Beruflich Dokumente
Kultur Dokumente
SAP Security Day 1 1st Half Anwar
Hochgeladen von
Krishna KoduruOriginaltitel
Copyright
Verfügbare Formate
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenCopyright:
Verfügbare Formate
SAP Security Day 1 1st Half Anwar
Hochgeladen von
Krishna KoduruCopyright:
Verfügbare Formate
Confidential Copyright IBM Corporation 2004
IBM Global Services
Objectives
What is security ? Security threats & measures to combat threats Types of security
Confidential Copyright IBM Corporation 2004
IBM Global Services
A who's who Security , Secured System, Threats, Safeguards
Confidential Copyright IBM Corporation 2004
IBM Global Services
What is Security ?
Dictionary meaning
Freedom from risk or danger; safety.
In Other Words
The process of ensuring confidentiality, integrity, and availability of computers, their programs, hardware devices, and data.
Confidential Copyright IBM Corporation 2004
IBM Global Services
A secure System and Threat
A secure System It is a system which does exactly what we want it to do and nothing that we don't want it to do even when someone else tries to make it behave differently. Threat It is an act or event that has the potential to cause a failure of security .
Confidential Copyright IBM Corporation 2004
IBM Global Services
Why I am here and how do I achieve it ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
A security Consultant should know
What To Secure
What
Why to Secure i.e.. Importance of the Data/Article etc. Why
Who could attack the system / challenge the security of the system
From Whom
Confidential Copyright IBM Corporation 2004
IBM Global Services
Security Achieved By
Keeping Unauthorized Person out of the System
Keeping People out of Places Where They Should Not Be
Safeguarding the Data from Damage or Loss
Confidential Copyright IBM Corporation 2004
IBM Global Services
So, Do I understand ? .. I need to implement some safeguards to avoid threats and thats how I achieve my security goals ?
. Lets see the big picture
Confidential Copyright IBM Corporation 2004
IBM Global Services
The BIG Picture ..
Access Control Firewall
Encryption Confidentiality Integrity
Threats
Safe Guards
Goals
Availability
1. 2. 3. 4. 5. 6.
Tampering Planting Eves- Dropping Penetration Authorization Violation O/s Cracking
Digital Certificate
Obligation Anti-Virus
Security O/S Monitor Hardening
Confidential Copyright IBM Corporation 2004
IBM Global Services
Security - Under The Microscope .
Confidential Copyright IBM Corporation 2004
IBM Global Services
Types Of Security
Organizational Policies Monitoring Training Disaster Plan
Organizational
Physical
Server Facilities Building Fire Alarm Camera
Program Level O/S Level
Patches , O/S Hardening (Authentication, O/S Hardening, Virus Guard, Spam Blocker) (Authentication, Access Control) (Authentication , Firewall , Encryption, Security Monitor)
Confidential Copyright IBM Corporation 2004
Technical
Database
N/W security
|
IBM Global Services
A known story with an extension
Lets recollect the Rabbit Tortoise story again. Once the Tortoise won the run the Rabbit wants to congratulate the tortoise and so the rabbit wants to gift a piece of memento to the tortoise. The Rabbit needs to carry the memento to the Tortoises home. Our point of focus would be.. 1. Is the rabbit secured at its own home? 2. Is the tortoise secured at its own home? 3. Is the memento secured ? 4. The road through which the rabbit needs to go, is that secured ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
If we co-relate the rabbit and the tortoise to our computer world
Remember
Any computer is not secured Security can be void if The applications are not secured ( consider the hands by which the rabbit carries the gift to tortoise) The O/S is not secured (the house of the rabbit or the tortoise) The database and data is not secured ( The container from where the rabbit takes the piece of gift) The network path is not secured ( the path through which the rabbit needs to run)
Confidential Copyright IBM Corporation 2004
IBM Global Services
Lets understand these challenges in our known terms and their safeguards
Confidential Copyright IBM Corporation 2004
IBM Global Services
Lets introduce Program Security
Confidential Copyright IBM Corporation 2004
IBM Global Services
Computer programs are the first line of defense in computer security, since programs provide logical controls. Programs, however, are subject to error, which can affect computer security.
Exact Correct
A computer program is correct if it meets the requirements for which it was designed. Finally, a program is exact if it performs only those operations specified by requirements.
Complete
A program is complete if it meets all requirements.
Confidential Copyright IBM Corporation 2004
IBM Global Services
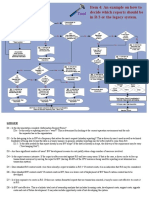
Application Security Threat Flow
Identify Security Objectives
Application Overview
Identify Vulnerabilities
Decompose Application
Identify Threats
Confidential Copyright IBM Corporation 2004
IBM Global Services
Application Security
Virus, Spy ware Injection Attacks
Architecture D e s i g n
Authentication Error
Cross Site Scripting
T e s t
Application Security
Deny Of Service
Web Defacement
Implementation
Trojan
Path Traversal
Confidential Copyright IBM Corporation 2004
IBM Global Services
My Program is Secured .. But is my O/S secured ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
How as operating system is build?
Operating systems, structured specifically, for security are built in a kernelized manner.
A kernelized operating system is designed in layers. The innermost layer provides direct access to the hardware facilities of the computing system and exports very primitive abstract objects to the next layer. Lets visualize that ..
Confidential Copyright IBM Corporation 2004
IBM Global Services
Security of operating systems
To avoid threats we apply different Patches and Harden our O/S.
O/S Patch O/s Hardening
OS Kernel
Confidential Copyright IBM Corporation 2004
IBM Global Services
The container story . Database damage threats
Confidential Copyright IBM Corporation 2004
IBM Global Services
Database Threats
Data Overwrite
User Conflict
Data Loss
Database
Improper Change/Alteration of Data
Scrambled Data
Unauthorized Changes
Confidential Copyright IBM Corporation 2004
IBM Global Services
Why to Protect a Data Base Intelligent Threats
Name Age
Data Base
No Of Cust.
Unit Price
inference
Aggregation
Customer Data
Total Market Share
Confidential Copyright IBM Corporation 2004
IBM Global Services
Database Vulnerabilities
Basically database security can be broken down into the following key points of interest. Server Security
Server security is the process of limiting actual access to the database server itself, The basic idea is this, "You can't access what you can't see".
Database Connections
Ensure that every connection uses it's own unique user to access the shared data
Table Access Control
Properly using Table access control will require the collaboration of both system administrator and database developer
Restricting Database Access
Mainly into the network access of the system. Specifically targeting Internet based databases, since they have been the most recent targets of attacks.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Database Web-Security
For Web security, you must address three primary areas:
Session security -- ensuring that data is not intercepted as it is broadcast over the Internet or Intranet
User-authentication security -- ensuring login security that prevents unauthorized access to information Server security -- ensuring security relating to the actual data or private HTML files stored on the server
Confidential Copyright IBM Corporation 2004
IBM Global Services
Knock .. Knock can you save my data?
Confidential Copyright IBM Corporation 2004
IBM Global Services
Some Database Security Measures
Database Connections Public and Private Key Security Server Security Table Access Control
Digital Signatures as Passwords
Database
Dynamic Page Generation
Session Security User-Authentication Security Vendor-Specific Security Kerberos
Secure Sockets Layer (SSL) and S-HTTP
Confidential Copyright IBM Corporation 2004
IBM Global Services
Huh !!
The rabbit is on the way .. but is it secured enough ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
Network Security
Protection of networks and their services from unauthorized modification, destruction, or disclosure, and provision of assurance that the network performs its critical functions correctly and there are no harmful sideeffects. Network security includes data integrity .
Confidential Copyright IBM Corporation 2004
IBM Global Services
Lets identify the rabbits dangers on the road ..
Confidential Copyright IBM Corporation 2004
IBM Global Services
The Rabbits gift could have been stolen , destroyed by any other animal / stranger on the road To safeguard 1 . The rabbit could hide 2. The rabbit could run faster 3 . The rabbit could fool them etc
Lets see in our network world .
Confidential Copyright IBM Corporation 2004
IBM Global Services
Common security attacks and their countermeasures
Finding a way into the network Firewalls Exploiting software bugs, buffer overflows Intrusion Detection Systems Denial of Service Ingress filtering, IDS TCP hijacking IPSec Packet sniffing Encryption (SSH, SSL, HTTPS) Social problems Education
Confidential Copyright IBM Corporation 2004
IBM Global Services
Attacks on Different Layers
IP Attacks ICMP Attacks Routing Attacks Session Hijacking Application Layer Attacks
Confidential Copyright IBM Corporation 2004
IBM Global Services
Visualize imagine you realize
Confidential Copyright IBM Corporation 2004
IBM Global Services
Web and Network Security Threats
Web Security Threats
Network Security Threats
Confidential Copyright IBM Corporation 2004
IBM Global Services
Is there anyone who can save me?
Confidential Copyright IBM Corporation 2004
IBM Global Services
Network Security Safeguards
Firewall Certificate Digital Cert
Port Scan Proxy
Router
Spam Blocker
Encryption IDS
Antivirus Access Control Monitoring
Corporate Network
Confidential Copyright IBM Corporation 2004
IBM Global Services
SAP world and security
Confidential Copyright IBM Corporation 2004
IBM Global Services
Different Layer of Security With SAP Application
NETWORK SECURITY
WORKSTATION SECURITY SAP APPLICATION SECURITY
O/S SECURITY
DATABASE SECURITY
Confidential Copyright IBM Corporation 2004
IBM Global Services
Security in an integrated system like SAP tries to achieve the following.
Authentication - Only legitimate users should be able to access the system Authorization - Users should only be able to perform their designated tasks Integrity Privacy Obligation - Data integrity needs to be granted at all time - Protection of data against unauthorised access - Ensuring liability and legal obligation towards stakeholders and shareholders including validation
Confidential Copyright IBM Corporation 2004
SAP Product Overview
Confidential Copyright IBM Corporation 2004
IBM Global Services
Objectives
Introduction to SAP Netweaver What is ? Netweaver Stack Introduction Netweaver breakdown SOA
Confidential Copyright IBM Corporation 2004
IBM Global Services
SAP Product Introduction - History
The 1970s: A Real-Time Vision
In 1972, five former IBM employees -- Dietmar Hopp, Hans-Werner Hector, Hasso Plattner, Klaus Tschira, and Claus Wellenreuther -- launch a company called Systems, Applications, and Products Their vision: to develop standard application software for real-time business processing. One year later, the first financial accounting software "R/1 system is complete." "R" stands for real-time data processing. By the end of the decade, intensive examination of SAP's IBM database and dialog control system leads to the birth of SAP R/2.
Confidential Copyright IBM Corporation 2004
IBM Global Services
continued
The 1980s: Rapid Growth
The SAP R/2 system attains the high level of stability Keeping in mind its multinational customers, SAP designs SAP R/2 to handle different languages and currencies. With the founding of subsidiaries in Denmark, Sweden, Italy, and the United States, SAP's international expansion takes a leap forward.
Confidential Copyright IBM Corporation 2004
IBM Global Services
continued
The 1990s: A New Approach to Software and Solutions
SAP R/3 is unleashed on the market. The client-server concept, uniform appearance of graphical interfaces, consistent use of relational databases, and the ability to run on computers from different vendors meets with overwhelming approval. With SAP R/3, SAP ushers in a new generation of enterprise software -- from mainframe computing to the three-tier architecture of database, application, and user interface.
Confidential Copyright IBM Corporation 2004
IBM Global Services
continued
The 2000s: Innovation for the New Millennium
With the Internet, the user becomes the focus of software applications. SAP develops mySAP Workplace and paves the way for the idea of an enterprise portal and rolespecific access to information. By 2005, 12 million users work each day with SAP solutions 100,600 installations worldwide more than 1,500 partners over 25 industry-specific business solutions more than 33,200 customers in 120 countries SAP Netweaver developed based on Services-Oriented Architecture (SOA) Companies can integrate people, information, and processes within the company and beyond.
Confidential Copyright IBM Corporation 2004
IBM Global Services
What is SOA ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
SOA
Software architecture that defines the use of loosely coupled software services to support the requirements of business processes and software users
Resources on a network in an SOA environment are made available as independent services that can be accessed without knowledge of their underlying platform implementation
SOA-based systems can therefore be independent of development technologies and platforms (such as Java, .NET etc)
Confidential Copyright IBM Corporation 2004
IBM Global Services
Now let us take a look at some technical & operational challenges facing a distributed system
Confidential Copyright IBM Corporation 2004
IBM Global Services
SAP NetWeaver
Confidential Copyright IBM Corporation 2004
IBM Global Services
How to address the integration challenge ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
SAP NetWeaver
SAP NetWeaver integrates various different technological concepts and previous platforms in a single solution It is an open technology platform which offers a comprehensive set of technologies that are natively integrated
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration
Multi-Channel Access
Portal
Collaboration
People Integration brings together the right functionality and the right information to the right people
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration Portal Sample View
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration -- Portal
Multi-Channel Access
Portal
Collaboration
The portal is the Web front-end component for SAP NetWeaver
It is a personalized, interactive gateway, providing employees, partners, suppliers and customers with a single point of access. The key capabilities of the portal within SAP NetWeaver are as follows:
Heterogeneous information integration Administrator & EUS User management & Security support Personalization Ready-to-deploy business packages Delegated administration
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration Multi-Channel Access
Multi-Channel Access
Portal
Collaboration
With multi-channel access, you can connect to enterprise systems through voice, mobile, or radio-frequency technology Multi-channel access is delivered through Mobile Infrastructure The key elements of SAP NetWeavers multi-channel access capabilities are SAP NetWeaver Mobile,
SAP Auto-ID Infrastructure
SAP NetWeaver Voice, Message Interfaces (SMS, Fax, Email) and Web-based GUI
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration Multi-Channel Access
NetWeaver Mobile comprises of various technical architectures used for enabling end-toend mobile business solutions targeting specific user roles and device platforms
SAP Auto-ID Infrastructure connects RFID data directly from auto-ID data-capture sources, such as RFID readers, and integrates high-volume data directly into enterprise applications in real-time
SAP NetWeaver provides standardized interfaces to link 3rd party communication management applications with business applications. It enables the integration of fax, sms or email Web-based GUI enables end-users to gain access to their enterprise business via a Browser or Java User Interface SAP NetWeaver Voice makes business processes accessible by any telephone, any time. Users can interact with SAP backend systems using speech recognition or touch tones. It is currently not part of a standard SAP NetWeaver shipment.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver People Integration Collaboration
Multi-Channel Access
Portal
Collaboration
The collaboration capabilities delivered with SAP NetWeaver, are designed to enable individuals, teams, and interest groups to work together closely towards a common goal. The comprehensive set of collaboration tools and services allows users to share relevant information, communicate online in real-time, plan with the help of a unified calendar, and provide a single point of access to documents and resources.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Information Integration
Business Intelligence
Knowledge Management
Master Data Management
Information Integration makes both structured and unstructured information available in the enterprise in a consistent and accessible manner Users demand ubiquitous access to information wherever it resides. That information must be served in a consistent manner and its integrity guaranteed
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Information Integration Business Intelligence
Business Intelligence
Knowledge Management
Master Data Management
Business Intelligence in NetWeaver is composed of the following parts:
Data warehousing, which forms the application-neutral foundation for Business Intelligence. SAP BW supports the complete data warehousing process, from data integration, data transformation, consolidation and cleansing to data provision for analysis.
A business intelligence platform that serves as the technological infrastructure to support information access and comprehensive analytics. Business intelligence suite that transforms data into insightful information and serves a wide variety of users for decision-making.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Information Integration Knowledge Management
Business Intelligence
Knowledge Management
Master Data Management
Knowledge Management (KM) is the umbrella term for the management of unstructured information that is, all kinds of documents The Knowledge Management (KM) capabilities of SAP NetWeaver turn unstructured information into organizational knowledge an essential function in this age of global e-business The business challenge is to transform unstructured information into organizational knowledge by structuring and classifying it in such a way that it becomes assessable and relevant to the enterprise's knowledge workers There is an urgent need to create a central point of access within the enterprise to manage information and translate it into knowledge for success
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Information Integration Master Data Management
Business Intelligence
Knowledge Management
Master Data Management
Today, companies operating within heterogeneous IT landscapes are commonplace, and the demand for streamlining communication within such an environment is great. SAP Master Data Management (SAP MDM) - a key capability of SAP NetWeaver - enables information integrity across the business network. It enables companies to store, augment, and consolidate master data, while ensuring consistent distribution to all applications and systems within the IT landscape. It leverages existing IT investments in business-critical data, delivering vastly reduced data maintenance costs through effective data management. By ensuring cross-system data consistency, SAP MDM accelerates the execution of business processes, greatly improves decision-making and helps companies maintain their competitive advantage.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Process Integration
Integration Broker
Business Process Management
Process Integration enables business processes to run seamlessly across heterogeneous IT landscapes. Integration broker -- This capability enables XML/SOAP-based communication between application components from various sources and vendors. It also enables you to define software components, interfaces, mappings, and content-based routing rules. This capability is delivered through SAP Exchange Infrastructure (XI) Business process management -- With business process management, you can model and drive processes in a dynamic IT environment. It allows you to combine underlying applications into adaptive, end-to-end processes spanning the entire value chain.
|
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Process Integration -- XI
Integration Broker
Business Process Management
SAP NetWeaver Exchange Infrastructure: Provides a technical infrastructure for XML-based message exchange in order to connect SAP components with each other, as well as with non-SAP components Delivers business-process and integration knowledge to the customer, in the form of SAPs predefined integration scenarios Provides an integrated toolset for building new integration scenarios by defining and maintaining all integration-relevant information ("shared collaboration knowledge")
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Process Integration Business Process Management
Integration Broker
Business Process Management
BPM has three focuses to cater: Collaboration Tasks, which is part of the Enterprise Portal Framework, to enable individuals to create light-weight ad hoc process to optimize their day-to-day tasks and add transparency to what they are doing in relation to their colleagues. This is what delivers the people empowerment. SAP Business workflow, embedded within the SAP Web Application Server, which is used to automate the business processes taking place within an SAP component and integrate the SAP users with the business processes. This is what delivers the workflow empowerment within the mySAP components. Cross-Component BPM, which is part of SAP Exchange Infrastructure, drives and controls complex business processes across business applications and enterprise boundaries This delivers the total Business Process Empowerment in a heterogeneous system landscape.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Application Platform
J2EE
ABAP
DB and OS Abstraction
The application platform of SAP NetWeaver is the SAP Web Application Server
It provides a complete infrastructure to develop, deploy and run platformindependent, robust and scalable Web Services and business applications. To allow this flexibility, different technologies have been established
Java 2 Platform Enterprise Edition (J2EE) ABAP DB and OS Abstraction
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Application Platform SAP WAS
SAP Web Application Server (SAP Web AS) is the application platform of SAP NetWeaver, i.e. it provides the complete infrastructure to develop, deploy and run all SAP NetWeaver applications. The major key capability of SAP Web AS is the full support for both the proven ABAP technology and the innovative open source internet-driven technologies Java, Java 2 Enterprise Edition (J2EE) and Web Services.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Application Platform ABAP
ABAP is the SAP Web Application Server programming language for business applications It contains all characteristics of an object-oriented programming language and at the same time provides the benefits of a 4GL language: Many functions that are located in libraries in other languages are contained as language elements, which make it easier to check statistics and is beneficial for program performance.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Application Platform DB & OS Abstraction
Using the SAP Web Application Server, you can develop applications regardless of the underlying OS. Using OpenSQL, you can develop applications that run immediately on a given set of databases. With Web Dynpro you can develop user interfaces that run on a given set of web browsers. With MCOD (multiple components in one database), SAP provides the option to deploy several independent SAP components in one database without compromising flexibility.
With SAP DB, SAP has its own DB platform offering. SAP DB is an enterprise open source database designed for easy and simple administration and providing very low total costs of ownership.
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Application Platform Composite Application Framework
Composite Application Framework (CAF)
Composites aim at enabling efficient development of new applications that are easily adopted by customers, and allow flexibility in backend connectivity The key characteristics of composite applications are: - Model-driven architecture - Reuse of existing assets - Loose coupling to backend systems - Adaptive user-centric process flow and user interfaces Among the main features that SAP CAF provides are: - Support for the three layers of a composite application (services, user interfaces, and processes) - Patterns and templates at all three levels to increase development efficiency and application homogeneity - Model- and code-generation-based methods using tools that store models in a proprietary metamodel repository
Confidential Copyright IBM Corporation 2004
IBM Global Services
Questions ?
Confidential Copyright IBM Corporation 2004
Introduction to SAP Product Security
Confidential Copyright IBM Corporation 2004
IBM Global Services
Objectives
Why security & implications ? What types of security ? NetWeaver Security
Confidential Copyright IBM Corporation 2004
IBM Global Services
Perfect Security ?
There is no perfect security Needs to evolve with changing technologies & associated risks Risk to a security attack can be minimized
Confidential Copyright IBM Corporation 2004
IBM Global Services
Why is Security necessary ?
With the increasing use of distributed systems and the Internet for managing business data, the demands on security are also on the rise.
When using a distributed system, you need to be sure that your data and processes support your business needs without allowing unauthorized access to critical information.
User errors, negligence, or attempted manipulation on your system should not result in loss of information or processing time. These demands on security apply likewise to the SAP NetWeaver platform.
Confidential Copyright IBM Corporation 2004
IBM Global Services
What to protect ?
There are various aspects to consider while considering the answer to the above In the SAP environment, we should be able to reduce the risk of a security attack in the entire NetWeaver stack Broadly, we are looking at reducing security risks to the following NetWeaver layers: People Integration Process Integration Information Integration Application Platform
Confidential Copyright IBM Corporation 2004
IBM Global Services
People Integration Security Risks ?
Multi-Channel Access
Portal
Collaboration
People Integration brings together the right functionality and the right information to the right people. This module of the NetWeaver stack aims at providing seamless user experience, boundless collaboration functionality, and pervasive access. This functionality of this module of the NetWeaver stack is further broken down into: Portal Infrastructure Collaboration Multi-Channel Access We will investigate the security aspects to be considered for the above subcomponents in forth coming slides.
|
Confidential Copyright IBM Corporation 2004
IBM Global Services
NetWeaver Portal Security
The SAP NetWeaver Portal offers users a single point of access to all applications, information, and services needed to accomplish their daily tasks. Links to back-end and legacy applications, selfservice applications, company intranet services, and Internet services are all readily available in the users portal. Because the borders between company intranets and the Internet are blurring, comprehensive security is vital to protect the companys business.
Below are the aspects to consider while aiming to secure enterprise portal:
User administration & Authentication Authorizations Network & Communication Security Data Storage Security Operating System Security
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security - User Administration & Authentication
This section covers: User Management Authentication Integration Into Single Sign-On Environments
Confidential Copyright IBM Corporation 2004
IBM Global Services
User Management
The SAP NetWeaver Portal uses the User Management Engine (UME) for user management.
The UME can be configured to work with user management data from multiple data sources, for example, an LDAP directory, database of the SAP NetWeaver Application Server (AS) Java, or ABAP system.
The UME is integrated as a service of the Java AS.
Confidential Copyright IBM Corporation 2004
IBM Global Services
User Management Engine (UME)
What is the User Management Engine ?
Confidential Copyright IBM Corporation 2004
IBM Global Services
User Management Engine (UME)
The User Management Engine (UME) provides a centralized user management for all Java applications. It can be configured to work with user management data from multiple data sources. It is seamlessly integrated in the SAP NetWeaver Application Server (AS) Java as its default user store and can be administrated using the administration tools of the AS Java. In the figure, user data is stored in one or more data sources. Each type of data source has its own persistence adapter. The persistence manager consults the persistence adapters when creating, reading, writing, and searching user management data. The application programming interface (API) is a layer on top of the persistence manager. In the persistence manager, you configure which data is written to or read from which data source, so that the applications using the API do not have to know any details about where user management data is stored.
|
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security - Authentication
Authentication provides a way of verifying the users identity before he or she is granted access to the portal.
Several authentication mechanisms exist, some detailed below:
-
Basic authentication (Userid & Password) Client Certificates Single Sign-on Single Sign-On with Logon Tickets Single Sign-On with User-id & Password
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication Basic Authentication
Basic Authentication is an HTTP standard method to use for authentication, whereby the user provides a user ID and password for authentication.
SAP J2EE Engine uses Basic Authentication for applications that are set up to use basic or form authentication.
When using basic authentication, the users information is passed to the server over the HTTP connection in a header variable as a base-64 encoded string. When using form-based authentication, the information is passed in the URL as an URL parameter. Since the above is not very secure, the user of SSL to secure is recommended which then converts a HTTP request to HTTPS.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication - Client Certificates
In addition to using SSL for encrypting connections, you can use SSL and X.509 client certificates for authenticating client or user access requests to the J2EE Engine.
When using client certificates, authentication takes places transparently for the user with the underlying SSL security protocol. Therefore, you can use authentication with client certificates to integrate the J2EE Engine in a Single Sign-On environment.
Users need to receive their client certificates from a Certification Authority (CA) as part of a public-key infrastructure (PKI). If you do not have an established PKI then you can use a Trust Center Service to obtain certificates.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication Single Sign-On (SSO)
SSO is a key feature of the SAP NetWeaver Portal that eases user interaction with the many component systems available to the user in a portal environment. Once the user is authenticated to the portal, he or she can use the portal to access external applications. With SSO in the portal, the user can access different systems and applications without having to repeatedly enter his or her user information for authentication. The portal SSO mechanism is available in the following variants depending on security requirements and the supported external applications:
-
SSO with logon tickets SSO with user ID and password
Both variants eliminate the need for repeated logons to individual applications after the initial authentication at the portal. Whereas SSO with logon tickets is based on a secure ticketing mechanism, SSO with user ID and password forwards the users logon data (user ID and password) to the systems that a user wants to call.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication Single Sign-On (SSO)
Single Sign-On With Login Tickets
Logon tickets represent the user credentials. The portal server issues a logon ticket to a user after successful initial authentication The logon ticket itself is stored as a cookie on the client and is sent with each request of that client. It can then be used by external applications such as SAP systems to authenticate the portal user to
those external applications without any further user logons being required.
Logon tickets contain information about the authenticated user. They do not contain any passwords. Specifically, logon tickets contain the following items:
-
Portal user ID and one mapped user ID for external applications Authentication scheme Validity period Information identifying the issuing system Digital signature
When using logon tickets, one system must be the ticket-issuing system. This can either be the portal or another system.
|
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication Single Sign-On
Single Sign-On With Userid & Password The Single Sign-On (SSO) mechanism with user name and password provides an alternative for applications that cannot accept and verify logon tickets. With this SSO mechanism the portal server uses user mapping information provided by users or administrators to give the portal user access to external systems. ] The portal components connect to the external system with the users credentials. Since the system sends the user's logon ID and password across the network, use a secure protocol such as Secure Sockets Layer (SSL) for sending data.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security - Authorization
Authorizations define which objects users can access and which actions they can perform. The portal has an authorization concept that is implemented using the following concepts:
Permissions Security Zones UME Actions AuthRequirement property
Portal permissions define portal user access rights to portal objects in the PCD and are based on access control list (ACL) methodology. Security Zones Control which portal components and portal services users can launch and are defined in the development phase. UME Actions the User Management Engine (UME) equivalent of portal permissions. The UME verifies that users have the appropriate UME actions assigned to them before granting them access to UME iViews and functions. AuthRequirement property This is a master iView property used in EP 5.0 that defines which users are authorized to access a master iView or Java iViews derived from a master iView.
|
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Authentication Portal Roles
In the SAP NetWeaver Portal, roles are only indirectly linked to authorization. Portal roles group together the portal content required by users with a certain role in the company. In addition, the role structure defines the navigation structure that a user sees in the portal. Users and groups assigned to a role inherit the permissions of the role. By default this is end user permission.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Portal Security Network & Communication Security
The portal is dependent on the NetWeaver Application Server for Java for network communication.
SAP systems are implemented as client-server frameworks built in three levels: database server level, application server level and the presentation level (front ends).
The servers are the most vulnerable part of the network infrastructure and special care should be taken to protect them from unauthorized access
Confidential Copyright IBM Corporation 2004
IBM Global Services
Collaboration Security
SAP Collaboration allows access to company-internal personal data, information, and documents that may not be equally accessible to all portal users. Settings for data security prevent unauthorized access and data manipulation. Collaboration uses the user management and user authentication mechanisms in the SAP NetWeaver platform, in particular those in the SAP Web Application Server (Java). Therefore, the security recommendations and guidelines for user management and authentication apply as described in the SAP Web Application Server security guide. Collaboration uses the permissions concept provided by the SAP Web Application Server (Java). Therefore, the security recommendations and guidelines for permissions apply as described in the SAP Web Application Server (Java) security guide.
This permissions concept is based on roles that are valid throughout the portal, which are assigned to the users.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Multi-Channel Access Security
With multi-channel access, you can connect to enterprise systems through voice, mobile, or radio-frequency technology.
Multi-channel access is delivered through Mobile Infrastructure.
The mobile device is threatened by the following potential dangers:
-
Loss of the device Theft Unauthorized use by an unauthorized person Data manipulation in the file system
Authentication & Authorization procedures are discussed in the next few slides
Confidential Copyright IBM Corporation 2004
IBM Global Services
Mobile Infrastructure Authentication
The user management of the SAP MI Client Component manages user IDs and local logon passwords. The local logon password is used for local user authentication. It is stored in coded form on the mobile device, and not in plain text. The number of possible failed attempts can be restricted. A second password, called the synchronization password, is used for synchronization with the SAP MI Server Component (SAP NetWeaver AS).
You can change the passwords on the client side at any time. The data can, however, only be synchronized successfully if the user ID and synchronization password for the client have counterparts on the server. Users can change both passwords with the SAP MI Client Component
Confidential Copyright IBM Corporation 2004
IBM Global Services
Mobile Infrastructure Authentication
Authentication Using System Logon (Bypassing Local SAP MI Logon) For mobile devices with only one user you can configure the device in such a way that the user does not have to logon with the local logon password. The start page of the SAP MI Client Component appears immediately as soon as the mobile device is started. Where this is the case, the user must be able to identify him- or herself on the operating system. Where this is the case, the user must be able to identify him- or herself on the operating system.
The authentication on the operating system is not technically linked to the SAP MI Client Component. It is a conceptual, organizational prerequisite for working with the SAP MI Client Component.
When the user synchronizes with the SAP MI Server Component he or she has to use the synchronization password. You cannot use this bypass option in conjunction with the handling option local for the synchronization password. This results in a configuration conflict.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Mobile Infrastructure - Authentication
Authentication with Single Sign-On You can configure the SAP MI Client Component to support single sign-on (SSO) if the device is available with an online connection. The SSO technology is based on the SAP logon tickets. The mobile device receives the SAP logon ticket from a system that issues tickets, such as SAP Enterprise Portal. The mobile device can then be verified at the SAP MI Server Component with the SAP logon ticket without the user having to enter an additional password
Confidential Copyright IBM Corporation 2004
IBM Global Services
Mobile Infrastructure - Authorization
The security recommendations and guidelines for authorizations described in the SAP NetWeaver Application Server Security Guide also apply, therefore, to SAP MI.
The authorization concept of the SAP NetWeaver AS is based on the assignment of authorizations to users on the basis of roles. Use the profile generator (transaction PFCG) for role maintenance on SAP NetWeaver AS ABAP and the user administration console from the User Management Engine on SAP NetWeaver AS Java. Access to data and applications on the SAP MI Client Component is controlled by userspecific data filtering based on the SAP authorization concept.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Mobile Infrastructure Securing the Communication Channel
There are 2 communication paths to secure:
-
From the SAP MI Client Component to the SAP NetWeaver AS ABAP and vice versa Protocols include HTTP,SSL or HTTPS Data transferred includes application data, control data for SAP Mobile Infrastructure, synchronization password Data requiring particular protection includes synchronization password, as it is copied from the mobile device to the SAP NetWeaver AS ABAP with each HTTP request. Use of SSL or HTTPS is recommended
From SAP NetWeaver AS ABAP to back-end system and vice versa Protocols include RFC Data type includes application data
Confidential Copyright IBM Corporation 2004
IBM Global Services
Information Integration- Security Risks ?
Information Integration makes both structured and unstructured information available in the enterprise in a consistent and accessible manner. Users demand ubiquitous access to information wherever it resides. That information must be served in a consistent manner and its integrity guaranteed.
Security risk revolve around ensuring the integrity of data
Confidential Copyright IBM Corporation 2004
IBM Global Services
Business Information Warehouse Security
Why Is Security Necessary? SAP NetWeaver BI serves to integrate, transform, and consolidate data from all areas of an enterprise in order to provide this for analysis, interpretation and distribution. This includes confidential corporate data, for example, personal data from Personnel Administration. Decisions are made in all enterprise areas and target-oriented actions are determined on the basis of this data. For this reason, security when accessing data and the ability to guarantee data integrity is of great importance. The following examples show the dangers to which BI can be exposed:
-
Attacks from the Internet or Intranet when using BEx Web functionality and Web Services Infringement of data protection guidelines through unauthorized access to personal data
Confidential Copyright IBM Corporation 2004
IBM Global Services
BI Security - Authentication
The authentication process enables the identity of a user to be checked before this user gains access to BI or BI data. SAP NetWeaver supports various authentication mechanisms. Some of the authentication mechanisms include:
-
Single Sign-On (SSO) Client Certificates SAP Logon Tickets
Single sign-on implies that once a user is authenticated with a username & password, the user then has access to other SAP systems that are in the landscape As an alternative to user authentication using a user ID and passwords, users using Internet applications via the Internet Transaction Server (ITS) can also provide X.509 client certificates. In this case, user authentication is performed on the Web Server using the Secure Sockets Layer Protocol (SSL Protocol) and no passwords have to be transferred. User authorizations are valid in accordance with the authorization concept in the SAP system. BI supports SAP logon tickets. To make Single Sign-On available for several systems, users can issue an SAP logon ticket after they have logged on to the SAP system. The ticket can then be submitted to other systems (SAP or external systems) as an authentication token. The user does not need to enter a user ID or password for authentication but can access the system directly after the system has checked the logon ticket.
Confidential Copyright IBM Corporation 2004
IBM Global Services
BI Security - Authorization
An authorization allows a user to perform a certain activity on a certain object in the BI System. There are two different concepts for this depending on the role and tasks of the user: Standard Authorizations
-
These authorizations are required by all users that are working in the Data Warehousing Workbench to model or load data, and also by users that work in the planning workbench or the Analysis Process Designer and those that work with the Reporting Agent or the BEx Broadcaster or define queries.
Analysis Authorizations.
-
All users that want to display transaction data from authorization-relevant characteristics in a query require analysis authorizations for these characteristics.
Confidential Copyright IBM Corporation 2004
IBM Global Services
Knowledge Management (KM) Security
The KM security aspects deal with preventing illegal access to documents and settings and prevent them being manipulated illegally.
Security in KM is achieved by implementing one or more of the following measures:
-
Roles ACLs Security Zones
Roles are of 3 types:
-
Content Manager allows users to structure & manage content System Administrator allows user to perform KM administration Content Administrator allows user to perform KM specific content administration
Confidential Copyright IBM Corporation 2004
IBM Global Services
Knowledge Management (KM) Security
Restricting access permissions only by using the role concept or worksets is not sufficient. The use ACLs is recommended.
-
Access permissions on the root nodes of security-relevant repositories should be restricted immediately after the installation or after configuring new repository managers in order to prevent documents being read illegally by users hacking or guessing document URLs. Change the ACLs for subordinate folders if different permissions apply for these folders.
Security zones
-
Security zones restrict unauthorized direct access to KM content For initial KM content, the required permissions in the security zones are already assigned during installation of SAP NetWeaver.
Confidential Copyright IBM Corporation 2004
IBM Global Services
KM Security - Communication Channel Security
Various channels of communication and technologies are used between the components and data sources in Knowledge Management.
The following technologies are used for communication:
-
HTTP/HTTPS WebDAV ICE JDBC on OpenSQL Operation-system-dependent and database-specific technologies
Confidential Copyright IBM Corporation 2004
IBM Global Services
Process Integration Security Risks ?
Why Is Security Necessary? As the central infrastructure for exchanging business documents, PI has to make sure that the involved processes can be executed in a secure manner. Particular security requirements have to be considered if business partners communicate over the Internet. XML messages may contain confidential business data. In order to protect them against eavesdropping and unauthorized access, the communication lines as well as the storage locations of XML messages need to be made secure. In addition to the business data exchanged using PI, the various components of PI need to communicate with each other on a technical level in order to keep the infrastructure running. Security requirements apply to these technical communications as well, because confidential information such as user names and passwords may have to be sent or stored, or both.
Confidential Copyright IBM Corporation 2004
IBM Global Services
PI Security - Communication
The components of a process integration (PI) landscape communicate with each other for different purposes like configuration, administration, monitoring, or the actual messaging. The primary purpose of a PI landscape is to enable business partners and applications to exchange XML messages (business documents). This includes business communication between business systems, Integration Servers or Adapter Engines.
In addition to proper messaging, technical communication between various PI tools and runtime components is required.
Two different technical protocols are used for these communications: HTTP and RFC.
Confidential Copyright IBM Corporation 2004
IBM Global Services
PI Security - Authentication
Session-based single sign-on is supported for the dialog users of the PI tools. A dialog user has to log on only once for all PI tools, provided that the same browser session is used for each tool access, and that the tools are started from the same SAP NetWeaver Application Server Java. Single sign-on is also supported by the Runtime Workbench where access to other PI components is required (for example, for component monitoring).
Confidential Copyright IBM Corporation 2004
IBM Global Services
PI Security Message Level Security
Message-level security allows you to digitally sign or encrypt documents exchanged between systems or business partners. It improves communication-level security by adding security features that are particularly important for inter-enterprise communication. Message-level security is recommended and sometimes a prerequisite for inter-enterprise communication. Certificate Store
-
Message-level security processing is generally done in SAP NetWeaver Application Server Java (AS-Java). If the Integration Server executes security processing, a Web service is called in the J2EE Engine. Therefore, the certificates as well as the certification authority (CA) certificates to be used must be entered into the keystore of the J2EE Engine that executes the security handling at runtime.
Archiving Secured Messages - For non-repudiation purposes, signed messages are stored in a dedicated archive, the nonrepudiation archive. It contains data to prove the validity of the signature. The following data is stored:
The raw message The security policy as configured in the Integration Directory The sender certificate
Confidential Copyright IBM Corporation 2004
IBM Global Services
Questions ?
Confidential Copyright IBM Corporation 2004
Das könnte Ihnen auch gefallen
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (400)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (345)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- SAP SD Interview QuestionsDokument9 SeitenSAP SD Interview Questionskrishna_koduruNoch keine Bewertungen
- SAP HANA Master Guide enDokument72 SeitenSAP HANA Master Guide enkrishna_koduruNoch keine Bewertungen
- MySQL Tutorial - KDokument14 SeitenMySQL Tutorial - Kkrishna_koduru0% (1)
- How Indian Communists Are Destroying by Russian CommunistsDokument1 SeiteHow Indian Communists Are Destroying by Russian Communistskrishna_koduruNoch keine Bewertungen
- SAP GUI Hand OutDokument41 SeitenSAP GUI Hand Outkrishna_koduruNoch keine Bewertungen
- Special Status Benefits For APDokument4 SeitenSpecial Status Benefits For APkrishna_koduruNoch keine Bewertungen
- Item 4: An Example On How To Decide Which Reports Should Be in R/3 or The Legacy SystemDokument2 SeitenItem 4: An Example On How To Decide Which Reports Should Be in R/3 or The Legacy Systemkrishna_koduruNoch keine Bewertungen
- AnRak AluminiumDokument5 SeitenAnRak Aluminiumkrishna_koduruNoch keine Bewertungen
- List of SAP MM Transaction CodesDokument4 SeitenList of SAP MM Transaction Codescoolrobin000% (1)
- Nielsen Survey - APDokument1 SeiteNielsen Survey - APkrishna_koduruNoch keine Bewertungen
- SAP Security - Day 1 1st Half - AnwarDokument112 SeitenSAP Security - Day 1 1st Half - AnwarRajiv BaghelNoch keine Bewertungen
- List of SAP MM Transaction CodesDokument4 SeitenList of SAP MM Transaction Codescoolrobin000% (1)