Beruflich Dokumente
Kultur Dokumente
Technology Management
Hochgeladen von
omar__abdullahOriginalbeschreibung:
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
Technology Management
Hochgeladen von
omar__abdullahCopyright:
Verfügbare Formate
1
TECHNOLOGY MANAGEMENT
[Information Technology]
OMAR BAKODAH FAISAL AL-JAMMAZ SALEM AL-DOSSARY
Contents
Introduction 3
Information Technology Management 3 IT Service Management 4 Security Management 5
List of Information Technology Fields 6 Intellectual Property 6
Copyright Industrial Property 7 7
Patent Laws
Conditions of Patentability
9
Types of Patents 9
Exclusive Rights Compulsory License
10 10
References
11
Introduction
I. Information Technology Management:
Information Technology Management is concerned with exploring and understanding Information Technology as a corporate resource that determines both the strategic and operational capabilities of the firm in designing and developing products and services for maximum customer satisfaction, corporate productivity, profitability and competitiveness. Under IT management there are five sub-categories: 1. 2. 3. 4. 5. IT Governance IT service Management Financial Management Security Management Risk Management
1) IT Governance: IT Governance or ICT (Information & Communications Technology) Governance, is a subset discipline of Corporate Governance focused on information technology (IT) systems and their performance and risk management. The rising interest in IT governance is partly due to compliance initiatives, as well as the acknowledgment that IT projects can easily get out of control and profoundly affect the performance of an organization. But to include foundational mechanism IT governance institute expands the statement: The leadership and organizational structures and processes that ensure that the organizations IT sustains and extends the organizations strategies and objectives."
The discipline of information technology governance derives from corporate governance and deals primarily with the connection between business focus and IT management of an organization. It highlights the importance of IT related matters in contemporary organizations and states that strategic IT decisions should be owned by the corporate board, rather than by the chief information officer or other IT managers. 2) IT Service Management: IT Service Management (ITSM) is a discipline for managing information technology (IT) systems, philosophically centered on the customer's perspective of IT's contribution to the business. ITSM stands in deliberate contrast to technology-centered approaches to IT management and business interaction. The following represents a characteristic statement from the ITSM literature: Providers of IT services can no longer afford to focus on technology and their internal organization, they now have to consider the quality of the services they provide and focus on the relationship with customers. ITSM is process-focused and in this sense have ties and common interests with process improvement movement frameworks and methodologies. For example it relates to: TQM Six Sigma Business Process Management CMMI TSM is related to the field of Management Information Systems (MIS) in scope. However, ITSM has a distinct practitioner point of view, and is more introspective (i.e. IT thinking about the delivery of IT to the business) as opposed to the more academic and outward facing connotation of MIS 3) Financial Management: It is the management of the finances of a business / organization in order to achieve financial objectives. Taking a commercial business as the most common organizational structure, the key objectives of financial management would be to: Create wealth for the business Generate cash Provide an adequate return on investment bearing in mind the risks that the business is taking and the resources invested There are three key elements to the process of financial management:
(1) Financial Planning Management need to ensure that enough funding is available at the right time to meet the needs of the business. In the short term, funding may be needed to invest in equipment and stocks, pay employees and fund sales made on credit.
(2) Financial Control Financial control is a critically important activity to help the business ensure that the business is meeting its objectives. Financial control addresses questions such as: Are assets being used efficiently? Are the businesses assets secure? Do management act in the best interest of shareholders and in accordance with business rules? (3) Financial Decision-making The key aspects of financial decision-making relate to investment, financing and dividends: Investments must be financed in some way however there are always financing alternatives that can be considered. For example it is possible to raise finance from selling new shares, borrowing from banks or taking credit from suppliers A key financing decision is whether profits earned by the business should be retained rather than distributed to shareholders via dividends. If dividends are too high, the business may be starved of funding to reinvest in growing revenues and profits further. 4) Security Management: Security Management is a broad field of management related to asset management, physical security and human resource safety functions. It entails the identification of an organization's information assets and the development, documentation and implementation of policies, standards, procedures and guidelines. In network management it is the set of functions that protects telecommunications networks and systems from unauthorized access by persons, acts, or influences and that includes many sub functions, such as creating, deleting, and controlling security services and mechanisms; distributing security-relevant information; reporting security-relevant events;
controlling the distribution of cryptographic keying material; and authorizing subscriber access, rights, and privileges. Management tools such as information classification, risk assessment and risk analysis are used to identify threats, classify assets and to rate system vulnerabilities so that effective control can be implemented. Under security management there are:
Access control Alarm management Physical Security Physical Security Professional Security policy
5) Risk Management: Risk management is a structured approach to manage uncertainty related to a threat, a sequence of human activities including: risk assessment, strategies development to manage it, and mitigation of risk using managerial resources. The objective of risk management is to reduce different risks related to a preselected domain to the level accepted by society. It may refer to numerous types of threats caused by environment, technology, humans, organizations and politics. Areas of risk management include: Enterprise risk management Risk management to project management
II. List of Information technology fields.
Technology management information system has a broad range of fields. Five of them are listed below: Customer Relationship Management (CRM) Human Resource Management System (HRMS) Product Lifecycle Management (PLM) Knowledge Management System (KMS) Enterprise Content Management (ECM)
III.
Intellectual Property:
Intellectual property refers to creations of the mind: inventions, literary and artistic works, and symbols, names, images, and designs used in commerce. Intellectual property is divided into two categories: Industrial property, which includes inventions (patents), trademarks, industrial designs, and geographic indications of source; and Copyright, which includes literary and artistic works such as novels, poems and plays, films, musical works, artistic works such as drawings, paintings, photographs and sculptures, and architectural designs. Rights related to copyright include those of performing artists in their performances, producers of phonograms in their recordings, and those of broadcasters in their radio and television programs. The two branches of Intellectual Property:
1. Copyright 2. Industrial Property
Copyright:
Copyright relates to artistic creations, such as poems, novels, music, paintings, and cinematographic works. In most European languages other than English, copyright is known as authors rights. The expression copyright refers to the main act which, in respect of literary and artistic creations, may be made only by the author or with his authorization. That act is the making of copies of the literary or artistic work, such as a book, a painting, a sculpture, a photograph, or motion picture. The second expression, authors rights refers to the person whose the creator of the artistic work, its author, thus underlining the fact, recognized in most laws, that the author has certain specific rights in his creation, such as the right to prevent a distorted reproduction, which only he can exercise, whereas other rights, such as the right to make copies, can be exercised by other persons, for example, a publisher who has obtained a license to this effect from the author.
Industrial Property:
Industrial property shall be understood in the broadest sense and shall apply not only to industry and commerce proper, but likewise to agricultural and extractive industries and to
all manufactured or natural products, for example, wines, grain, tobacco leaf, fruit, cattle, minerals, mineral waters, beer, flowers, and flour. Industrial property takes a range of forms, the main types of which will be outlined in this booklet. These include patents to protect inventions; and industrial designs, which are aesthetic creations determining the appearance of industrial products. Industrial property also covers trademarks, service marks, layout-designs of integrated circuits, commercial names and designations, as well as geographical indications, and protection against unfair competition. In some of these, the aspect of intellectual creation, although existent, is less clearly defined. What counts here is that the object of industrial property typically consists of signs transmitting information, in particular to consumers, as regards products and services offered on the market. Protection is directed against unauthorized use of such signs likely to mislead consumers, and against mislead practices in general.
Intellectual Property with regard to integrated circuits
The question of the type of protection to be granted to the layout design or topography of integrated circuits is relatively new. Although prefabricated components of electrical circuitry have been used for a long time in the manufacture of electrical equipment (such as radios), large-scale integration of a multitude of electrical functions in a very small component became possible as a result of advances in semiconductor technology. Integrated circuits are manufactured in accordance with very detailed plans or layout designs. The layout designs of integrated circuits are creations of the human mind. They are usually the result of vast investment, of both expertise and financial resources. There is a continuing need for the creation of new layout designs that reduce the dimensions of existing integrated circuits and simultaneously increase their functions. The smaller an integrated circuit, the less material is needed for its manufacture, and the smaller the space needed to accommodate it. Integrated circuits are used in a wide range of products, including articles of everyday use, such as watches, television sets, washing machines and cars, as well as sophisticated computers and servers.
IV. Patent Laws:
Most laws dealing with the protection of inventions do not actually define the notion of an invention. , however, A number of countries define inventions as new solutions to technical problems. The problem may be old or new, but the solution, in order to merit the name of invention, must be a new one. also discovering something that already exists in nature, such as a previously unknown plant variety, is not an invention. Human intervention must be added. So the process for extraction of a new substance from a plant may be an invention. Protection of inventions under patent law does not require that the invention be represented in a physical embodiment.
Patents, also referred to as patents for invention, are the most widespread means of protecting the rights of inventors. Simply put, a patent is the right granted to an inventor by a State, or by regional office acting for several States, which allows the inventor to exclude anyone else from commercially exploiting his invention for a limited period, generally 20 years. By granting an exclusive right, patents provide incentives to individuals, offering them recognition for their creativity and material reward for their marketable inventions. These incentives encourage innovation, which in turn contributes to the continuing enhancement of the quality of human life. In return for the exclusive right, the inventor must adequately disclose the patented invention to the public, so that others can gain the new knowledge and can further develop the technology. In order to obtain a patent for an invention, the inventor submits an application to the national or regional patent office. In the application the inventor must describe the invention in detail and compare it with previous existing technologies in the same field in order to demonstrate its newness. Not all inventions are patentable.
Conditions of patentability:
Industrial Applicability (utility). The invention must be of practical use, Or capable of some kind of industrial application. Novelty. It must show some new characteristic that is not known in the Body of existing knowledge in its technical field. Inventive step (non-obviousness). It must show an inventive step that could Not be deduced by a person with average knowledge of the technical field. Patentable subject matter. The invention must fall within the scope of Patentable subject matter as defined by national law. This varies from one Country to another.
V. Types Of Patents
There are two types of patents.
o Product Patent o Process Patent
It is customary to distinguish between inventions that consist of products and Inventions that consist of processes.
10
I.
Product Patent:
The creation of a new alloy is an example of a product invention.
II.
Process Patent:
The invention of a new method or process of making a Known or new alloy is a process invention.
VI. Exclusive Rights
The patents owner exclusive rights are: 1. In the case of a product patent, the right to prevent third parties without The owners consent from making, using, offering for sale, selling or importing For these purposes the product. 2. In the case of a process patent, the right to prevent third parties without The owners consent from using the process; and to prevent third parties from Using, offering for sale, selling or importing for these purposes the products Which were obtained directly by that process?
Compulsory License:
A compulsory license is an authorization to exploit the invention given by a Governmental authority. It is generally issued only in very special cases, defined In the law, and only where the entity wishing to exploit the patented invention Is unable to obtain the authorization of the owner of the patent. The conditions regarding the granting of compulsory licenses are regulated in detail by laws that provide for them. The decision to grant a compulsory license must provide for an adequate remuneration of the patentee. The decision may be the subject of an appeal.
11
References
1. M.K. Badawy (1998), Technology Management Education: Alternative Models. California Management Review.
2. http://www.gartner.com/it/products/research/topi
cs/topics.jsp
3. http://www.wipo.int
12
Das könnte Ihnen auch gefallen
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Dessler 03Dokument13 SeitenDessler 03Yose DjaluwarsaNoch keine Bewertungen
- Report On Business LetterDokument28 SeitenReport On Business LetterAnum SheikhNoch keine Bewertungen
- C TSCM62 65 Sample QuestionsDokument7 SeitenC TSCM62 65 Sample QuestionsAnand Iyer100% (2)
- Import Export DivisionDokument5 SeitenImport Export DivisionSanskar TiwariNoch keine Bewertungen
- Strategic Assignment FullDokument50 SeitenStrategic Assignment FullFitriana AnnisaNoch keine Bewertungen
- Sip Project ReportDokument45 SeitenSip Project ReportRachit KhareNoch keine Bewertungen
- OPER312 Exercise5Dokument4 SeitenOPER312 Exercise5Berk AlbakerNoch keine Bewertungen
- Bam 040 Demand and Supply PT.2Dokument14 SeitenBam 040 Demand and Supply PT.2Vkyla BataoelNoch keine Bewertungen
- Olaf Abel Ethylene ApcDokument32 SeitenOlaf Abel Ethylene Apcasamad54Noch keine Bewertungen
- Diamonds+in+the+Sky PDFDokument70 SeitenDiamonds+in+the+Sky PDFRaffi Delic100% (5)
- Vishnu AgenciesDokument2 SeitenVishnu AgenciesBack-End MarketingNoch keine Bewertungen
- Thư Tín - NN5-2020 - UpdatedDokument60 SeitenThư Tín - NN5-2020 - UpdatedK59 Nguyen Minh ChauNoch keine Bewertungen
- Essay BusinessDokument2 SeitenEssay Businessali basitNoch keine Bewertungen
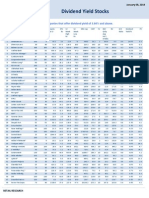
- High Dividend Yield StocksDokument3 SeitenHigh Dividend Yield StockskaizenlifeNoch keine Bewertungen
- B40Dokument7 SeitenB40ambujg0% (1)
- Quality Preliminary ReportDokument16 SeitenQuality Preliminary ReportNilabh OholNoch keine Bewertungen
- Birla Navya EOI Form - Amoda - R4Dokument4 SeitenBirla Navya EOI Form - Amoda - R4sushil aroraNoch keine Bewertungen
- Case General Motors Onstar ProjectDokument10 SeitenCase General Motors Onstar ProjectSergio IvánNoch keine Bewertungen
- PARTNERSHIP2Dokument13 SeitenPARTNERSHIP2Anne Marielle UyNoch keine Bewertungen
- CDR Mechanical Engineer 1 No SummaryDokument24 SeitenCDR Mechanical Engineer 1 No SummaryZizo Awad100% (1)
- Statement For Contract # 1019396517: Rana Shameem AkhtarDokument4 SeitenStatement For Contract # 1019396517: Rana Shameem AkhtarZeshan Khan jeeNoch keine Bewertungen
- Vyshnavikambar@Yahoo Com 193481Dokument3 SeitenVyshnavikambar@Yahoo Com 193481sudhirreddy1982Noch keine Bewertungen
- Joselito Resumae UpdatedDokument8 SeitenJoselito Resumae Updatedjoselito ruantoNoch keine Bewertungen
- Cold Box Overview enDokument18 SeitenCold Box Overview enSasa DjordjevicNoch keine Bewertungen
- ObjectionDokument10 SeitenObjectionMy-Acts Of-SeditionNoch keine Bewertungen
- Unit 2 Consumer BehaviourDokument14 SeitenUnit 2 Consumer Behaviournileshstat5Noch keine Bewertungen
- CE462-CE562 Principles of Health and Safety-Birleştirildi PDFDokument663 SeitenCE462-CE562 Principles of Health and Safety-Birleştirildi PDFAnonymous MnNFIYB2Noch keine Bewertungen
- Twofour54 Tadreeb Corporate Overview PDFDokument17 SeitenTwofour54 Tadreeb Corporate Overview PDFSolo PostNoch keine Bewertungen
- Gr. Reggane Nord - Tender No - cfb-0295-20 - Provision of Tubular Running ServicesDokument1 SeiteGr. Reggane Nord - Tender No - cfb-0295-20 - Provision of Tubular Running ServicesOussama AmaraNoch keine Bewertungen
- Ogutu - The Role of National Housing Corporation in The Provision of Housing in KenyaDokument95 SeitenOgutu - The Role of National Housing Corporation in The Provision of Housing in KenyaboneylouNoch keine Bewertungen