Beruflich Dokumente
Kultur Dokumente
802 11
Hochgeladen von
aditi0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
16 Ansichten76 Seiten802.12 it is
Originaltitel
802.11
Copyright
© © All Rights Reserved
Verfügbare Formate
PPTX, PDF, TXT oder online auf Scribd lesen
Dieses Dokument teilen
Dokument teilen oder einbetten
Stufen Sie dieses Dokument als nützlich ein?
Sind diese Inhalte unangemessen?
Dieses Dokument melden802.12 it is
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PPTX, PDF, TXT herunterladen oder online auf Scribd lesen
0 Bewertungen0% fanden dieses Dokument nützlich (0 Abstimmungen)
16 Ansichten76 Seiten802 11
Hochgeladen von
aditi802.12 it is
Copyright:
© All Rights Reserved
Verfügbare Formate
Als PPTX, PDF, TXT herunterladen oder online auf Scribd lesen
Sie sind auf Seite 1von 76
Unit IV :
Introduction, Requirements of Wireless LAN
Advantages and Disadvantages of IR LAN and Radio
Transmissions
IEEE802.11 Architecture and Services, Bluetooth
Architecture , Bluetooth Security, Bluetooth Protocols.
Infrared
Infrared systems (IR systems) are simple in design and
therefore inexpensive.
They use the same signal frequencies used on fiber
optic links.
IR systems detect only the amplitude of the signal and
so interference is greatly reduced.
These systems are not bandwidth limited and thus can
achieve transmission speeds greater than the other
systems.
Infrared transmission operates in the light spectrum
and does not require a license from the FCC to operate.
Wireless LAN technology is based on IEEE 802.11 standard.
Its predecessor the IEEE 802.3, commonly referred to as
the Ethernet, is the most widely deployed member of the
family.
IEEE 802.11 is commonly referred to as wireless Ethernet
because of its close similarity with the IEEE 802.3.
Like IEEE 802.3, it also defines only two bottom levels of
ISO’s open system Interconnection (OSI) model
As it shares the upper layers with other LAN standards, it
is relatively easy to bridge the IEEE 802.11 wireless LANs to
other IEEE 802.11 wired LANs to form an extended
interconnected wired and wireless LAN network.
IEEE 802.11 networks consist of four major
components :
Stations: Stations are computing devices with wireless
network interfaces. Typically, stations are battery-
operated laptop or handheld pocket PCs.
Access points: Frames on an 802.11 network must be
converted to another type of frame for delivery to a
wired network. Devices called access points (AP)
perform the wireless to-wired bridging function.
Wireless medium: To move frames from station to
station, the standard uses a wireless medium. Typical
WLANs utilize an RF physical layer.
Distribution system :
When several APs are connected to form a large coverage area,
they must communicate with each other to handle the
movements of mobile stations. The distribution system (DS) is
the logical component of 802.11 used to forward frames to their
destination.
Usually, the DS is implemented as a combination of a bridging
engine and a distribution system medium, which is the
backbone network used to relay frames between APs. In most
cases, Ethernet is used as the backbone network technology.
Most APs operate as bridges. They have at least one wireless
network interface and at least one Ethernet network interface.
The Ethernet side can be connected to an existing network, and
the wireless side becomes an extension of that network.
IEEE 802.11 standard defines two kinds of services:
The Basic Service Set (BSS)
Extended Service Set (ESS) [
The BSS is the basic building block of a wireless LAN.
A BSS consists of stationary or mobile wireless stations
and possibly a central base station (e.g., an AP).
When a station is in the BSS, it can communicate with
the other members of the BSS.
The BSS without an AP is a stand-alone network and
cannot send data to other BSSs.
Such BSSs are called Independent BSSs (IBSS).
Typically, IBSSs involve a small number of stations set
up for a specific purpose and for a short period of time
(e.g.,creating a short-lived network to support a single
meeting in a conference room).
IBSSs are also referred to as ad hoc networks.
Infrastructure BSSs are distinguished from ad hoc
networks by the use of an AP.
APs are used for all communications in an
infrastructure BSS, including communication between
mobile nodes in the same service set.
An infrastructure BSS is bounded by the coverage
distance from the AP. The coverage area of a single AP
is called acell.
All mobile stations are required to be within reach of
the AP.
802.11 allows wireless networks of arbitrarily large size
to be created by linking BSSs into an ESS.
An ESS is created by chaining BSSs together with a
backbone network.
All the Aps in an ESS are given the same Service Set
Identier (SSID), which serves as a network name for its
users.
APs in an ESS operate in a manner such that the
outside world can use the station's MAC address to
talk to a station without worrying about its location in
the ESS.
Figure 4 shows three BSSs corresponding to three APs.
There is an equal level of overlap between BSS 1 and
BSS 2, and between BSS 2 and BSS 3.
Such overlap is necessary to provide stations with
seamless connectivity if they move from one BSS to
another.
In the figure, the router uses the station's MAC
address as the destination to deliver frames to a
station; only the AP with which that station is
associated delivers the frame.
Usually, mobility support is the primary motivation for
deploying an 802.11 network.
IEEE 802.11 allows mobility between BSSs at the link
layer.
However, it is not aware of anything that happens
above the link layer.
When stations move between BSSs, they will find and
attempt to associate with an AP with the strongest
signal and the least network traffic.
This way, a mobile station can transition seamlessly
from one AP in the network to another, without losing
connectivity. This event is often referred to as roaming.
IEEE 802.11 Framing
Frame control: The frame control is 2 bytes long and
defines the type of the frame and control information.
The subfields in the frame control field are as follows:
Protocol version: Indicates which version of 802.11
MAC is contained in the rest
of the frame. Only one version of the 802.11 MAC has
been developed: it has been assigned a protocol
number of 0.
Type: Defines the type of information carried in the
frame body: management
(00), control (01), or data (10).
Subtype: Defines the subtype of each management,
control, or data frame.
ToDS: This bit is set to 1 if the frame was sent to the DS.
FromDS: This bit is set to 1 if the frame was sent from the
DS.
More fragments: When a higher-level packet has been
fragmented by the MAC, the initial fragment and any
following non-final fragments set this bit to 1.
Retry: The retry bit is set to 1 if the current packet is a
retransmission of a previous attempt. This aids the
receiving station in eliminating duplicate packets.
Power management: To conserve battery life, many small
devices have the ability to power down parts of the network
interface. A 1 indicates that the station will be in powersave
mode, and 0 indicates that the station will be active.
WEP: The Wired Equivalent Privacy (WEP) bit is set
to 1 if the payload of the packet has been encrypted
using the WEP algorithm.
Order: Frames and fragments can be transmitted in
any order by both the receiv-ing and sending stations.
The bit is set to 1 when the packets must be strictly
ordered.
Duration ID: The duration field is used to set the
Network Allocation Vector (NAV). NAV is used for
carrier sensing. The value represents the number of
microseconds that the medium is expected to remain
busy for the transmission currently in progress.
Address fields :There are four address elds, each 6
bytes long.
The meaning of each address field depends on the
value of the ToDS and the FromDS subfields as shown
in Table 2.
Address 1 is the address of the receiver of the frame.
Address 2 is the transmitter address.
Address 3 is the final destination station if it is not
defined by Address 1.
Address 4 is the address of the original source station
if it is not the same as Address 2.
Sequence control:
The sequence control field is composed of a 4-bit
fragment number and a 12-bit sequence number.
This field is used for defragmentation and discarding
duplicate frames.
Higher-level frames are each given a sequence number
as they are passed to the MAC layer for transmission.
Frame body :
The frame body moves the higher-layer payload from
station to station.
802.11 can transmit frames with a maximum payload of
2304 bytes of data.
Frame check sequence Similar to Ethernet, the 802.11
frame ends with a Frame Check Sequence (FCS), also
known as Cyclic Redundancy Check (CRC). The FCS
allows stations to check the integrity of received
frames.
IEEE 802.11 Services
IEEE 802.11 defines nine services that need to be
provided by the wireless LAN to provide functionality
1. The service provider can be either the station or the
distribution system (DS).
Station services are implemented in every 802.11 station,
including access
point (AP) stations.
Distribition services are provided between basic service
sets (BSSs); these services may be implemented in an AP.
2. Three of the services are used to control IEEE 802.11
LAN access and confidentiality.
Six of the services are used to support delivery of MAC
service data units (MSDUs) between stations. The MSDU is
a the block of data passeddown from the MAC user to the
MAC layer;
If the MSDU is too large to be transmitted in a single MAC
frame, it may befragmented and transmitted in a series of
MAC frames.
Distribution :
It is the primary service used by stations to exchange
MAC frames when the frame must traverse the DS to get
from a station in one BSS to a station in another BSS. For
example, suppose a frame is to be sent from station 2 (STA
2) to STA 7 .
The frame is sent from STA 2 to STA 1, which is the AP for
this BSS. The AP gives the frame to the DS, which has the
job of directing the frame to the AP associated with STA 5
in the target BSS.STA 5 receives the frame and forwards it
to STA 7.
If the two stations that are communicating are within the
same BSS, then the distribution service logically goes
through the single AP of that BSS.
The integration service enables transfer of data
between a station on an IEEE 802.11 LAN and a
station on an integrated IEEE 802.x LAN.
The term integrated refers to a wired LAN that is
physically connected to the DS and whose stations
may be logically connected to an IEEE 802.11 LAN via
the integration service.
To deliver a message within a DS, the distribution
service needs to know where the destination station is
located. To meet this requirement, a station must
maintain an association with the AP within its current
BSS. Three services relate to this requirement:
• Association: Establishes an initial association
between a station and an AP.
Before a station can transmit or receive frames on a
wireless LAN, its identity and address must be known.
For this purpose, a station must establish an
association with an AP within a particular BSS.
The AP can then communicate this information to
other APs within the ESS to facilitate routing and
delivery of addressed frames.
• Reassociation: Enables an established
association to be transferred from oneAP to
another, allowing a mobile station to move from one
BSS to another.
Disassociation: A notification from either a
station or an AP that an existing association is
terminated. A station should give this notification
before leaving an ESS or shutting down.
Access and Privacy Services
• Authentication:
Used to establish the identity of stations to each
other.
IEEE 802.11 supports several authentication schemes
and allows for expansion of the functionality of these
schemes.
The standard does not mandate any particular
authentication scheme, which could range from
relatively unsecure handshaking to public-key
encryption schemes.
• Deathentication: This service is invoked
whenever an existing authentication is to be
terminated.
• Privacy: Used to prevent the contents of
messages from being read by other than the
intended recipient.
The standard provides for the optional use of
encryption to assure privacy. The algorithm specified
in the standard is WEP,
The lower sublayer of the MAC layer is the distributed
coordination function (DCF). DCF uses a contention
algorithm to provide access to all traffic.
The point coordination function
(PCF) is a centralized MAC algorithm used to provide
contention-free service.
Distributed Coordination Function
The DCF sublayer makes use of a simple CSMA
(carrier sense multiple access) algorithm.
If a station has a MAC frame to transmit, it listens to
the medium.If the medium is idle, the station may
transmit; otherwise the station must wait until
the current transmission is complete before
transmitting.
The DCF does not include a collision detection
function (i.e., CSMA/CD) because collision detection
is not practical on a wireless network.
• SIFS (short IFS): The shortest IFS, used for all
immediate response actions.
• PIFS (point coordination function IFS): A
midlength IFS, used by the centralized controller in
the PCF scheme when issuing polls
• DIFS (distributed coordination function IFS):
The longest IFS, used as a minimum delay for
asynchronous frames contending for access
Point Coordination Function
PCF is an alternative access method implemented on top of
the DCF. The operation consists of polling by the
centralized polling master (point coordinator).
A wireless network is configured so that a number of
stations with time-sensitive traffic are controlled by the
point coordinator while remaining traffic contends for
access using CSMA.
The point coordinator could issue polls in a round-robin
fashion to all stations configured for polling. When a poll is
issued, the polled station may respond using SIFS. If the
point coordinator receives a response, it issues another poll
using PIFS.If no response is received during the expected
turnaround time, the coordinator issues a poll.
Bluetooth
What is Bluetooth?
Bluetooth is an open standard for short-range radio
frequency (RF) communication.
Bluetooth technology is used primarily to establish
wireless personal area networks (WPAN), commonly
referred to as ad hoc or peer-to-peer (P2P) networks.
Bluetooth is a low-cost, low-power technology that
provides a mechanism for creating small wireless
networks on an ad hoc basis
Where we can find it?
Bluetooth technology has been integrated into many types
of business and consumer devices,including:
Cellular phones
Personal digital assistants (PDA)
Laptops
Automobiles
Printers
Headsets
This allows users to form ad hoc networks between a wide
variety of devices to transfer voice and data.
Why do we need Bluetooth (keybenefits of Bluetooth
technology are):
Cable replacement.
Ease of file sharing.
Wireless synchronization.
Internet connectivity.
There are two types of topology for Bluetooth –
Piconet
Scatternet.
The Piconet is a small ad hoc network of devices (normally 8
stations)
It has the following features:
One is called Master and the others are called Slaves
All slave stations synchronizes their clocks with the master
Possible communication - One-to-one or one-to-many
There may be one station in parked state
Each piconet has a unique hopping pattern/ID
Each master can connect to 7 simultaneous or 200+ inactive
(parked) slaves per piconet
Scatternet is formed by combining several Piconets. Multiple
piconets with overlapping coverage areas form a scatternet. Each
piconet may have only one master, but slaves may participate in
different piconets
Key features of the scatternet topology are mentioned below:
A Scatternet is the linking of multiple co-located piconets
through the sharing of common master or slave devices.
A device can be both a master and a slave.
Radios are symmetric (same radio can be master or slave).
High capacity system, each piconet has maximum capacity
(720 Kbps)
Bluetooth Architecture
Layer 1: Radio Layer
This is the lowest layer in the Bluetooth protocol stack.
Bluetooth uses a technique called frequency hopping
in establishing radio links with other Bluetooth
devices.
Suppose we have a data packet then the whole packet
is never transmitted at the same frequency. It is always
split into different parts and transmitted at different
frequencies. This is the frequency hopping technique
This partly gives the necessary protection to the
transmitted data and avoids tampering.
Standard hop values are 79 hops, which are spaced at
an interval of 1 MHz.
Layer 2: Baseband Layer
The baseband is the digital engine of a Bluetooth system.
It is responsible for
constructing and decoding packets
encoding and managing error correction
encrypting and decrypting for secure communications
calculating radio transmission frequency patterns
maintaining synchronization, controlling the radio
all of the other low level details necessary to realize
Bluetooth communications.
Bluetooth operates in the 2.4 GHz ISM band. In the US and
Europe, a band of 83.5 MHz width is available; in this band,
79 RF channels spaced 1 MHz apart are defined.
Layer 3: Link Manager Protocol
The Link Manager is responsible for managing the
physical details for Bluetooth connections.
The Link Manager carries out link setup,
authentication, link configuration and other protocols.
It discovers other remote LM’s and communicates
with them via the Link Manager Protocol (LMP).
To perform its service provider role, the LM uses the
services of the underlying Link Controller (LC).
Layer 4: Host Controller Interface
This is the layer of the stack that contains the firmware
i.e. the software that actually controls all the activities
happening in the Baseband and Radio layers.
It provides a common interface between the Bluetooth
host and a Bluetooth module. It manages the hardware
links with the scatternets.
Logical Link Control and Adaptation Protocol
The Logical Link Control and Adaptation Layer
Protocol (L2CAP) is layered over the Baseband
Protocol and resides in the data link layer.
It manages the high level aspects of each connection
(who is connected to who, whether to use encryption
or not, what level of performance is required, etc.).
In addition it is responsible for converting the format
of data as necessary between the APIs and the lower
level Bluetooth protocols.
The L2CAP is implemented in software and can
execute either on the host system processor or on a
local processor in the Bluetooth system.
L2CAP provides connection oriented and
connectionless data services to upper layer protocols.
L2CAP permits higher-level protocols and applications
to transmit and receive L2CAP data packets up to 64
kilobytes in length.
Two link types are supported for the Baseband layer:
Synchronous Connection-Oriented (SCO) links and
Asynchronous Connection-Less (ACL) links.
SCO links support real-time voice traffic using
reserved bandwidth. ACL links support best effort
traffic.
Das könnte Ihnen auch gefallen
- Assignment 4 MWDokument11 SeitenAssignment 4 MWaditiNoch keine Bewertungen
- Bluetooth WLAN 4 PDFDokument43 SeitenBluetooth WLAN 4 PDFaditiNoch keine Bewertungen
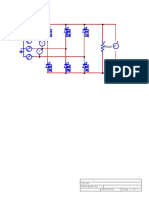
- FWCR ckt1 PDFDokument1 SeiteFWCR ckt1 PDFaditiNoch keine Bewertungen
- The Challenges of Wireless Communications in Developing A Virtual University P.M.PapazoglouDokument9 SeitenThe Challenges of Wireless Communications in Developing A Virtual University P.M.PapazoglouaditiNoch keine Bewertungen
- 802 11Dokument76 Seiten802 11aditiNoch keine Bewertungen
- The Yellow House: A Memoir (2019 National Book Award Winner)Von EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Bewertung: 4 von 5 Sternen4/5 (98)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceVon EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceBewertung: 4 von 5 Sternen4/5 (895)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeVon EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeBewertung: 4 von 5 Sternen4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingVon EverandThe Little Book of Hygge: Danish Secrets to Happy LivingBewertung: 3.5 von 5 Sternen3.5/5 (399)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaVon EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaBewertung: 4.5 von 5 Sternen4.5/5 (266)
- Shoe Dog: A Memoir by the Creator of NikeVon EverandShoe Dog: A Memoir by the Creator of NikeBewertung: 4.5 von 5 Sternen4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureVon EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureBewertung: 4.5 von 5 Sternen4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItVon EverandNever Split the Difference: Negotiating As If Your Life Depended On ItBewertung: 4.5 von 5 Sternen4.5/5 (838)
- Grit: The Power of Passion and PerseveranceVon EverandGrit: The Power of Passion and PerseveranceBewertung: 4 von 5 Sternen4/5 (588)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryVon EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryBewertung: 3.5 von 5 Sternen3.5/5 (231)
- The Emperor of All Maladies: A Biography of CancerVon EverandThe Emperor of All Maladies: A Biography of CancerBewertung: 4.5 von 5 Sternen4.5/5 (271)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyVon EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyBewertung: 3.5 von 5 Sternen3.5/5 (2259)
- On Fire: The (Burning) Case for a Green New DealVon EverandOn Fire: The (Burning) Case for a Green New DealBewertung: 4 von 5 Sternen4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersVon EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersBewertung: 4.5 von 5 Sternen4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnVon EverandTeam of Rivals: The Political Genius of Abraham LincolnBewertung: 4.5 von 5 Sternen4.5/5 (234)
- The Unwinding: An Inner History of the New AmericaVon EverandThe Unwinding: An Inner History of the New AmericaBewertung: 4 von 5 Sternen4/5 (45)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreVon EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreBewertung: 4 von 5 Sternen4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)Von EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Bewertung: 4.5 von 5 Sternen4.5/5 (121)
- Her Body and Other Parties: StoriesVon EverandHer Body and Other Parties: StoriesBewertung: 4 von 5 Sternen4/5 (821)
- Best Answer For Each Conversation. You Will Hear Each Conversation TwiceDokument4 SeitenBest Answer For Each Conversation. You Will Hear Each Conversation TwiceQuang Nam Ha0% (1)
- GSB (Coarse Graded) Summary Sheet: Physical PropertiesDokument10 SeitenGSB (Coarse Graded) Summary Sheet: Physical PropertiesjitendraNoch keine Bewertungen
- MotRadar System PrinciplesDokument26 SeitenMotRadar System PrinciplesReadmotNoch keine Bewertungen
- Cep Matlab CodeDokument5 SeitenCep Matlab CodeMuhammad FurqanNoch keine Bewertungen
- Proco Rat Distortion DIY SchemDokument1 SeiteProco Rat Distortion DIY SchemFer VazquezNoch keine Bewertungen
- PCBA-WP543HV HW Manual Rev1.05Dokument21 SeitenPCBA-WP543HV HW Manual Rev1.05Surapong Pongchaiprateep100% (1)
- 165 NebulizerDokument2 Seiten165 NebulizerLotfi BahriNoch keine Bewertungen
- E-Paper Technology DocumentDokument32 SeitenE-Paper Technology DocumentZuber Md54% (13)
- Installation, Operation, and Maintenance Manual: Ansi Process PumpDokument56 SeitenInstallation, Operation, and Maintenance Manual: Ansi Process Pumpfaundes100% (1)
- Urban Bus Spec IIDokument33 SeitenUrban Bus Spec IIBhawna SinghNoch keine Bewertungen
- Group B04 - MM2 - Pepper Spray Product LaunchDokument34 SeitenGroup B04 - MM2 - Pepper Spray Product LaunchBharatSubramonyNoch keine Bewertungen
- Usermanual en Manual Arium Bagtanks WH26010 ADokument33 SeitenUsermanual en Manual Arium Bagtanks WH26010 AԳոռ ԽաչատրյանNoch keine Bewertungen
- FraceDokument12 SeitenFraceIra MejiaNoch keine Bewertungen
- Jntu Hyderabad - 2010 Dec - 07a51404 Kinematicsofmachineryfr 3180Dokument10 SeitenJntu Hyderabad - 2010 Dec - 07a51404 Kinematicsofmachineryfr 3180bbkNoch keine Bewertungen
- Deep Sea Research Submarine Report PDFDokument128 SeitenDeep Sea Research Submarine Report PDFy_596688032Noch keine Bewertungen
- Performance of Trinidad Gas Reservoirs PDFDokument11 SeitenPerformance of Trinidad Gas Reservoirs PDFMarcus ChanNoch keine Bewertungen
- Logic Families and Their Characteristics CharacteristicsDokument26 SeitenLogic Families and Their Characteristics CharacteristicsanunilaNoch keine Bewertungen
- C QuestionsDokument22 SeitenC QuestionsSeethalam ManushaNoch keine Bewertungen
- Dn7064519 - Installing Flexi Cabinet For IndoorDokument63 SeitenDn7064519 - Installing Flexi Cabinet For Indoorlettymc100% (1)
- Dimetra Ip CompactDokument2 SeitenDimetra Ip CompactGrompolLopmorgNoch keine Bewertungen
- Collateral Document Management System: User'S ManualDokument10 SeitenCollateral Document Management System: User'S ManualGerard DGNoch keine Bewertungen
- West Point Partners Project - OverviewDokument11 SeitenWest Point Partners Project - OverviewhudsonvalleyreporterNoch keine Bewertungen
- Fundamentals and History of Cybernetics 2Dokument46 SeitenFundamentals and History of Cybernetics 2izzul_125z1419Noch keine Bewertungen
- Internship Opportunities PDFDokument2 SeitenInternship Opportunities PDFMD MoizNoch keine Bewertungen
- Industrial Visit Report OnDokument41 SeitenIndustrial Visit Report OnLalit SharmaNoch keine Bewertungen
- Philips Accent LightingDokument37 SeitenPhilips Accent LightingCecila Torrez BenitezNoch keine Bewertungen
- McGraw-Hill (Level 1) PDFDokument41 SeitenMcGraw-Hill (Level 1) PDFDarpan GajjarNoch keine Bewertungen
- NovaSeq X - Site PreparationDokument3 SeitenNovaSeq X - Site Preparationlifir67730Noch keine Bewertungen