Beruflich Dokumente
Kultur Dokumente
Introduction
Hochgeladen von
Avinash BajajOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Introduction
Hochgeladen von
Avinash BajajCopyright:
Verfügbare Formate
Chapter 1.
Cryptography
Introduction.
Cryptography (from Greek krypts, "hidden", and grphein, "to write") is, traditionally, the study of means of converting information from its normal, comprehensible form into an incomprehensible format, rendering it unreadable without secret knowledge the art of encryption. In the past, cryptography helped ensure secrecy in important communications, such as those of spies, military leaders, and diplomats. In recent decades, the field of cryptography has expanded its remit in two ways. Firstly, it provides mechanisms for more than just keeping secrets: schemes like digital signatures and digital cash, for example. Secondly, cryptography has come to be in widespread use by many civilians who do not have extraordinary needs for secrecy, although typically it is transparently built into the infrastructure for computing and telecommunications, and users are not aware of it. The study of how to circumvent the use of cryptography is called cryptanalysis, or codebreaking. Cryptography and cryptanalysis are sometimes grouped together under the umbrella term cryptology, encompassing the entire subject. In practice, "cryptography" is also often used to refer to the field as a whole; crypto is an informal abbreviation.
Chapter 2
Terminology
The original information which is to be protected by cryptography is called the plaintext. Encryption is the process of converting plaintext into an unreadable form, termed ciphertext, or, occasionally, a cryptogram. Decryption is the reverse process, recovering the plaintext back from the ciphertext. Enciphering and deciphering are alternative terms. A cipher is an algorithm for encryption and decryption. The exact operation of ciphers is normally controlled by a key some secret piece of information that customises how the ciphertext is produced. Protocols specify the details of how ciphers (and other cryptographic primitives) are to be used to achieve specific tasks. A suite of protocols, ciphers, key management, user-prescribed actions implemented together as a system constitute a cryptosystem; this is what an end-user interacts with, e.g. PGP or GPG. In ordinary parlance, a (secret) "code" is often used synonymously with "cipher". In cryptography, however, the term has a specialised technical meaning: codes are a method for classical cryptography, substituting larger units of text, typically words or phrases (e.g., "apple pie" replaces "attack at dawn"). In contrast, classical ciphers usually substitute or rearrange individual letters (e.g., "attack at dawn" becomes "buubdl bu ebxo" by substitution.). The secret information in a code is a specified codebook.
Chapter 3.
Cryptanalysis
A cryptanalyst might appear to be the natural adversary of a cryptographer, and to an extent this is true: one can view this contest all through the history of cryptography. However, it is possible, in fact preferable, to interpret the two roles as complementary: a thorough understanding of cryptanalysis is necessary to create secure cryptography. There are a wide variety of cryptanalytic attacks, and it is convenient to classify them. One distinction concerns what an attacker can know and do in order to learn secret information, e.g. does the cryptanalyst have access only to the ciphertext? Does he also know or can he guess some corresponding plaintexts? Or even: Can he choose arbitrary plaintexts to be encrypted? (see ciphertext only, known plaintext and chosen plaintext). While these example scenarios all view the cipher as an abstract black box, other attacks are based on the implementation of the cipher. If a cryptanalyst has access to, for example, timing or power consumption, he may be able to break a cipher otherwise resistant to analysis. If a cryptosystem uses a key or a password, it is at risk from an exhaustive search; this is very commonly the weakest point in such systems. Linear and differential cryptanalysis are general methods for symmetric key cryptography. When cryptography relies on hard mathematical problems, as is usually the case in asymmetric cryptography, algorithms for tasks such as factoring become potential tools for cryptanalysis.
Chapter 4.
THE PURPOSE OF CRYPTOGRAPHY Secure communications
Information security
Cryptography is commonly used for securing communications. Four desirable properties are: 1. Confidentiality, also known as secrecy: only an authorised recipient should be able to extract the contents of the message from its encrypted form. Otherwise, it should not be possible to obtain any significant information about the message contents. 2. Integrity: the recipient should be able to determine if the message has been altered during transmission. 3. Authentication: the recipient should be able to identify the sender, and verify that the purported sender actually did send the message. 4. Non-repudiation: the sender should not be able to deny sending the message. Cryptography can provide mechanisms to help achieve all of the above. However, some goals aren't always necessary, practical or even desirable in some contexts. For example, the sender of a message may wish to remain anonymous; clearly non-repudiation would be inappropriate in that case.
Chapter 5.
Symmetric key cryptography
Symmetric key algorithm
Symmetric key ciphers use the same key for encryption and decryption, or a little more precisely, the key used for decryption is "easy" to calculate from the key used for encryption. Other terms include "private-key", "one-key" and "single-key" cryptography. Symmetric key ciphers can be broadly grouped into block ciphers and stream ciphers. Stream ciphers encrypt one bit at a time, in contrast to a block cipher, which operates on a group of bits (a "block") of a certain length all in one go. Depending on the mode of operation, block ciphers can be implemented as self-synchronizing stream ciphers (CFB mode). Likewise, stream ciphers can be made to work on individual blocks of plaintext at a time. Thus, there is some duality between the two. The block ciphers DES, IDEA and AES, and the stream cipher RC4, are among the most well-known symmetric key ciphers. Other cryptographic primitives are sometimes classified as symmetric cryptography:
Cryptographic hash functions produce a hash of a message. While it should be easy to compute, it must be very difficult to invert (one-way), though other properties are usually needed as well. MD5 and SHA-1 are well-known hash functions.
Message authentication codes (MACs), also known as keyed-hash functions, are similar to hash functions, except that a key is needed to compute the hash. As the name suggests, they are commonly used for message authentication. They are often constructed from other primitives, such as block ciphers, unkeyed-hash functions or stream ciphers.
Symmetric key algorithm
DES
DES (the Data Encryption Standard) is a symmetric block cipher developed by IBM. The algorithm uses a 56-bit key to encipher/decipher a 64-bit block of data. The key is always presented as a 64-bit block, every 8th bit of which is ignored. However, it is usual to set each 8th bit so that each group of 8 bits has an odd number of bits set to 1. The algorithm is best suited to implementation in hardware, probably to discourage implementations in software, which tend to be slow by comparison. However, modern computers are so fast that satisfactory software implementations are readily available. DES is the most widely used symmetric algorithm in the world, despite claims that the key length is too short. Ever since DES was first announced, controversy has raged about whether 56 bits is long enough to guarantee security. The key length argument goes like this. Assuming that the only feasible attack on DES is to try each key in turn until the right one is found, then 1,000,000 machines each capable of testing 1,000,000 keys per second would find (on average) one key every 12 hours. Most reasonable people might find this rather comforting and a good measure of the strength of the algorithm. Those who consider the exhaustive key-search attack to be a real possibility (and to be fair the technology to do such a search is becoming a reality) can overcome the problem by using double or triple length keys. In fact, double length keys have been recommended for the financial industry for many years. Use of multiple length keys leads us to the Triple-DES algorithm, in which DES is applied three times. If we consider a triple length key to consist of three 56-bit keys K1, K2, K3 then encryption is as follows:
Encrypt with K3
Encrypt Decrypt
with with
K1 K2
Decryption is the reverse process: Decrypt with K1 Setting K3 equal to K1 in these processes gives us a double length key K1, K2. Setting K1, K2 and K3 all equal to K has the same effect as using a single-length (56-bit key). Thus it is possible for a system using triple-DES to be compatible with a system using single-DES. Decrypt Encrypt with with K3 K2
Chapter 6.
Public key cryptography Public key cryptography / Asymmetric key algorithm
Symmetric key encryption has a troublesome drawback two people who wish to exchange confidential messages must share a secret key. The key must be exchanged in a secure way, and not by the means they would normally communicate. This is usually inconvenient, and public-key (or asymmetric) cryptography provides an alternative. In public key encryption there are two keys used, a public and a private key, with the public key for encryption and the private key for decryption. It must be "difficult" to derive the private key from the public key. This means that someone can freely send their public key out over an insecure channel and yet be sure that only they can decrypt messages encrypted with it. Public key algorithms are usually based on hard mathematical problems. RSA, for example, relies on the (conjectured) difficulty of factorisation. For efficiency reasons, hybrid encryption systems are used in practice; a key is exchanged using a public-key cipher, and the rest of the communication is encrypted using a symmetric-key algorithm (which is typically much faster). Elliptic curve cryptography is a type of public-key algorithm that may offer efficiency gains over other schemes. Asymmetric cryptography also provides mechanisms for digital signatures, which are way to establish with high confidence (under the assumption that the relevant private key has not been compromised in any way) that the message received was sent by the claimed sender. Such signatures are often, in law or by implicit inference, seen as the digital equivalent of physical signatures on paper documents. In a technical sense, they are not as there is no physical contact nor connection between the 'signer' and the 'signed'. Properly used high quality designs and implementations are capable of a very high degree
of assurance, likely exceeding any but the most careful physical signature. Examples of digital signature protocols include DSA and ElGamal. Digital signatures are central to the operation of public key infrastructure and many network security schemes (e.g., Kerberos, most VPNs, etc). Like encryption, hybrid algorithms are typically used in practice; rather than signing an entire document, a cryptographic hash of the document is signed instead.
Public key cryptography / Asymmetric key algorithm
RSA
RSA is a public key algorithm invented by Rivest, Shamir and Adleman. The key used for encryption is different from (but related to) the key used for decryption. The algorithm is based on modular exponentiation. Numbers e, d and N are chosen with the property that if A is a number less than N, then (Ae mod N)d mod N = A. This means that you can encrypt A with e and decrypt using d. Conversely you can encrypt using d and decrypt using e (though doing it this way round is usually referred to as signing and verification). The pair of numbers (e,N) is known as the public key and can be published. The pair of numbers (d,N) is known as the private key and must be kept secret. The number e is known as the public exponent, the number d is known as the private exponent, and N is known as the modulus. When talking of key lengths in connection with RSA, what is meant is the modulus length. An algorithm that uses different keys for encryption and decryption is said to be asymmetric. Anybody knowing the public key can use it to create encrypted messages, but only the owner of the secret key can decrypt them. Conversely the owner of the secret key can encrypt messages that can be decrypted by anybody with the public key. Anybody successfully decrypting such messages can be sure that only the owner of the secret key could have encrypted them. This fact is the basis of the digital signature technique. Without going into detail about how e, d and N are related, d can be deduced from e and N if the factors of N can be determined. Therefore the security of RSA depends on the difficulty of factorizing N. Because factorization is believed to be a hard problem, the
longer N is, the more secure the cryptosystem. Given the power of modern computers, a length of 768 bits is considered reasonably safe, but for serious commercial use 1024 bits is recommended. The problem with choosing long keys is that RSA is very slow compared with a symmetric block cipher such as DES, and the longer the key the slower it is. The best solution is to use RSA for digital signatures and for protecting DES keys. Bulk data encryption should be done using DES.
The Mathematical Guts of RSA Encryption
The RSA algorithm was invented in 1978 by Ron Rivest, Adi Shamir, and Leonard Adleman.
Here's the relatively easy to understand math behind RSA public key encryption. 1. Find P and Q, two large (e.g., 1024-bit) prime numbers. 2. Choose E such that E is greater than 1, E is less than PQ, and E and (P-1)(Q-1) are relatively prime, which means they have no prime factors in common. E does not have to be prime, but it must be odd. (P-1)(Q-1) can't be prime because it's an even number. 3. Compute D such that (DE - 1) is evenly divisible by (P-1)(Q-1). Mathematicians write this as DE = 1 (mod (P-1)(Q-1)), and they call D the multiplicative inverse of E. This is easy to do -- simply find an integer X which causes D = (X(P-1)(Q1) + 1)/E to be an integer, then use that value of D. 4. The encryption function is C = (T^E) mod PQ, where C is the ciphertext (a positive integer), T is the plaintext (a positive integer), and ^ indicates exponentiation. The message being encrypted, T, must be less than the modulus, PQ. 5. The decryption function is T = (C^D) mod PQ, where C is the ciphertext (a positive integer), T is the plaintext (a positive integer), and ^ indicates exponentiation. Your public key is the pair (PQ, E). Your private key is the number D (reveal it to no one). The product PQ is the modulus (often called N in the literature). E is the public exponent. D is the secret exponent.
You can publish your public key freely, because there are no known easy methods of calculating D, P, or Q given only (PQ, E) (your public key). If P and Q are each 1024 bits long, the sun will burn out before the most powerful computers presently in existence can factor your modulus into P and Q.
An Example of the RSA Algorithm P = 61 Q = 53 <- first prime number (destroy this after computing E and D) <- second prime number (destroy this after computing E and D)
PQ = 3233 <- modulus (give this to others) E = 17 <- public exponent (give this to others)
D = 2753 <- private exponent (keep this secret!)
Your public key is (E,PQ). Your private key is D.
The encryption function is:
encrypt(T) = (T^E) mod PQ = (T^17) mod 3233
The decryption function is:
decrypt(C) = (C^D) mod PQ = (C^2753) mod 3233
To encrypt the plaintext value 123, do this:
encrypt(123) = (123^17) mod 3233 = 337587917446653715596592958817679803 mod 3233
= 855
To decrypt the ciphertext value 855, do this:
decrypt(855) = (855^2753) mod 3233 = 123
One way to compute the value of 855^2753 mod 3233 is like this:
2753 = 101011000001 base 2, therefore
2753 = 1 + 2^6 + 2^7 + 2^9 + 2^11 = 1 + 64 + 128 + 512 + 2048
Consider this table of powers of 855:
855^1 = 855 (mod 3233) 855^2 = 367 (mod 3233) 855^4 = 367^2 (mod 3233) = 2136 (mod 3233) 855^8 = 2136^2 (mod 3233) = 733 (mod 3233) 855^16 = 733^2 (mod 3233) = 611 (mod 3233) 855^32 = 611^2 (mod 3233) = 1526 (mod 3233) 855^64 = 1526^2 (mod 3233) = 916 (mod 3233) 855^128 = 916^2 (mod 3233) = 1709 (mod 3233) 855^256 = 1709^2 (mod 3233) = 1282 (mod 3233) 855^512 = 1282^2 (mod 3233) = 1160 (mod 3233) 855^1024 = 1160^2 (mod 3233) = 672 (mod 3233) 855^2048 = 672^2 (mod 3233) = 2197 (mod 3233)
Given the above, we know this:
855^2753 (mod 3233) = 855^(1 + 64 + 128 + 512 + 2048) (mod 3233) = 855^1 * 855^64 * 855^128 * 855^512 * 855^2048 (mod 3233) = 855 * 916 * 1709 * 1160 * 2197 (mod 3233) = 794 * 1709 * 1160 * 2197 (mod 3233) = 2319 * 1160 * 2197 (mod 3233) = 184 * 2197 (mod 3233) = 123 (mod 3233) = 123
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Data Privacy - 30 Ways To Love Yourself OnlineDokument34 SeitenData Privacy - 30 Ways To Love Yourself Onlinedyake04Noch keine Bewertungen
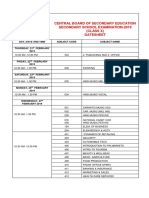
- Central Board of Secondary Education Secondary School Examination-2019 (Class X) DatesheetDokument4 SeitenCentral Board of Secondary Education Secondary School Examination-2019 (Class X) DatesheetPriyanka SharmaNoch keine Bewertungen
- FriendshipDokument2 SeitenFriendshipnitrvsNoch keine Bewertungen
- WIFIDokument18 SeitenWIFIAvinash BajajNoch keine Bewertungen
- Instructions For Seminar-Computer EngineeringDokument44 SeitenInstructions For Seminar-Computer EngineeringAvinash BajajNoch keine Bewertungen
- E TICKETDokument42 SeitenE TICKETSachin Joshi100% (1)
- Cyber Security: (Prof. Ashok K. Bhateja, IIT Delhi)Dokument10 SeitenCyber Security: (Prof. Ashok K. Bhateja, IIT Delhi)Jatin GoyalNoch keine Bewertungen
- Security Issues in Mobile ComputingDokument62 SeitenSecurity Issues in Mobile Computingnehabhende2001Noch keine Bewertungen
- محتويات أساسيات الحاسوب والأنترنتDokument8 Seitenمحتويات أساسيات الحاسوب والأنترنتAdel MahmoudNoch keine Bewertungen
- Importance of Network SecurityDokument2 SeitenImportance of Network SecurityLuck JayNoch keine Bewertungen
- Ecommerce Slides Unit 5Dokument65 SeitenEcommerce Slides Unit 5Aayush HumagainNoch keine Bewertungen
- Sysadmin Magazine October 2021Dokument32 SeitenSysadmin Magazine October 2021TonyTonySNoch keine Bewertungen
- ProxyDokument43 SeitenProxyАнонимни ЧовекNoch keine Bewertungen
- The Dark Side of The WebDokument16 SeitenThe Dark Side of The WebRahul VermaNoch keine Bewertungen
- Chapter 6Dokument35 SeitenChapter 6Fedawak ObsaNoch keine Bewertungen
- 22SCE151Cryptography and Network SecurityDokument3 Seiten22SCE151Cryptography and Network SecuritytnagaviNoch keine Bewertungen
- Ghack Crypto Presentation NECDokument25 SeitenGhack Crypto Presentation NECRajendra PrasadNoch keine Bewertungen
- Quality RequirementsDokument100 SeitenQuality RequirementsAnonymous 0zVzjl50% (2)
- CS8792-Cryptography and Network Security - Moodle - TopicsDokument3 SeitenCS8792-Cryptography and Network Security - Moodle - TopicsanantNoch keine Bewertungen
- Literaturereview Proposed System Cloud Security System Model Development Modules Experimental Results Advantages Conclusion ReferencesDokument17 SeitenLiteraturereview Proposed System Cloud Security System Model Development Modules Experimental Results Advantages Conclusion ReferencesManoj KumarNoch keine Bewertungen
- Decrypt MD5 Using The Following Code in PHPDokument3 SeitenDecrypt MD5 Using The Following Code in PHPTechnoTiger100% (3)
- SHA - 256 (Secured Hashing Algorithm)Dokument8 SeitenSHA - 256 (Secured Hashing Algorithm)sri harshaphaniNoch keine Bewertungen
- PKCSDokument5 SeitenPKCSAntonio Duplat JrNoch keine Bewertungen
- Phishing AttackDokument17 SeitenPhishing AttackNaidnic SecNoch keine Bewertungen
- Quiz For Chapter 4 IASDokument5 SeitenQuiz For Chapter 4 IASeliza marie luisNoch keine Bewertungen
- CEH v10 Module 13 Hacking Web Servers PDFDokument25 SeitenCEH v10 Module 13 Hacking Web Servers PDFDavid AmanNoch keine Bewertungen
- Vyatta Open-VpnDokument10 SeitenVyatta Open-Vpnduranduran11100% (1)
- Unidad 1, ISP - Traffic - HourlyDokument5 SeitenUnidad 1, ISP - Traffic - HourlyRafael Adrian Báez RamírezNoch keine Bewertungen
- Network Security Case StudyDokument13 SeitenNetwork Security Case StudyshankugeetuNoch keine Bewertungen
- Cyber Security SeminarDokument40 SeitenCyber Security SeminarJethu Singh100% (1)
- Olin Wong ID# 008435258: Assignment 04Dokument5 SeitenOlin Wong ID# 008435258: Assignment 04Vikram KumarNoch keine Bewertungen
- Outline: Friends and Enemies: Alice, Bob, TrudyDokument3 SeitenOutline: Friends and Enemies: Alice, Bob, Trudychuchu mangeusNoch keine Bewertungen
- PHISHINGDokument10 SeitenPHISHINGPrimael BouazoNoch keine Bewertungen
- Diffie Hellman WriteupDokument3 SeitenDiffie Hellman WriteupSumitThoratNoch keine Bewertungen
- Chapter Four: E-Commerce Security and CryptographyDokument21 SeitenChapter Four: E-Commerce Security and Cryptographyiyasu ayenekuluNoch keine Bewertungen