on Continue.
Figure 2-12
Create Certificate
h. Open a Change Request to get permission to install a certificate on the server, for the following maintenance window, unless the window is less than 24 hours away, if so, then use the next maintenance window.
Confidential
69697753.doc2 Page 21
9/28/2011
Wiggle Wireless
i. Copy the certificate request to notepad and email the.*txt file to the appropriate WIGGLE resource to submit to VeriSign. Make sure you select the area that includes -----BEGIN NEW CERTIFICATE REQUEST----- through the area that ends with -----END NEW CERTIFICATE REQUEST----- j. Give it the name of the server with csrr appended, i.e. (aatcar52csr.txt) See Figure 2-13. k. Click OK. l. After you email the notepad file to WIGGLE Resource to submit to VeriSign, delete the *txt notepad file.
Figure 2-13 Saving CSR as .txt
Confidential
69697753.doc2 Page 22
9/28/2011
Wiggle Wireless
m. After a certain time the person who submitted the CSR request to VeriSign receives the certificate through e-mail. They should. Copy and paste the certificate data received from VeriSign into a text file on your PC using, for example the Notepad editor. Make sure you select the area that includes -----BEGIN CERTIFICATE ----- through the area that ends with -----END CERTIFICATE -----. Make sure it is given a meaningful identifying name. Save in a protected folder. Remove the email received from VeriSign or save in a protected (preferably encrypted) email folder. Send Certificate file CSR requester.
Figure 2-14 Copy and Paste VeriSign Certificate
Confidential
69697753.doc2 Page 23
9/28/2011
Wiggle Wireless
n. On the Command line of the server, make sure the CW_Cert directory exists:
Type WRKLNK /CW_cert If it does not exist, type MKDIR DIR(CW_cert) Secure the Directory: WRKLNK /CW_cert
Enter 9 beside the directory, press ENTER
Work with Object Links
Directory
. . . . :
/ 13=Change directory attributes ... Attribute Text
Type options, press Enter. 9=Work with authority 10=Move Opt 9 Object link CW_cert Type DIR
Enter a 2 beside *PUBLIC
Work with Authority . . . . . . . . . . . . . . . . . . . . . . . . : : : : /CW_cert JSTEWART *NONE *NONE 4=Remove user
Object . . . . . . Owner . . . . . . Primary group . . Authorization list
Type options, press Enter. 1=Add user 2=Change user authority Opt 2 User *PUBLIC JSTEWART QDIRSRV QNOTES Authority *RWX *RWX *X *RWX Data Exist X X
--Object Authorities-Mgt Alter Ref X X X X X X
Confidential
69697753.doc2 Page 24
9/28/2011
Wiggle Wireless
Change all Object authorities (OBJAUT) to *NONE Press ENTER , and Enter again then Press CMD 5 to Refresh
Change Authority (CHGAUT) Type choices, press Enter. Object . . . . . . . . User . . . . . . . . . New data authorities . New object authorities > *OBJEXIST > *OBJALTER > *OBJREF Authorization list . . . . . . . AUTL . . . . . . . . . . . . . . . . . . . . OBJ USER DTAAUT OBJAUT > > > > '/CW_cert' *PUBLIC *RWX *OBJMGT
Enter a 2 beside *PUBLIC again
Work with Authority
Object . . . . . . Owner . . . . . . Primary group . . Authorization list
. . . .
. . . .
. . . .
. . . .
. . . .
. . . .
: : : :
/CW_cert JSTEWART *NONE *NONE
Type options, press Enter. 1=Add user 2=Change user authority Opt 2 User *PUBLIC JSTEWART QDIRSRV QNOTES Data Authority *RWX *RWX *X *RWX
4=Remove user
--Object Authorities-Exist Mgt Alter Ref X X X X
Change data authorities (DTAAUT) to *NONE Press ENTER , and Enter again Press CMD 5,
Change Authority (CHGAUT) Type choices, press Enter. Object . . . . . . . . . . . . . OBJ User . . . . . . . . . . . . . . USER > '/CW_cert' > *PUBLIC
Confidential
69697753.doc2 Page 25
9/28/2011
Wiggle Wireless
New data authorities . . . . . . DTAAUT New object authorities . . . . . OBJAUT + for more values Authorization list . . . . . . . AUTL
> *RWX *SAME
o. FTP the VeriSign Certificate .txt file the Server cd /CW_cert Be sure to enter NAMEFMT 1 Put certificatname.txt
Figure 2-15
FTP VeriSign certificate to Server
Confidential
69697753.doc2 Page 26
9/28/2011
Wiggle Wireless
2.1.6 Import the VeriSign certificate into the Certificate store
Now import the VeriSign certificate in the *SYSTEM certificate store. Starting from the window in Figure 2-16, follow these steps: Note: Make sure the HTTP server is started (See Section 1.3, step 5 and 6) 1. In the DCM navigation panel:
Click on the Select a Certificate Store button. In the Select a Store window verify that the radio button next to *SYSTEM is selected. Click Continue.
Figure 2-16 Select the *SYSTEM store to import the file into
Confidential
69697753.doc2 Page 27
9/28/2011
Wiggle Wireless
2. In the Certificate Store and Password window provide the password and click Continue.
Figure 2-17 Certificate Store Password
Confidential
69697753.doc2 Page 28
9/28/2011
Wiggle Wireless
3. Once the screen refreshes, in DCM navigation panel on the left,
Click on Manage Certificates, as shown in Figure 2-18.
Figure 2-18 Select the option to Manage Certificates
Confidential
69697753.doc2 Page 29
9/28/2011
Wiggle Wireless
4. From the Manage Certificates page as shown in Figure 2-19, Select the radio button for Import Certificate. Click on Continue.
Figure 2-19 Import Certificates selection
Confidential
69697753.doc2 Page 30
9/28/2011
Wiggle Wireless
5. The Import Certificate page is displayed, as shown in Figure 2-20. Select the Server or Client radio button. Click Continue.
Figure 2-20 DCM - Import Certificate page
Confidential
69697753.doc2 Page 31
9/28/2011
Wiggle Wireless
6. The Import Server or Client Certificate page is displayed, as you can see in Figure 2-21.
In the Import file field, specify the full name of the file (including the leading /) that contains the Certificate to be imported. We used /CW_cert/aatcar51cer.txt Click Continue.
Figure 2-21 DCM - Import Server or Client Certificate page
Confidential
69697753.doc2 Page 32
9/28/2011
Wiggle Wireless
7. You should see a message stating the import was successful, as in figure 2-22 Click OK.
Figure 2-22 DCM Import Server or Client Certificate
Confidential
69697753.doc2 Page 33
9/28/2011
Wiggle Wireless
8. From the left panel select Fast Path, shown in Figure 2-23. Click on Fast Path.
Figure 2-23 DCM Select Fast Path
Confidential
69697753.doc2 Page 34
9/28/2011
Wiggle Wireless
9. From the Fast Path page, shown in Figure 2-24: Select Radio Button Work with server and client certificates. Click Continue.
Figure 2-24 DCM Select Fast Path
Confidential
69697753.doc2 Page 35
9/28/2011
Wiggle Wireless
10. The Work with Server and Client Certificates page is displayed, as seen in Figure 2-25. Select the certificate, here it is labeled CW iSeries Cert. Click on Assign to Applications.
Figure 2-25 DCM Assign Certificate
Confidential
69697753.doc2 Page 36
9/28/2011
Wiggle Wireless
11. The Select Applications page is displayed, as seen in Figure 2-26. Scroll down until you see the OS/400 TCP/IP FTP Server option. Select OS/400 TCP/IP FTP Server. Click Continue.
Figure 2-26 DCM Assign Certificate
Confidential
69697753.doc2 Page 37
9/28/2011
Wiggle Wireless
12. You should see an Application Status message as shown in Figure 2-27. Click OK.
Figure 2-27 DCM Select Applications Application Status Message
You will be returned to the Work with Server and Client Certificates page, Click Cancel. From the Fast Path page, Click Cancel.
Confidential
69697753.doc2 Page 38
9/28/2011
Wiggle Wireless
13. Verify Server Certificates assignment
Click on Manage Applications from the left side Panel in the DCM. Click on radio button View application definition. Click Continue.
Figure 2-28 DCM Manage Applications Page
Confidential
69697753.doc2 Page 39
9/28/2011
Wiggle Wireless
14. View Application Definition
Click on radio button for Server. Click Continue.
Figure 2-29 DCM View Applications Definition Page
Confidential
69697753.doc2 Page 40
9/28/2011
Wiggle Wireless
15. From the View Application Definition Page
Scroll down and select the Radio button for OS/400 TCP/IP FTP Server. Click View. Next, Click on View Certificate and verify correct certificate assignment.
Figure 2-30 DCM View Applications Definition Page
Confidential
69697753.doc2 Page 41
9/28/2011
Wiggle Wireless
2.1.7 Configure the FTP client to trust the Certificate Authority
To configure the FTP client to trust the local CA, perform the following steps: 1. Continuing from the previous DCM session:
Click on Manage Applications from the list of tasks in the DCM navigation panel on the left as shown in Figure 2-30. Select Define CA trust list. Click on Continue.
Figure 2-31 DCM Define CA trust List
Confidential
69697753.doc2 Page 42
9/28/2011
Wiggle Wireless
2. The Define CA Trust List page is displayed, as shown in Figure 2-32. Select the Client radio button. Click Continue.
Figure 2-32 DCM - Define CA Trust List page
Confidential
69697753.doc2 Page 43
9/28/2011
Wiggle Wireless
3. The list with client applications installed on the iSeries server is displayed, as you can see in
Figure 2-33.
Select the OS/400 TCP/IP FTP Client radio button. Click Define CA Trust List.
Figure 2-33 DCM - Client applications trust list
Confidential
69697753.doc2 Page 44
9/28/2011
Wiggle Wireless
4. A list with all the Certificate Authorities on the system is displayed in the next window, as
shown in Figure 2-34.
Select all the VeriSign CAs listed. Click OK.
Figure 2-34 DCM - Certificate Authorities list
Confidential
69697753.doc2 Page 45
9/28/2011
Wiggle Wireless
5. A message is displayed in the next page, stating that the Certificate Authority changes have
been applied (see Figure 2-35).
Click Cancel to end the procedure.
Figure 2-35 DCM - Certificate Authority changes applied
Confidential
69697753.doc2 Page 46
9/28/2011
Wiggle Wireless
2.1.8 Configure the FTP server to listen for secure connections
To enable the FTP server to listen only for secure connections, perform the following steps:
1. Use the command line to configure FTP to listen for secure connections. This changes FTP attributes to allow SSL connections. (ALWSSL) which can be set to allow only SSL, or both SSL and non-secure connections. When this parameter is set to allow only SSL the FTP server will not start without a certificate assigned to the application (FTP server). Enter CHGFTPA ALWSSL(*YES)
Note : ALWSSL(*YES) The iSeries FTP server accepts non-SSL FTP sessions. If the prerequisite products needed to allow SSL support are installed and a valid FTP server certificate is configured in the Digital certificate Manager, SSL sessions will also be allowed. Note: If ALWSSL(*YES) is specified and the Digital Certificate Manager is configured for required FTP client authentication, non-SSL sessions are accepted by the FTP server. However, nonanonymous FTP users must switch to SSL mode in order to log in to the iSeries FTP server.
Command Entry Request level Previous commands and messages: (No previous commands or messages)
Type command, press Enter. ===> CHGFTPA ALLWSSL(*YES)
Figure 2-36 iSeries Command Entry Change FTP Properties
2. In order for the modifications to take effect, the FTP server must be restarted. Once this
done the FTP server will be able to support secure connects with any clients that trust our Certificate Authority. On the Command line enter the following command:
ENDTCPSVR SERVER(*FTP). Wait a moment and then enter the following command: STRTCPSVR SERVER(*FTP).
This completes the configuration of the FTP server to accept only secure connections.
Confidential
69697753.doc2 Page 47
9/28/2011
Wiggle Wireless
2.1.9 Test the configuration
Test the configuration, on a client and sever that have had the VeriSign certificates completely installed. To test the configuration, perform the following steps: 1. Connect to the client (non-repository) iSeries (FTP client) using a 5250 session. 2. Start a secure FTP session on Repository iSeries server by running the following command:
FTP System_name port(*SECURE)
Using this command, the client tries to establish secure control and data connections.
3. The FTP client is started and status messages are displayed on the screen. As you can see
in Figure 2-37, the control messages are displayed on the screen.
File Transfer Protocol Previous FTP subcommands and messages: Connecting to remote host WAXLAB01.WIGGLElab.com using port 990 Connection is secure. 220-QTCP at WAXLAB01.WIGGLElab.com 220 Connection will close if idle more than 5 minutes. Enter password: ===>
F3=Exit F17=Top
F6=Print F18=Bottom
F9=Retrieve F21=CL command line
Figure 2-37 FTP client screen - secure connection to server
Confidential
69697753.doc2 Page 48
9/28/2011
Wiggle Wireless
4. Connect to the FTP server and transfer a file to the server. The messages displayed on the
FTP client session screen should be like the ones in Figure 2-38.
Figure 2-38 FTP client screen - transfer a file to the server
Confidential
69697753.doc2 Page 49
9/28/2011
Wiggle Wireless
3.1 Renewing the Server Certificate
1. You will need to contact your certificate provider prior to the expiry date of the certificate to
request the certificate renewal. Check with your certificate provider for instructions. Give yourself plenty of time to renew your certificate before it expires. One to 2 weeks prior to the certificate expiration is probably good. You normally do not need to go through the full Certificate Signing Request that you did when you first created the certificate as most certificate providers will renew your certificate without an additionsl CSR (Certificate Signing Request).
2. Next, you will need to FTP the renewed certificate you received to your iSeries. Refer to
section 2.1.5.1, steps 5 m through o for instructions to FTP the file you received from your certificate provider up to the IFS on your system. After FTPing the certificate to your system, continue with step 3. 3. Go to the Tasks page (Figure 3-11) via the iSeries HTTP Administration server using the URL: http://your_server_name.com:2001
Supply the user ID and password (must have IOSYSCFG, *ALLOBJ, *SECADM authority). Select Digital Certificate Manager. Click on Select a Certificate Store.
Confidential
69697753.doc2 Page 50
9/28/2011
Wiggle Wireless
Figure 3-11
Digital Certificate Manager page
Confidential
69697753.doc2 Page 51
9/28/2011
Wiggle Wireless
4. Enter the Certificate store password as shown in figure 3-12 and click Continue.
Figure 3-12
Certificate Store and Password page
Confidential
69697753.doc2 Page 52
9/28/2011
Wiggle Wireless
On the Current Certificate Store screen, Click on Manage Certificates to expand the selection and then click on the Renew certificate link.
Figure 3-13
Current Certificate Store page
Confidential
69697753.doc2 Page 53
9/28/2011
Wiggle Wireless
5. Choose the certificate that you wish to renew and then click the Renew button as shown in
Figure 3-14.
Figure 3-14
Renew Certificate page
Confidential
69697753.doc2 Page 54
9/28/2011
Wiggle Wireless
6. Choose VeriSign or other Internet Certificate Authority (CA) as shown in Figure 3-15 and
click Continue.
Figure 3-15
Select a Certificate Authority page
Confidential
69697753.doc2 Page 55
9/28/2011
Wiggle Wireless
7. Choose No Import the renewed signed certificate from an existing file and click
Continue.
Figure 3-16
Renew Certificate page
Confidential
69697753.doc2 Page 56
9/28/2011
Wiggle Wireless
8. Enter the path to the Import File that you FTPed up to the system in step 2 as shown in
Figure 3-17. When done, click Continue.
Figure 3-17
Import Server or Client Certificate page
Confidential
69697753.doc2 Page 57
9/28/2011
Wiggle Wireless
9. You will see the Certificate Renewed Successfully page as shown in Figure 3-18. Here you will select the application/s that you want to assign this renewed certificate to.
Figure 3-18
Certificate Renewed Successfully page
Confidential
69697753.doc2 Page 58
9/28/2011
Wiggle Wireless
10. Scroll down and check all applications that you wish to assign this certificate to and click Continue when finished.
Figure 3-19
Certificate Renewed Successfully page
Confidential
69697753.doc2 Page 59
9/28/2011
Wiggle Wireless
Figure 3-20
Application Status page
11. When you have finished, you will see the page displayed above in Figure 3-20. 12. You may need to cycle the application/s using the renewed certificate. Test the application
and ensure that if functions properly.
Confidential
69697753.doc2 Page 60
9/28/2011
Wiggle Wireless
Additional material
Certificate store structure and locations
Certificate Authority, server and user certificates and related information are stored in different directories on the AS/400 system. DCM provides a default store location for you.
Certificate Authority store location
DCM uses a fixed store location for the local CA. You cannot change its location. After you create a local CA you will see the following files in a specific directory. These directories must be protected from unauthorized access. The directory and files for the CA objects are: /QIBM/UserData/ICSS/Cert/CertAuth Directory CA.TXT CA certificate and public key DEFAULT.KDB CA certificate and CA private key DEFAULT.POL CA policy file DEFAULT.STH Stashed password for accessing the local CA KDB. /QIBM/UserData/ICSS/Cert/Download/CertAuth Directory containing the CA certificate available for distribution to clients CA.CACRT CA certificate in binary format
System certificate store location
You can select two types of locations to store a certificate. OS/400 server applications, such as HTTP and Telnet, can only use certificates stored in the *SYSTEM certificate store. Another selection is OTHER, which enables you to store certificates in any directory on the AS/400 Integrated File System (IFS). The directory and file structure is as follows: *SYSTEM (default store location) /QIBM/UserData/ICSS/Cert/Server Directory
DEFAULT.KDB System certificate(s), private key(s) and CA certificates DEFAULT.RDB Certificate request DEFAULT.STH Stashed password for automatic access to a KDB file by the server
Confidential
69697753.doc2 Page 61
9/28/2011
Wiggle Wireless
OTHER You can specify another directory such as /your_directory_name to store certificates. Customer applications that are written to use SSL_Init (instead of the newer SSL_Init_App) can make more use of this. System administrators can also make use of this certificate store for certain kinds of backups or testing before moving into their production environment. Some functions, such as exporting certificates from certificate stores created while the system was on a previous release, may also make use of this. Again do not use this if you want to use OS/400 secure applications.
Cleaning up DCM
Here are the locations to cleanup in order to start over with DCM (NOTE: We'll want to cleanup all files in these locations): These files can be deleted allowing you to start from scratch. Prior to deleting the *System store you should verify that the store does not contain certificates that have been purchased or are currently in use. There is no way to recover
files that have not been backed up after performing this operation. Only remove *STMF files, Do NOT remove the folders
/QIBM/UserData/ICSS/Cert/Server/ --> This location holds the *SYSTEM store /QIBM/UserData/ICSS/Cert/CertAuth/ --> This location holds the Local CA store /QIBM/UserData/ICSS/Cert/Download/CertAuth/CertAuth --> This locations holds a file that gets created when a CA is created (so that you can't create it again). Once all the files are cleared from these locations, get out of DCM and go back into it. You should now have the option to create a Local CA (which will in turn create a *SYSTEM store and a server/client cert in the store).
Also, from command line on the iSeries issue this command to clean up Cache:
CALL QSOMAINT PARM('10' '3')
Migrating to New Hardware
When performing a system migration to new iSeries hardware, DCM must be synchronized to run on the new serial number and hardware. If you do not perform this step, you will receive an error message when trying to start servers that require a digital certificate. The error will read: TCP7421 f/qzhbhttp qhttpsvr *stmt t/qzhbhttp qhttpsvr *stmt Message . . . . : The server cannot start with SSL mode on because SSL security is not installed. Cause . . . . . . : The AC1, AC2 or AC3 product must be installed before the HTTP server will start with SSL mode on.
Confidential
69697753.doc2 Page 62
9/28/2011
Wiggle Wireless
Recovery . . . : Remove "sslmode on" from your configuration file or install AC1, AC2 or AC3 and try to start the server again. To correct the error, on an iSeries command line type the following: CALL QCAP3/QYAC3INAT
Confidential
69697753.doc2 Page 63
9/28/2011
Wiggle Wireless
Local CA Certificate Parameters
Key size. You may select 512, 768, 1024, or 2048. It is true that the larger the key size the more secure the encryption level is, but a larger key size also creates more overhead on the system and the network. Password: This will be used to access the Local Certificate Authority certificate store. You will need to know this password in the future so follow whatever process you have in place to document passwords of this nature. Certificate Authority (CA) name: This is the name that will be displayed as the issuer of server certificates. Organization unit: This is an optional field. It may be used for accounting type purposes. Organization name: This is the name of the person or group that is responsible for operating and maintaining policy for this Certificate Authority. Locality or city: This parameter is not required. We supplied the value Atlanta. State or province: Note that this parameter requires at least 3 letters. It is best to spell out the state or province name completely. If you ever decide to change to a well know issuer of certificates the full name will be required when requesting certificates. Country or region: We supplied the value US. Validity period of Certificate Authority: Sets the length of time, in days, that the Certificate Authority certificate is valid. Certificates that are issued by this CA will also expire on or before this time period is reached.
Confidential
69697753.doc2 Page 64
9/28/2011
Wiggle Wireless
Server Certificate Parameters
Key size. As with the Certificate authority you may select 512, 768, 1024, or 2048. But keep in mind that the larger key size, although more secure, creates more overhead. Certificate label is just the name the certificate will be referred to as, in our case we called it iSeriesftp. There are no implications other than you want to make the name descriptive enough that its purpose is easily recognizable. Certificate store password is used to secure the certificate store. You need to follow your security guidelines for choosing the password. Common name parameter should be a meaningful identifier. If you plan to use the certificate for browser access, this becomes one of the more important fields on this screen. In this case, the best way to complete this field is to use the fully qualified host and domain name that is listed in the Change TCP/IP Domain (CHGTCPDMN) screen. When you make a secure connection (from a browser) and the Common name does not match the configured fully qualified domain name there is a warning that is displayed to the user. Although the warning does not stop the connection it is a nuisance that can be avoided. The Organization unit parameter is not a required field. We used IT Dept again, in keeping with the scenario. The Organization name should reflect the name of the group of users that will take advantage of the certificate. Locality or city does not need to be supplied, but we used the location of the server. The State or province field is a required parameter and must contain at least three characters. We suggest you spell out your location completely. Country or region must be filled in with a two character abbreviation of your country or region. Note: The remaining fields on this screen are used to further secure a Virtual Private Network (VPN) connection. Much like the process we are completing now when VPN is used SSL is configured to provide client certificates as an added level of security.
Confidential
69697753.doc2 Page 65
9/28/2011
Wiggle Wireless
Public Certificates versus Private Certificates
Once you decide to use certificates, you need to choose the type of certificate implementation that best suits your security needs. The choices that you have for obtaining your certificates include: Purchasing your certificates from a public Internet Certificate Authority (CA). Operating your own Local CA to issue private certificates for your users and applications. Using a combination of certificates from public Internet CAs and your own Local CA.
Which of these implementation choices you make depends on a number of factors, one of the most important being the environment in which the certificates are used. Here's some information to help you better determine which implementation choice is right for your business and security needs.
Using public certificates
Public Internet CAs issue certificates to anyone who pays the necessary fee. However, an Internet CA still requires some proof of identity before it issues a certificate. This level of proof varies, though, depending on the identification policy of the CA. You need to evaluate whether the stringency of the identification policy of the CA suits your security needs before deciding to obtain certificates from the CA or to trust the certificates that it issues. As Public Key Infrastructure for X.509 (PKIX) standards have evolved, some public CAs now provide much more stringent identification standards for issuing certificates. While the process for obtaining certificates from such PKIX CAs is more involved, the certificates the CA issues provide better assurance for securing access to applications by specific users. Digital Certificate Manager (DCM) allows you to use and manage certificates from PKIX CAs that use these new certificate standards. You must also consider the cost associated with using a public CA to issue certificates. If you need certificates for a limited number of server or client applications and users, cost may not be an important factor for you. However, cost can be particularly important if you have a large number of private users that need public certificates for client authentication. In this case, you need to also consider the administrative and programming effort needed to configure server applications to accept only a specific subset of certificates that a public CA issues. Using certificates from a public CA may save you time and resources because many server, client, and user applications are configured to recognize most of the well-known public CAs. Also, other companies and users may recognize and trust certificates that a well-known public CA issues more than those that your private Local CA issues.
Confidential
69697753.doc2 Page 66
9/28/2011
Wiggle Wireless
Using private certificates
If you create your own Local CA, you can issue certificates to systems and users within a more limited scope, such as within your company or organization. Creating and maintaining your own Local CA allows you to issue certificates only to those users who are trusted members of your group. This provides better security because you can control who has certificates, and therefore who has access to your resources, more stringently. A potential disadvantage of maintaining your own Local CA is the amount of time and resources that you must invest. However, Digital Certificate Manager (DCM) makes this process easier for you. When you use a Local CA to issue certificates to users for client authentication, you need to decide where you want to store the user certificates. When users obtain their certificates from the Local CA through DCM their certificates are stored with a user profile by default. However, you can configure DCM to work with Enterprise Identity Mapping (EIM) so that their certificates are stored in a Lightweight Directory Access Protocol (LDAP) location instead. If you prefer not to have user certificates associated or stored with a user profile in any manner, you can use APIs to programmatically issue certificates to non-iSeries users.
Confidential
69697753.doc2 Page 67
9/28/2011
Wiggle Wireless
Troubleshooting
Troubleshooting ADMIN Server Problems
If the *ADMIN server fails to start, you will need to determine the reason why and take corrective action.
1. On an iSeries command line, type WRKSPLF QTMHHTTP. This will display spooled files
that belong to user QTMHHTTP (this is the user that is responsible for starting the *ADMIN server. Look at the last spooled file belonging to QTMHHTTP and it should tell you why the *ADMIN server failed to start. 2. Edit the ADMIN custom config file that resides in the IFS a. On the iSeries run the command WRKLNK and navigate to directory /QIBM/UserData/HTTPA/admin/conf/ b. Edit the file admin-cust.conf and look for any invalid directives, if
you can not determine the cause of the error, comment out all of the lines in the custom config as shown in the following example using the # character. #-----------------------------------------------------# The following directives should be added to # /QIBM/UserData/HTTPA/admin/conf/admin-cust.conf # and uncommented in order to enable SSL for ADMIN. #-----------------------------------------------------# LoadModule ibm_ssl_module /QSYS.LIB/QHTTPSVR.LIB/QZSRVSSL.SRVPGM # Listen 2001 # Listen 2010 # SetEnv HTTPS_PORT 2010 # <VirtualHost *:2010> # SSLEnable # SSLAppName QIBM_HTTP_SERVER_ADMIN # </VirtualHost>
Restart the *ADMIN server and ensure that it starts correctly.
Confidential
69697753.doc2 Page 68
9/28/2011
Wiggle Wireless
Troubleshooting - Problem Determination for FTP
If you detect a problem when using FTP, use the following flow chart to identify the cause after using the flow chart for general TCP/IP problems. The cause lists that follow list steps to help you identify the cause of the problem.
FTP Problem Analysis
Cause List A
1.
Is there is a long delay between connecting to the iSeries(TM) FTP server and receiving a prompt for a user id? If so, check the configuration of the domain name server on your iSeries. The FTP server performs a DNS query as soon as a new connection is received. DNS problems may cause the server to hang for several minutes before a response is received. 2. Check to see if an exit program has been added to the FTP Server Logon Exit Point. Refer to the Server logon exit point subtopic. If yes, then check if the logon that is unsuccessful is allowed by the exit program.
Confidential
69697753.doc2 Page 69
9/28/2011
Wiggle Wireless
3. Check to see if the remote logon requires a password if a password was requested. Some systems request a password, but the connection can fail because it is not required. 4. Set up a password on the remote system if required. You may have to restart if you change the security information on the system. 5. Check your user ID and password by attempting to sign on to your remote system. If you are unable to do so, contact the system owner to verify that your user ID and password are correct.
Cause List B 1. Make sure binary mode is in effect if you are transferring binary files. 2. Check to be sure the mapping tables on both the client and server systems are compatible. You need only do this if you are using your own mapping tables. 3. Check to see that the correct CCSID has been specified for the transfer. If not, use the TYPE or LTYPE subcommand to set the correct CCSID value before the transfer is performed. 4. Create a file on the system that you are planning to store data into. Set the proper record length, number of members, and number of increments. Try the data transfer again and verify that it was successful. 5. Make sure that you are authorized to use the file and the file members. 6. Check to see if the transfer file contains packed decimal or zoned decimal data. 7. If you are transferring a Save file, verify that the appropriate method was used.
Cause List C 1. Check file size limits on the remote system. 2. Check to see if the FTP server timer ended. The iSeries server time-out value can be set using the QUOTE TIME command. 3. Use the NETSTAT command to verify that the *LOOPBACK interface is active. Then re-create the problem doing FTP LOOPBACK (iSeries-to-iSeries internally). If the problem cannot be recreated, it is probably a remote system problem. If you can re-create the problem, do the following: a. If the problem is an FTP server problem, then start the FTP server trace using the TRCTCPAPP command. b. Create the problem again. c. End the FTP connection. Refer to the Starting and stopping the FTP server. d. End the FTP server trace using the TRCTCPAPP command. e. Find a spooled file with the following characteristics: The file name is QTMFFTRC The username associated with the file is the name of the user who issued the TRCTCPAPP command.
Confidential
69697753.doc2 Page 70
9/28/2011
Wiggle Wireless
The trace is a spooled file in the default output queue of the system associated with the FTP server job. f. Send in that spooled file. g. If the problem was on the iSeries FTP client, a trace can be obtained using the DEBUG 100 client subcommand. h. When running the FTP client interactively, use the F6 (Print) key to create a spool file that contains a history of the FTP client subcommands entered, and the associated FTP server replies. When the FTP client is run in batch unattended mode, then this history of subcommands and server replies is written to the specified OUTPUT file. For more details, see "FTP as Batch Job".
Documentation and Links
Several good publications exist in downloadable PDF format at the following site: http://publib.boulder.ibm.com/infocenter/iseries/v5r3/index.jsp
Good publications to get here include: Digital Certificate Manager V5R3 book on the basics of DCM Redbook SG24-5659-00 - AS/400 Internet Security: Developing a Digital Certificate Infrastructure Redbook SG24-6168-00 - iSeries Wired Network Security OS/400 V5R1 DCM and Cryptographic Enhancements (highly recommend this Redbook-most of it is current in V5R3 and V5R4)
http://www.rsasecurity.com/rsalabs/faq/3-1-5.html RSA article on how large a key should be used in the RSA cryptosystem. iSeries DCM utilizes RSA cryptography in its key stores.
Confidential
69697753.doc2 Page 71
9/28/2011
Wiggle Wireless
Confidential
69697753.doc2 Page 72
9/28/2011
Das könnte Ihnen auch gefallen
- EDI Self Service Setup in Vendor CentralDokument10 SeitenEDI Self Service Setup in Vendor CentralGiorgio GandolfiNoch keine Bewertungen
- Database FilesDokument10 SeitenDatabase FilesUpendra KachhwahaNoch keine Bewertungen
- Essbase Security ImplementationDokument36 SeitenEssbase Security ImplementationAmit Sharma100% (1)
- GX1600 1600e SM Usa Exp Eu Em048n90dDokument46 SeitenGX1600 1600e SM Usa Exp Eu Em048n90dJadi PurwonoNoch keine Bewertungen
- Hololens - Presentation With VideoDokument23 SeitenHololens - Presentation With VideoAkshit GuptaNoch keine Bewertungen
- Migration From SQL Server 2008 To SQL Server 2014 Check ListDokument2 SeitenMigration From SQL Server 2008 To SQL Server 2014 Check ListPrasad ReddNoch keine Bewertungen
- Azure-SAP Solution IntellidocxDokument19 SeitenAzure-SAP Solution IntellidocxAndy Ng Chong SengNoch keine Bewertungen
- 5 Reasons For Account Payable AutomationDokument1 Seite5 Reasons For Account Payable AutomationManan PandyaNoch keine Bewertungen
- Fast Four S&C - Datasheet Architecture and Data Security PDFDokument5 SeitenFast Four S&C - Datasheet Architecture and Data Security PDFAnurag SinghNoch keine Bewertungen
- ISupplier Portal User HandbookDokument85 SeitenISupplier Portal User HandbookMarwan AladarbehNoch keine Bewertungen
- 10 Ways To Identify Accounts Payable FraudDokument7 Seiten10 Ways To Identify Accounts Payable FraudalfonsodzibNoch keine Bewertungen
- Intelligent Enterprise and SAP Business OneDokument21 SeitenIntelligent Enterprise and SAP Business OnepresisidigitalmoderenteknologiNoch keine Bewertungen
- HowTo Configure Counter DocumentsDokument10 SeitenHowTo Configure Counter DocumentsRohit DaswaniNoch keine Bewertungen
- Inspyrus - White PaperDokument8 SeitenInspyrus - White PaperBayCreativeNoch keine Bewertungen
- Account ReconciliationsDokument3 SeitenAccount ReconciliationsSamNoch keine Bewertungen
- Accounts Payable Automation Software For Food & Beverages IndustryDokument3 SeitenAccounts Payable Automation Software For Food & Beverages IndustryAPXPRESSNoch keine Bewertungen
- MicroStrategy Functions ReferenceDokument849 SeitenMicroStrategy Functions ReferenceArielNoch keine Bewertungen
- HMC DesktopDokument22 SeitenHMC DesktopgmawoyoNoch keine Bewertungen
- System Registration in SLDDokument12 SeitenSystem Registration in SLDShekhar GuptaNoch keine Bewertungen
- Workforce PlanDokument30 SeitenWorkforce PlanAbdur Rahman SiddiqueNoch keine Bewertungen
- ISupplier Portal TablesDokument2 SeitenISupplier Portal Tableskumar_amit_99Noch keine Bewertungen
- Oltp vs. Olap and How Do They Connect To SAP?: Last Updated On January 21, 2020Dokument12 SeitenOltp vs. Olap and How Do They Connect To SAP?: Last Updated On January 21, 2020FurqanNoch keine Bewertungen
- Archi User GuideDokument153 SeitenArchi User GuideMelissa Indah FiantyNoch keine Bewertungen
- Isupplier User ManualDokument29 SeitenIsupplier User ManualMarwan AladarbehNoch keine Bewertungen
- SustainabilityReport 2009Dokument116 SeitenSustainabilityReport 2009Siddarth ShettyNoch keine Bewertungen
- Quick View SchemaDokument8 SeitenQuick View SchemaJoe MarshallNoch keine Bewertungen
- Blogwhat Is 3 Way MatchingDokument5 SeitenBlogwhat Is 3 Way MatchingaluqueroNoch keine Bewertungen
- MISys - Guide - Level 1 B PDFDokument54 SeitenMISys - Guide - Level 1 B PDFcaplusincNoch keine Bewertungen
- EDI Fundamentals Feb2019 PDFDokument37 SeitenEDI Fundamentals Feb2019 PDFRocky GuptaNoch keine Bewertungen
- Report On Upskilling European IndustryDokument24 SeitenReport On Upskilling European IndustryLakshayNoch keine Bewertungen
- KWSH - Accounts Payable 28 - Oct-2020Dokument54 SeitenKWSH - Accounts Payable 28 - Oct-2020sureshNoch keine Bewertungen
- KWSH - Accounts PayableDokument53 SeitenKWSH - Accounts PayablesureshNoch keine Bewertungen
- TCZ - Presentation UST Global PDFDokument30 SeitenTCZ - Presentation UST Global PDFNarenNoch keine Bewertungen
- Exercise On Smart Forms Printing InvoicesDokument24 SeitenExercise On Smart Forms Printing InvoiceskkumartamanamNoch keine Bewertungen
- Accounts Payable Balance Sheet Entries: How Do They Show Up?Dokument9 SeitenAccounts Payable Balance Sheet Entries: How Do They Show Up?atia fawzyNoch keine Bewertungen
- Accounts Payable - SDD - 001Dokument95 SeitenAccounts Payable - SDD - 001KrishaNoch keine Bewertungen
- Transforming Warranty Processes With The IBMDokument13 SeitenTransforming Warranty Processes With The IBMClaudio Akira EndoNoch keine Bewertungen
- 10682-Integration With Fixed Assets - Purchasing - Payables - Projects - General Ledger - Etc-Presentation With Notes - 19Dokument79 Seiten10682-Integration With Fixed Assets - Purchasing - Payables - Projects - General Ledger - Etc-Presentation With Notes - 19Ali100% (1)
- SaaS Questionnaire - CloudDokument4 SeitenSaaS Questionnaire - CloudAhmed Hussain MohammedNoch keine Bewertungen
- Data QueueDokument11 SeitenData QueuesathishveeranNoch keine Bewertungen
- Carbon Capture Usage and Storage The New Driver of The EU Decarbonization PlanDokument9 SeitenCarbon Capture Usage and Storage The New Driver of The EU Decarbonization Planav1986362Noch keine Bewertungen
- Lab 6 - Encryption Using OpenPGP CompletedDokument10 SeitenLab 6 - Encryption Using OpenPGP CompletedabdallaNoch keine Bewertungen
- Mum PSP SQLDokument24 SeitenMum PSP SQLafonsobdsNoch keine Bewertungen
- 9-10 Integration Server Administrators GuideDokument1.034 Seiten9-10 Integration Server Administrators GuideRamakrishna Chandragiri100% (1)
- White Paper A Look Into Automating FTP and Batch ProcessesDokument11 SeitenWhite Paper A Look Into Automating FTP and Batch ProcessesrdngsNoch keine Bewertungen
- Smart by Gep Sap AdapterDokument6 SeitenSmart by Gep Sap AdapterjupudiguptaNoch keine Bewertungen
- Install Websphare PDFDokument100 SeitenInstall Websphare PDFZakaria AlmamariNoch keine Bewertungen
- 03 Business Structure Student VersionDokument11 Seiten03 Business Structure Student VersionjunkyardNoch keine Bewertungen
- Sap Invoice Management by Opentext (Vim) : Carlos de Los Santos - Director Ecm Entelgy Latam Abril, 2020Dokument53 SeitenSap Invoice Management by Opentext (Vim) : Carlos de Los Santos - Director Ecm Entelgy Latam Abril, 2020hector castroNoch keine Bewertungen
- AIIM Capture PosterDokument2 SeitenAIIM Capture PosterlogicpowerNoch keine Bewertungen
- 10-4 Error Messages ReferenceDokument2.710 Seiten10-4 Error Messages ReferenceJagadeeshwar ReddyNoch keine Bewertungen
- Winshuttle EasyAlternativetoLSMW Whitepaper enDokument15 SeitenWinshuttle EasyAlternativetoLSMW Whitepaper enYerukalasettyNoch keine Bewertungen
- KOFAX - Five Case Studies To Inspire Your Intelligent Automation StrategyDokument22 SeitenKOFAX - Five Case Studies To Inspire Your Intelligent Automation StrategyShirinda PradeeptiNoch keine Bewertungen
- Varan OBIA PDFDokument71 SeitenVaran OBIA PDFJuliaChenNoch keine Bewertungen
- Document Automation Tool - AIBridge MLDokument11 SeitenDocument Automation Tool - AIBridge MLAIBridge MLNoch keine Bewertungen
- Duplicate Invoices Function in SAP - SAP SIMPLE DocsDokument2 SeitenDuplicate Invoices Function in SAP - SAP SIMPLE DocsKrishna KumarNoch keine Bewertungen
- OracleKafka Build Scalable ETL Pipeline With ConnectorsDokument27 SeitenOracleKafka Build Scalable ETL Pipeline With ConnectorsRaghuNoch keine Bewertungen
- Migrating From Iseries To SQL ServerDokument46 SeitenMigrating From Iseries To SQL Serverjan2Noch keine Bewertungen
- S Solution Resources - White Papers108 - en UsDokument16 SeitenS Solution Resources - White Papers108 - en UsSohel AhmedNoch keine Bewertungen
- HowTo 101 Deploying Lancope StealthWatch With PxGridDokument42 SeitenHowTo 101 Deploying Lancope StealthWatch With PxGridAzfar ShabbirNoch keine Bewertungen
- SafeGuard Enterprise Evaluation Guide IaC - 7Dokument61 SeitenSafeGuard Enterprise Evaluation Guide IaC - 7PrateekGandhiNoch keine Bewertungen
- Data Sheet 6ES7234-4HE32-0XB0: General InformationDokument4 SeitenData Sheet 6ES7234-4HE32-0XB0: General Informationnik amirulNoch keine Bewertungen
- Chapter10 Econometrics DummyVariableModelDokument8 SeitenChapter10 Econometrics DummyVariableModelAbdullah KhatibNoch keine Bewertungen
- Knowledge 1Dokument1 SeiteKnowledge 1benciusilviuNoch keine Bewertungen
- Lab 3. DHT11Dokument5 SeitenLab 3. DHT11Maten NasradinNoch keine Bewertungen
- Winrar Password Remover 2015 Crack Plus Activation KeyDokument15 SeitenWinrar Password Remover 2015 Crack Plus Activation Keysiyamsanker722160% (5)
- Grammar & Spelling Check: CCNA 1 (v5.1 + v6.0) Chapter 1 Exam Answers 2017 - 100% FullDokument9 SeitenGrammar & Spelling Check: CCNA 1 (v5.1 + v6.0) Chapter 1 Exam Answers 2017 - 100% FullewmbtrakNoch keine Bewertungen
- T2K13 SeedsDokument16 SeitenT2K13 SeedsRyan Thomas100% (8)
- Ict Form 2Dokument12 SeitenIct Form 2farah7Noch keine Bewertungen
- Nurshath Dulal Wiki, Age, Photos, Height, Family, Net WorthDokument1 SeiteNurshath Dulal Wiki, Age, Photos, Height, Family, Net Worthraf0707066969Noch keine Bewertungen
- New Features Marvelous Designer 4Dokument45 SeitenNew Features Marvelous Designer 4tiff4ne1100% (1)
- 2 Chapter 1Dokument24 Seiten2 Chapter 1陳信宏Noch keine Bewertungen
- ANA Website Redesign FrameworkDokument1 SeiteANA Website Redesign FrameworkDemand Metric100% (1)
- Energies 12 00446Dokument35 SeitenEnergies 12 00446Vimal SamNoch keine Bewertungen
- IBM Analytics - Ladder To AIDokument31 SeitenIBM Analytics - Ladder To AIweeliyen5754Noch keine Bewertungen
- PMS ReportDokument51 SeitenPMS ReportMalavika K Murthy50% (2)
- Ac LGD User InstructionsDokument2 SeitenAc LGD User InstructionsGaudencio Alberco vilcayauriNoch keine Bewertungen
- Emerging Technologies in EducationDokument345 SeitenEmerging Technologies in EducationKhritish SwargiaryNoch keine Bewertungen
- Future of IT Audit Report - Res - Eng - 0219Dokument20 SeitenFuture of IT Audit Report - Res - Eng - 0219Immanuel GiuleaNoch keine Bewertungen
- As 2282.8-1999 Methods For Testing Flexible Cellular Polyurethane Determination of Force DeflectionDokument2 SeitenAs 2282.8-1999 Methods For Testing Flexible Cellular Polyurethane Determination of Force DeflectionSAI Global - APACNoch keine Bewertungen
- Bumble BizzDokument38 SeitenBumble BizzAxel RomanoNoch keine Bewertungen
- Theories & Practices in Local GovernanceDokument21 SeitenTheories & Practices in Local GovernanceLindsey MarieNoch keine Bewertungen
- Product Catalog: Smart Test Devices For Reliable Electric Power SystemsDokument32 SeitenProduct Catalog: Smart Test Devices For Reliable Electric Power SystemsbcqbaoNoch keine Bewertungen
- Comparing VMFS5 and VMFS6Dokument3 SeitenComparing VMFS5 and VMFS6Prasanth UnnikrishnanNoch keine Bewertungen
- 3 Compare The Algorithms:, A,, A, Find The Maximum Value ofDokument9 Seiten3 Compare The Algorithms:, A,, A, Find The Maximum Value ofLeming ShenNoch keine Bewertungen
- Pat Load Moment IndicatorDokument79 SeitenPat Load Moment IndicatorWilson torresNoch keine Bewertungen
- SAP B1 General Settings For Ivend RetailDokument12 SeitenSAP B1 General Settings For Ivend RetailVarun SirohiNoch keine Bewertungen
- How To Add A Node To An HACMP ClusterDokument6 SeitenHow To Add A Node To An HACMP ClusterSenthil GaneshNoch keine Bewertungen
- C674x CPU FeaturesDokument23 SeitenC674x CPU FeaturesbibiameenaNoch keine Bewertungen