Beruflich Dokumente
Kultur Dokumente
Auditing and Internal Control Report
Hochgeladen von
Teofel John Alvizo Pantaleon0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
32 Ansichten34 Seitenby Miss Shaireen Rojas
Copyright
© © All Rights Reserved
Verfügbare Formate
PPTX, PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument meldenby Miss Shaireen Rojas
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PPTX, PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
32 Ansichten34 SeitenAuditing and Internal Control Report
Hochgeladen von
Teofel John Alvizo Pantaleonby Miss Shaireen Rojas
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PPTX, PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 34
isa systematic process of objectively
obtaining and evaluating evidence regarding
assertions about economic actions and events
to ascertain the degree of correspondence
between those assertions and establishing
criteria and communicating the results to
interested users.
Information technology (IT) developments
have had tremendous impact on auditing.
Business organizations undergo different
types of audits for different purposes.
Business organizations undergo different
types of audits for different purposes.
Independent attestation performed by an
expert (i.e., CPA) who expresses an opinion
regarding the fair presentation of financial
statements known as the attest service.
Required by SEC for all public companies.
Key concept is independence:
Similar to a trial by judge
Auditor collects evidence and renders opinion.
Basis of public confidence in financial
statements.
Strict rules must be followed.
Defined by SEC, FASB, AICPA and SOX.
ATTEST SERVICE
o An engagement in which a practitioner is
engaged to issue, or does issue, a written
communication that expresses a conclusion
about the reliability of a written assertion
that is the responsibility of another party.
o Requirements of attestation services:
o Written assertions and practitioner’s written report.
o Formal establishment of measurement criteria.
o Limited to examination, review, and application of
agreedupon procedures.
ADVISORY SERVICES
A professional service offered by public
accounting firms to improve their client’s
organizations’ operational effectiveness and
efficiency.
SOX greatly restricts the types of non-audit
services auditors may render to audit clients.
Unlawful to provide many accounting, financial,
internal audit, management, human resource or
legal services unrelated to the audit.
isan independent appraisal function to
examine and evaluate activities within, and as
a service to, an organization. (IIA)
Internal auditors perform a wide variety of
activities including financial, operational,
compliance and fraud audits.
Auditors may work for the organization or task
maybe outsourced. (CIA/CISA)
Independence is self-imposed, but auditors
represent the interests of the organization.
The standards, guidance & certification of
internal audits are governed by IIA & ISACA
External auditors represent outsiders while
internal auditors represent organization’s
interests.
Internal auditors often cooperate with and assist
external auditors in some aspects of financial
audits.
Extent of cooperation depends upon the
independence and competence of the internal audit
staff.
Externalauditors can rely in part on evidence
gathered by internal audit departments that are
organizationally independent and report to the
board of directors’ audit committee.
Recent increase in popularity as a corporate
governance tool.
Objective of Fraud Audit
to investigate anomalies and gather evidence of
fraud that may lead to criminal convictions.
May be initiated by management who suspect
employee fraud or the board of directors who
suspect executive fraud.
Fraud Auditors have earned the Certified Fraud
Examiner (CFE) certificatio governed by the
Association of Certified Fraud Examiners (ACFE)
Subcommittee of the board of directors
Usually three members who are outsiders.
SOX requires at least one member must be a
“financial expert”.
Serves as independent “check and balance” for
the internal audit function and liason with
external auditors.
SOX mandates that external auditors report to
the audit committee:
Committee hires and fires auditors and resolve
disputes.
To be effective, they must be willing to challenge
the internal auditors as well as management.
Its role is to identify risks
In general, it becomes an independent guardian
of the entity’s assets.
Corporate frauds have some bearings of audit
committee failures
Lack of independence, Inactive audit committee,
total absence of audit committee, and lack of
experienced members.
Three classes of auditing standards:
general qualification, field work, and reporting.
Specific
guidance provided by AICPA Statements
on Auditing Standards (SASs) as authoritative
interpretations of GAAS.
First one issued in 1972.
If recommendations are not followed, auditor must be
able to show why a SAS does not apply to a given
situation.
SASs - often referred as Auditing standards and
regarded as authoritative pronouncements
Conducing an audit is a systematic and logical
process that applies to all forms of information
systems.
Theauditors determines the fairness of FS and
establishes audit objectives, designs
procedures, and gathers evidence based on
these assertions:
Existence or Occurence
Completeness
Rights and Obligations
Valuation or Allocation
Presentation or Disclosure
Auditormust determine whether internal
control weaknesses and misstatements are
material.
Auditors seek evidential matter that
corroborates assertions.
Auditors must communicate the results of
their tests, including an audit opinion.
Evidence is collected by:
Performing test of controls
Performing substantive tests
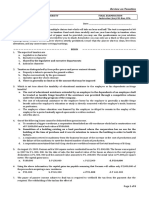
Probability that auditor will render unqualified
(clean) opinion on financial statements that are,
in fact, materially misstated.
The auditor’s objective is to achieve a level of
audit risk that is acceptable to the auditor.
Inherent risk (IR) is associated with unique
characteristics of client’s business or industry.
Control risk (CR) is the likelihood the control
structure is flawed because controls are either
absent or inadequate to prevent or detect errors.
Detection risk (DR) is the risk auditors are willing to
take that errors not detected or prevented by the
control structure will not be detected by the
auditor.
Audit risk components in a model used to
determine the scope, nature and timing of
substantive tests:
Audit risk model: AR = IR x CR x DR
If acceptable audit risk is 5%, the planned detection
risk will depend upon the control structure.
The stronger the internal control structure, the
lower the control risk and the less substantive
testing the auditor must do.
Substantive tests are labor intensive and time
consuming, which drives up audit costs and cause
disruption.
Management’s best interests are served by a strong
internal control structure.
Focuses on computer-based aspects of an
organization’s information system; modern systems
employ significant levels of technology.
First step is audit planning which includes the
analysis of audit risk.
Techniques for gathering evidence include questionnaires,
management interviews, reviewing system documentation and
observing activities.
Objective of tests of controls is to determine if
adequate controls are in place and functioning.
Third phase focuses on financial data and a detailed
investigation of specific account balances and
transactions through substantive tests.
Files may be extracted using Computer-Assisted-Audit Tools
and Techniques (CAATTs) software.
Management required by law to establish and
maintain adequate system of internal controls.
An important management obligation.
Brief history of internal control legislation:
SEC Acts of 1933 and 1934.
Copyright Law of 1976.
Foreign Corrupt Practices (FCPA) of 1977 requires
companies registered with the SEC to:
Keep records that fairly and reasonably reflect firm’s
transactions and financial position.
Maintain a system of internal control that provides reasonable
assurance that organization objectives are met.
Committee of Sponsoring Organizations - 1992
Sarbanes-Oxley Act of 2002 (SOX) requires management of
public companies to implement adequate internal control
system over their financial reporting process. Under
Section 302:
Managers must certify organization’s internal controls
quarterly and annually.
External auditors must perform certain procedures
quarterly to identify any material control modifications
that may impact financial reporting.
Section404 requires management of public
companies to access the effectiveness of their
internal controls in an annual report.
Internal
control system comprises policies,
practices, and procedures to achieve four
broad objectives:
Safeguard assets of the firm.
Ensure accuracy and reliability of accounting
records and information.
Promote efficiency in the firm’s operations.
Measure compliance with management’s
prescribed policies and procedures.
Management responsibility made law by SOX.
Objectives should be achieved regardless of the
data processing method used.
Every system has limitations on its effectiveness
including: possibility of error, circumvention,
management override and changing conditions.
System should provide reasonable assurance that
broad objectives are met.
Cost to achieve improved control should not
outweigh benefits.
Cost of correcting material weaknesses is offset by
benefits.
Preventive controls are passive techniques designed
to reduce frequency of undesirable events
occurring.
More cost effective than detecting and correcting
problems after they occur.
Detective controls are devices, techniques and
procedures to identify and expose undesirable
events that eluded the preventive controls.
Corrective controls fix the identified problem.
Thecontrol environment is the foundation for
the other four control components and includes:
Management integrity and ethical values,
organizational structure, board of director
participation and management’s philosophy and
operating style.
A risk assessment must be performed to identify,
analyze and manage financial reporting risks.
An effective accounting information system will:
Identify and record all valid financial transactions,
provide timely information and adequately measure
and record transactions.
Monitoring is the process by which the quality of
internal control design and operation can be
assessed.
Control activities are policies and procedures to
ensure actions to deal with identified risk.
Physical controls relate primarily to human
activities employed in accounting systems.
Information technology controls.
Transactionauthorization is to ensure all
processed transactions are valid.
May be general (sales only to authorized customer) or
specific (extending the credit limit of a customer).
Segregation of duties is designed to:
Separate transaction authorization from processing.
Separate asset custody from recordkeeping.
Ensure a successful fraud requires collusion between
individuals with incompatible responsibilities.
Supervisionis a compensating control for small
organizations that cannot achieve adequate
segregation of duties.
Accounting records are source documents, journals
and ledgers that provide an audit trail.
Information needed for day to day operations and essential
in the financial audit process.
Access controls ensure only authorized personnel
have assess to firm’s assets.
Verification procedures are independent checks to
identify errors and misrepresentations in the
accounting system.
Management can assess the performance of individuals,
the integrity of the transaction processing system, and
data correctness.
Applicationcontrols ensure validity,
completeness, and accuracy of financial
transactions.
Includes check digits, batch balancing and payroll limits.
General controls apply to all systems and
include:
IT governance, IT infrastructure, security and access to
operating systems and databases, application acquisition
and development and program change procedures.
General controls needed to support functioning
of application controls. Both needed to ensure
accurate financial reporting.
Expanded role of auditors:
Must attest to quality of client organization’s internal
controls with a separate audit opinion.
Possible to render a qualified opinion on controls and
an unqualified opinion on financial statements.
PCAOB Standard No. 5 requires auditors to
understand:
Transaction flows including controls pertaining to how
transactions are initiated, authorized, recorded, and
reported.
Auditors responsible for detecting fraudulent
activity.
Das könnte Ihnen auch gefallen
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (894)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (265)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- Estate Tax LectureDokument7 SeitenEstate Tax LectureVanilyn LaresmaNoch keine Bewertungen
- Accounting For Franchise (PFRS 15) HandoutsDokument3 SeitenAccounting For Franchise (PFRS 15) HandoutsTeofel John Alvizo Pantaleon100% (3)
- Forces of Fantasy (1ed)Dokument127 SeitenForces of Fantasy (1ed)Strogg100% (7)
- Pakistani Companies and Their CSR ActivitiesDokument15 SeitenPakistani Companies and Their CSR ActivitiesTayyaba Ehtisham100% (1)
- Arabic Letters Practice WorksheetsDokument3 SeitenArabic Letters Practice Worksheetsvinsensius soneyNoch keine Bewertungen
- Source Document-WPS OfficeDokument2 SeitenSource Document-WPS OfficeTeofel John Alvizo PantaleonNoch keine Bewertungen
- Horizontal AnalysisDokument3 SeitenHorizontal AnalysisTeofel John Alvizo Pantaleon0% (1)
- Opinion) Train-Wps OfficeDokument2 SeitenOpinion) Train-Wps OfficeTeofel John Alvizo PantaleonNoch keine Bewertungen
- Position With Job Description and QualificationsDokument8 SeitenPosition With Job Description and QualificationsTeofel John Alvizo PantaleonNoch keine Bewertungen
- AFAR PracDokument13 SeitenAFAR PracTeofel John Alvizo PantaleonNoch keine Bewertungen
- IFRS 1 - First-Time Adoption of International Financial Reporting StandardsDokument49 SeitenIFRS 1 - First-Time Adoption of International Financial Reporting StandardsTeofel John Alvizo PantaleonNoch keine Bewertungen
- Module 24 - Government Grants: Iasc Foundation: Training Material For The Ifrs For SmesDokument32 SeitenModule 24 - Government Grants: Iasc Foundation: Training Material For The Ifrs For SmesTeofel John Alvizo PantaleonNoch keine Bewertungen
- Social Accounting Research PaperDokument38 SeitenSocial Accounting Research PaperTeofel John Alvizo PantaleonNoch keine Bewertungen
- Internal Control Audit QuestionsDokument10 SeitenInternal Control Audit QuestionsTeofel John Alvizo Pantaleon100% (1)
- Solution To Comprehensive ProblemDokument7 SeitenSolution To Comprehensive ProblemEJ LagatNoch keine Bewertungen
- Management Advisory Services – Review QuizDokument14 SeitenManagement Advisory Services – Review QuizTeofel John Alvizo PantaleonNoch keine Bewertungen
- IFRS 8 - Operating Segments: Date Development CommentsDokument11 SeitenIFRS 8 - Operating Segments: Date Development CommentsTeofel John Alvizo PantaleonNoch keine Bewertungen
- IFRS 1 - First-Time Adoption of International Financial Reporting StandardsDokument49 SeitenIFRS 1 - First-Time Adoption of International Financial Reporting StandardsTeofel John Alvizo PantaleonNoch keine Bewertungen
- IFRS 8 - Operating Segments: Date Development CommentsDokument11 SeitenIFRS 8 - Operating Segments: Date Development CommentsTeofel John Alvizo PantaleonNoch keine Bewertungen
- Theory of Accounts Review DIY DrillDokument6 SeitenTheory of Accounts Review DIY DrillxinfamousxNoch keine Bewertungen
- Arens - Chapter14 AuditingDokument39 SeitenArens - Chapter14 AuditingtableroofNoch keine Bewertungen
- Commercial Law – Negotiable InstrumentsDokument29 SeitenCommercial Law – Negotiable InstrumentsTeofel John Alvizo PantaleonNoch keine Bewertungen
- IAS 2: InventoriesDokument6 SeitenIAS 2: InventoriescolleenyuNoch keine Bewertungen
- FS Analysis Ans KeyDokument5 SeitenFS Analysis Ans KeyTeofel John Alvizo PantaleonNoch keine Bewertungen
- At-030507 - Auditing in A CIS EnvironmentDokument15 SeitenAt-030507 - Auditing in A CIS EnvironmentRandy Sioson100% (9)
- Synthesis 1 - MCIADokument3 SeitenSynthesis 1 - MCIATeofel John Alvizo PantaleonNoch keine Bewertungen
- Audit of Cash and Bank BalancesDokument14 SeitenAudit of Cash and Bank Balanceshxn1421Noch keine Bewertungen
- Mactan-Cebu International Airport Terminal 2 To Open in JulyDokument5 SeitenMactan-Cebu International Airport Terminal 2 To Open in JulyTeofel John Alvizo PantaleonNoch keine Bewertungen
- Investment Committee CharterDokument5 SeitenInvestment Committee CharterTeofel John Alvizo PantaleonNoch keine Bewertungen
- Tax Review - FinalsDokument8 SeitenTax Review - FinalsRobert Castillo100% (2)
- 2018 PICPA Research ConferenceDokument4 Seiten2018 PICPA Research ConferenceTeofel John Alvizo PantaleonNoch keine Bewertungen
- The Secret - How Two Regular Students Topped The Civil Engineers Board ExamDokument8 SeitenThe Secret - How Two Regular Students Topped The Civil Engineers Board ExamTeofel John Alvizo PantaleonNoch keine Bewertungen
- How To Pass The CPA Board ExamDokument4 SeitenHow To Pass The CPA Board ExamTeofel John Alvizo PantaleonNoch keine Bewertungen
- Aqua Golden Mississippi Tbk Company Report and Share Price AnalysisDokument3 SeitenAqua Golden Mississippi Tbk Company Report and Share Price AnalysisJandri Zhen TomasoaNoch keine Bewertungen
- The Indian Navy - Inet (Officers)Dokument3 SeitenThe Indian Navy - Inet (Officers)ANKIT KUMARNoch keine Bewertungen
- Aclc College of Tacloban Tacloban CityDokument3 SeitenAclc College of Tacloban Tacloban Cityjumel delunaNoch keine Bewertungen
- LTD NotesDokument2 SeitenLTD NotesDenis Andrew T. FloresNoch keine Bewertungen
- The Emergence of Provincial PoliticsDokument367 SeitenThe Emergence of Provincial PoliticsHari Madhavan Krishna KumarNoch keine Bewertungen
- The University of Chicago PressDokument19 SeitenThe University of Chicago PressNikola TatalovićNoch keine Bewertungen
- Quiz 2Dokument2 SeitenQuiz 2claire juarezNoch keine Bewertungen
- FinTech BoguraDokument22 SeitenFinTech BoguraMeraj TalukderNoch keine Bewertungen
- Entrance English Test for Graduate Management StudiesDokument6 SeitenEntrance English Test for Graduate Management StudiesPhương Linh TrươngNoch keine Bewertungen
- Service Culture Module 2Dokument2 SeitenService Culture Module 2Cedrick SedaNoch keine Bewertungen
- Russian Revolution History Grade 9 NotesDokument6 SeitenRussian Revolution History Grade 9 NotesYesha ShahNoch keine Bewertungen
- Mind Map All in One PBA-2021-08-20 12-38-51Dokument1 SeiteMind Map All in One PBA-2021-08-20 12-38-51MikosamirNoch keine Bewertungen
- 6 Lee VS PPDokument2 Seiten6 Lee VS PPSarah De GuzmanNoch keine Bewertungen
- RA MEWP 0003 Dec 2011Dokument3 SeitenRA MEWP 0003 Dec 2011Anup George Thomas100% (1)
- Gender, Race, and Semicolonialism: Liu Na'ou's Urban Shanghai LandscapeDokument24 SeitenGender, Race, and Semicolonialism: Liu Na'ou's Urban Shanghai Landscapebaiqian liuNoch keine Bewertungen
- How To Become A Hacker - Haibo WuDokument281 SeitenHow To Become A Hacker - Haibo WuAlex de OliveiraNoch keine Bewertungen
- Advanced Customer Service: Presented by Amgad Salah Senior Customer ServicesDokument45 SeitenAdvanced Customer Service: Presented by Amgad Salah Senior Customer ServiceslovemagicNoch keine Bewertungen
- Problematika Pengembangan Kurikulum Di Lembaga Pendidikan Islam: Tinjauan EpistimologiDokument11 SeitenProblematika Pengembangan Kurikulum Di Lembaga Pendidikan Islam: Tinjauan EpistimologiAhdanzulNoch keine Bewertungen
- Battle of BadrDokument1 SeiteBattle of BadrAreeba QureshiNoch keine Bewertungen
- The Meaning of Life Without Parole - Rough Draft 1Dokument4 SeitenThe Meaning of Life Without Parole - Rough Draft 1api-504422093Noch keine Bewertungen
- Business and Transfer Taxation Chapter 11 Discussion Questions AnswerDokument3 SeitenBusiness and Transfer Taxation Chapter 11 Discussion Questions AnswerKarla Faye LagangNoch keine Bewertungen
- Anthony VixayoDokument2 SeitenAnthony Vixayoapi-533975078Noch keine Bewertungen
- BusLaw Chapter 1Dokument4 SeitenBusLaw Chapter 1ElleNoch keine Bewertungen
- Connotation Words Reading Kelompok 3Dokument11 SeitenConnotation Words Reading Kelompok 3Burhanudin Habib EffendiNoch keine Bewertungen
- People of The Philippines vs. OrsalDokument17 SeitenPeople of The Philippines vs. OrsalKTNoch keine Bewertungen
- The Slow Frog An Intraday Trading Strategy: A Rules Based Intra-Day Trading Strategy (Ver 1.0)Dokument17 SeitenThe Slow Frog An Intraday Trading Strategy: A Rules Based Intra-Day Trading Strategy (Ver 1.0)ticman123Noch keine Bewertungen
- ECC Ruling on Permanent Disability Benefits OverturnedDokument2 SeitenECC Ruling on Permanent Disability Benefits OverturnedmeymeyNoch keine Bewertungen